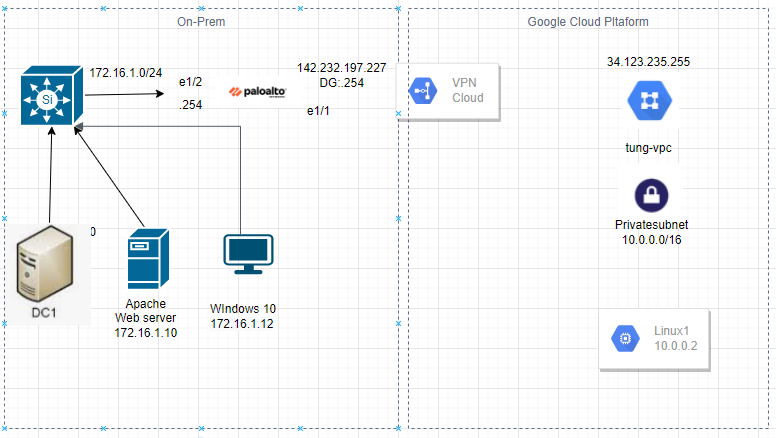
This is a diagram that I have used for the lab.
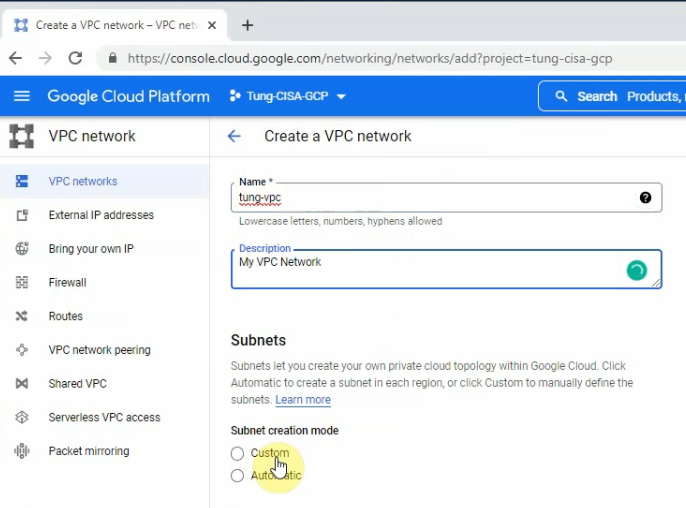
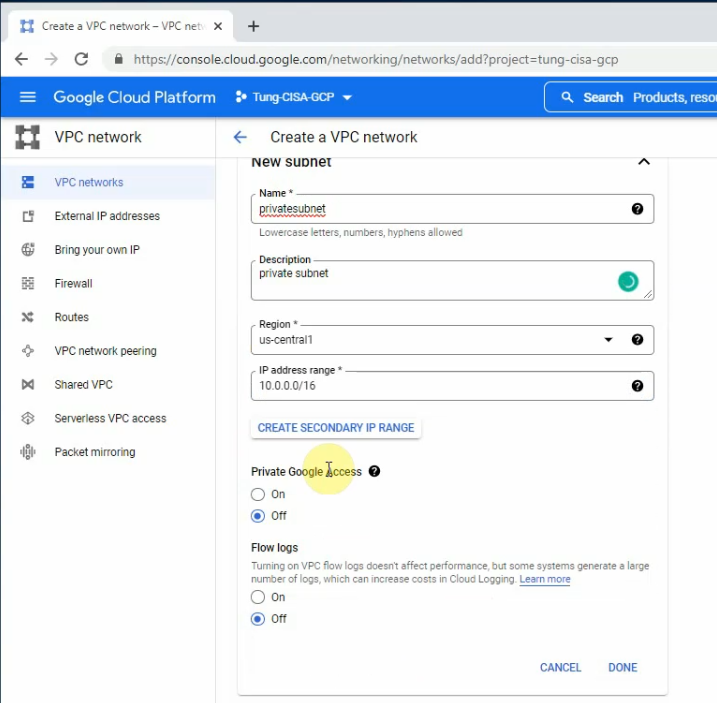
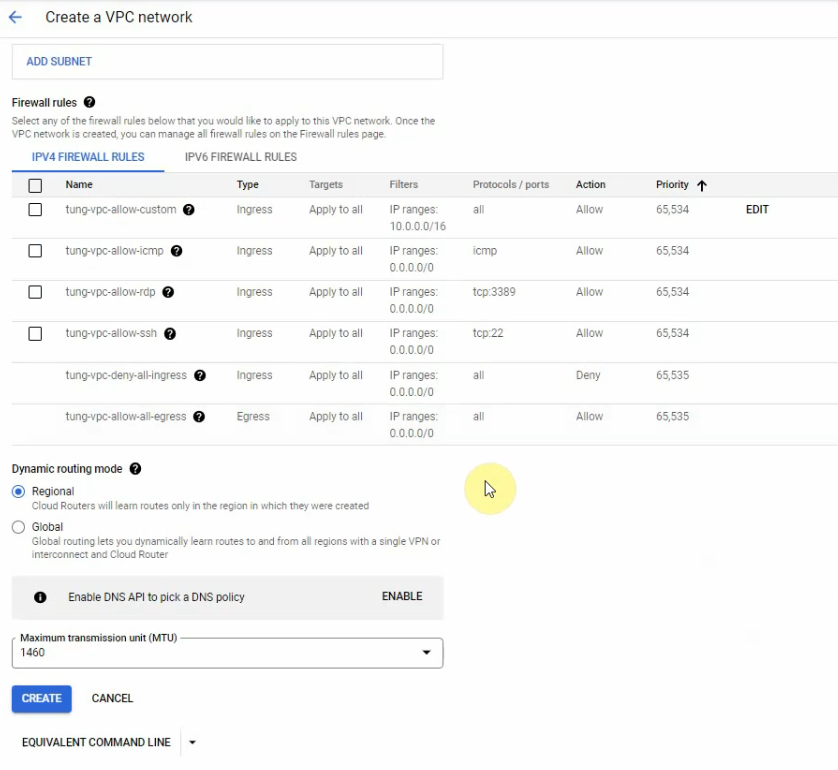
Create a new VPC network on GCP.
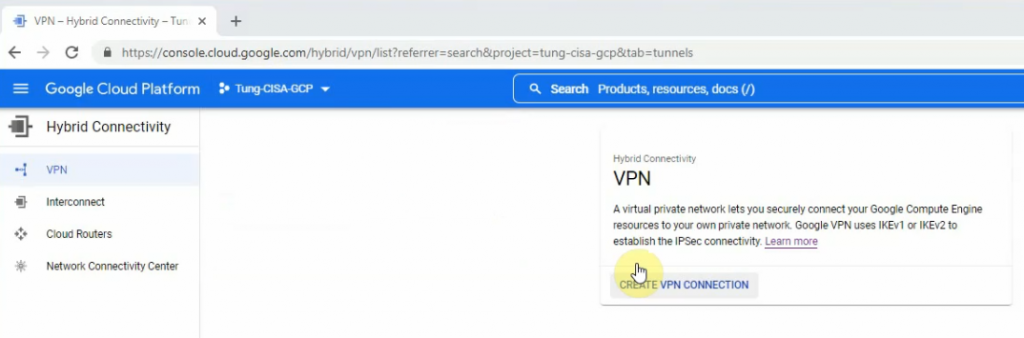
Search VPN keyword on the search function.
Click “Create VPN connection”.
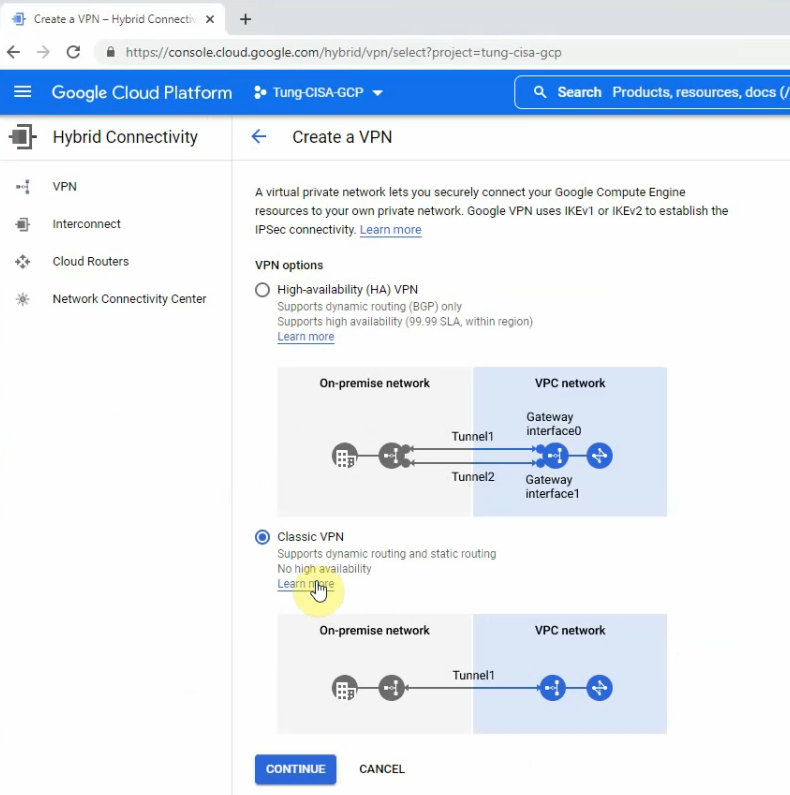
Select Classic VPN.
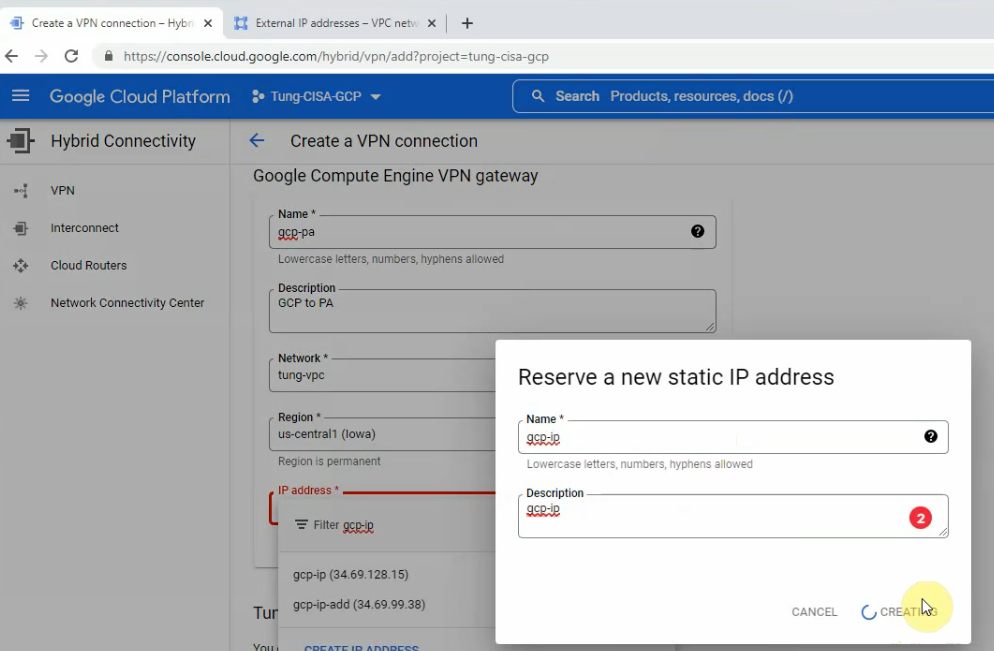
Select tung-vpc on the network setting.
Create a new static IP address for your VPC.
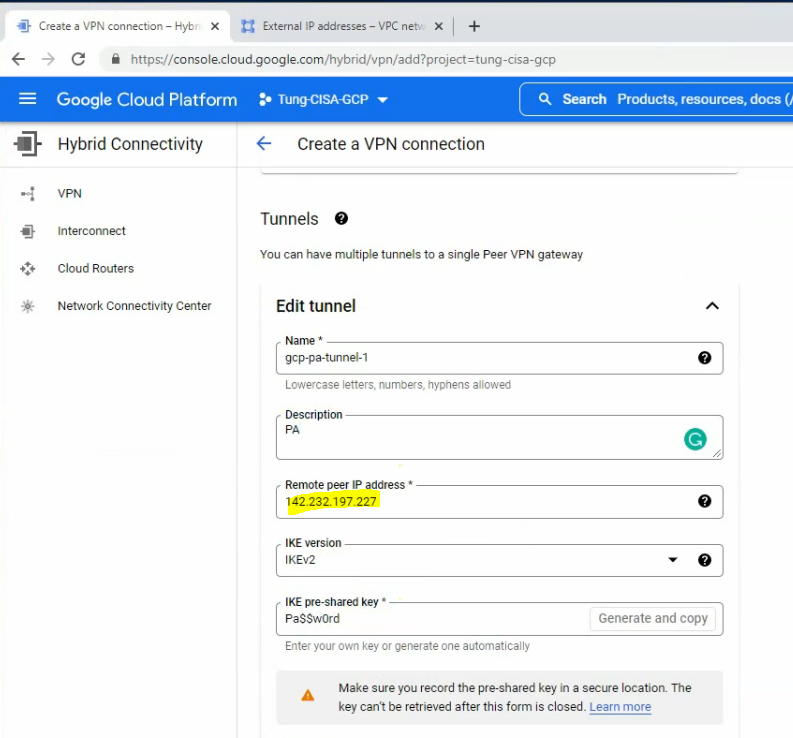
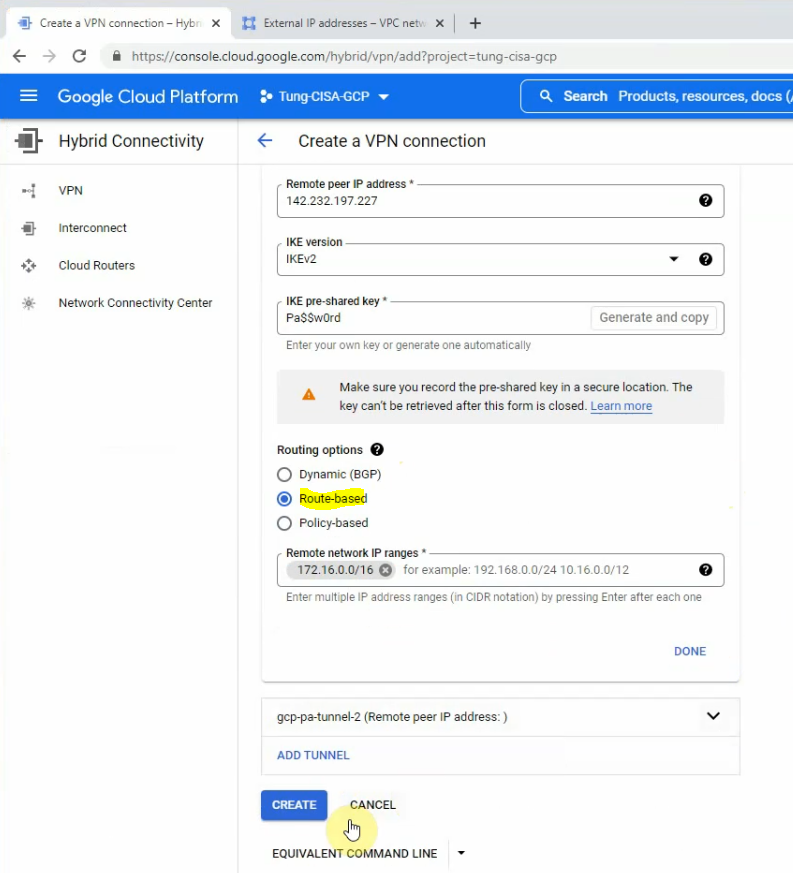
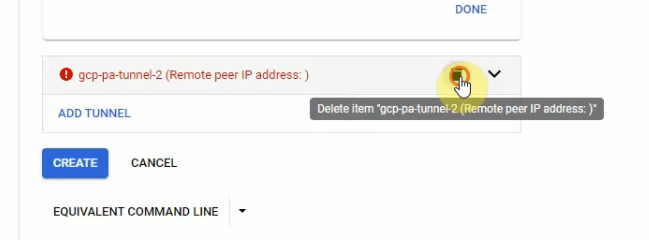
Delete tunnel 2 because I have only used tunnel 1 in this lab. Then click Create.
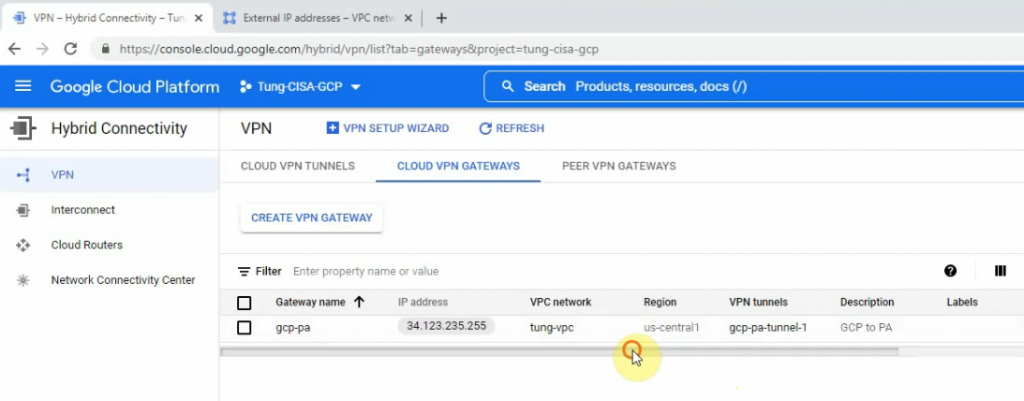
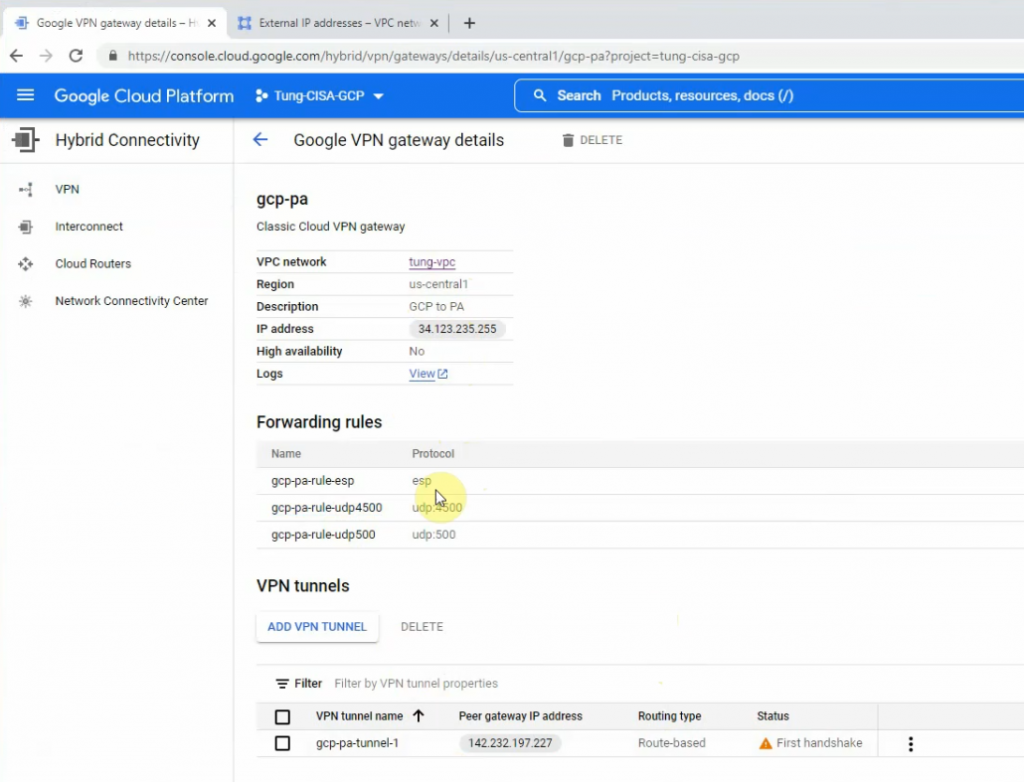
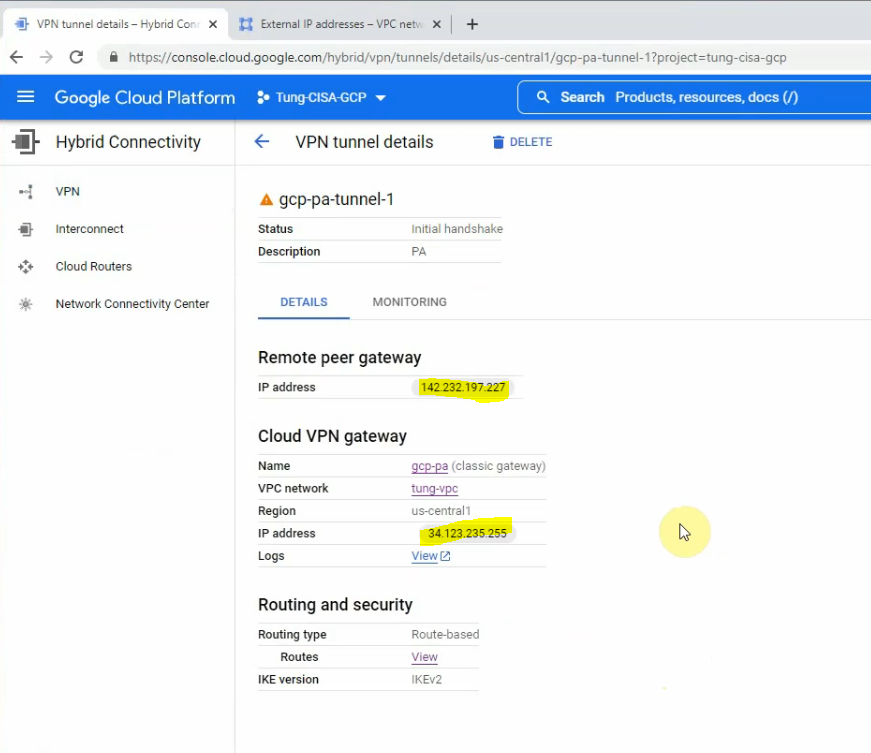
Click gpc-pa-tunnel-1.
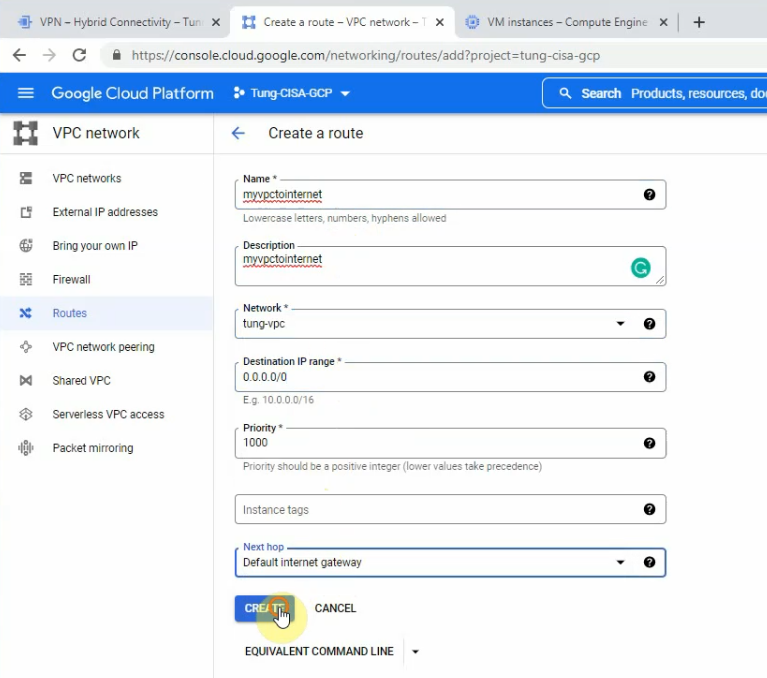
Edit the Routes to allow traffic from my tung-vpc network to the Internet via the Default Internet gateway.
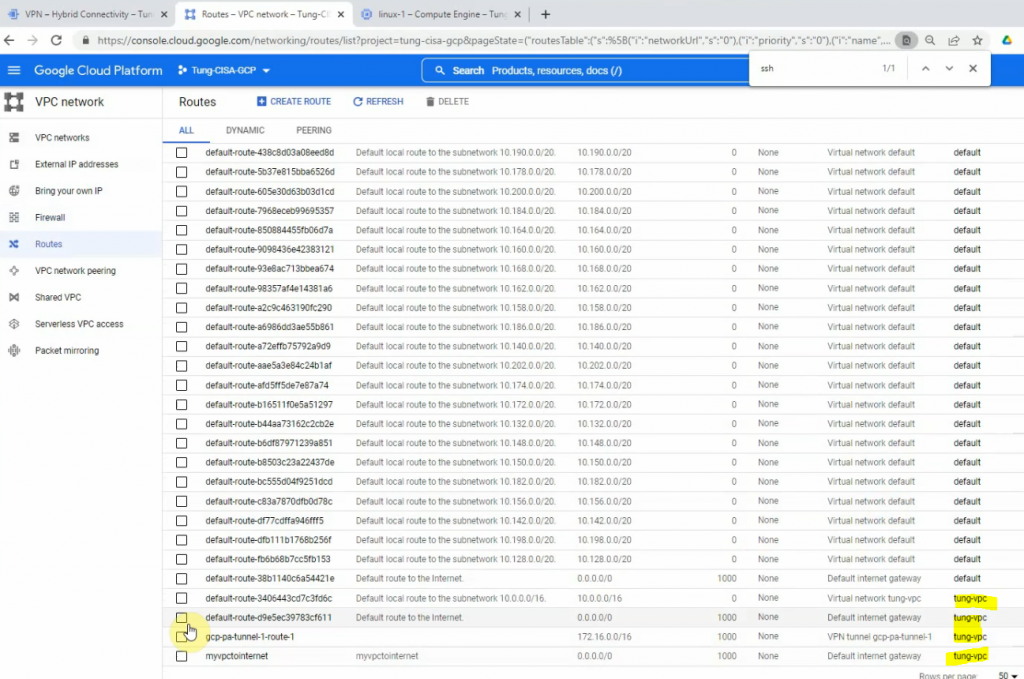
We can see the static route from privatesubnet on GCP to the LAN subnets on Palo Alto has been created on the Routes section.
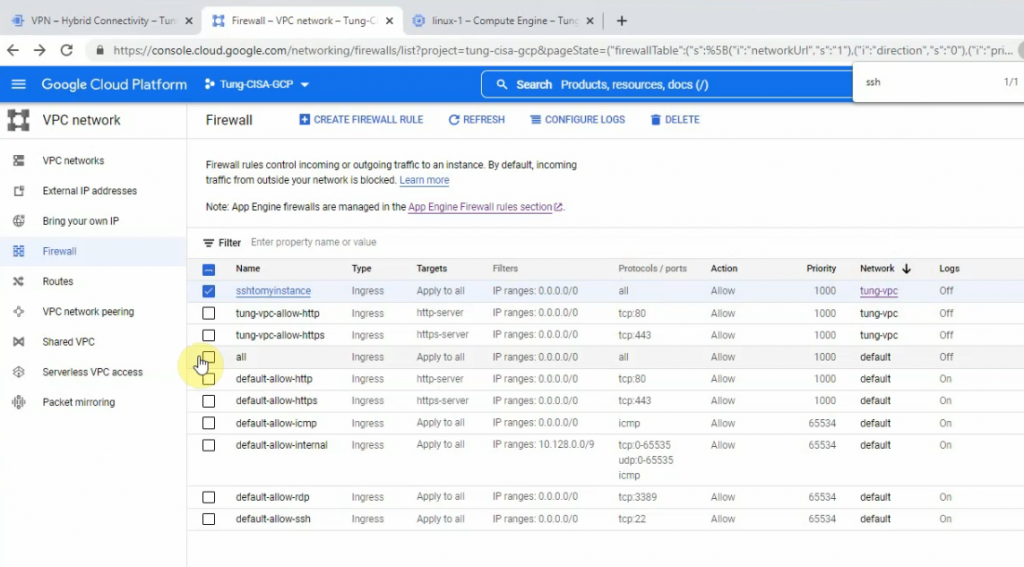
Check the Firewall and allow SSH from the Internet to Linux instance on the “privatesubnet”.
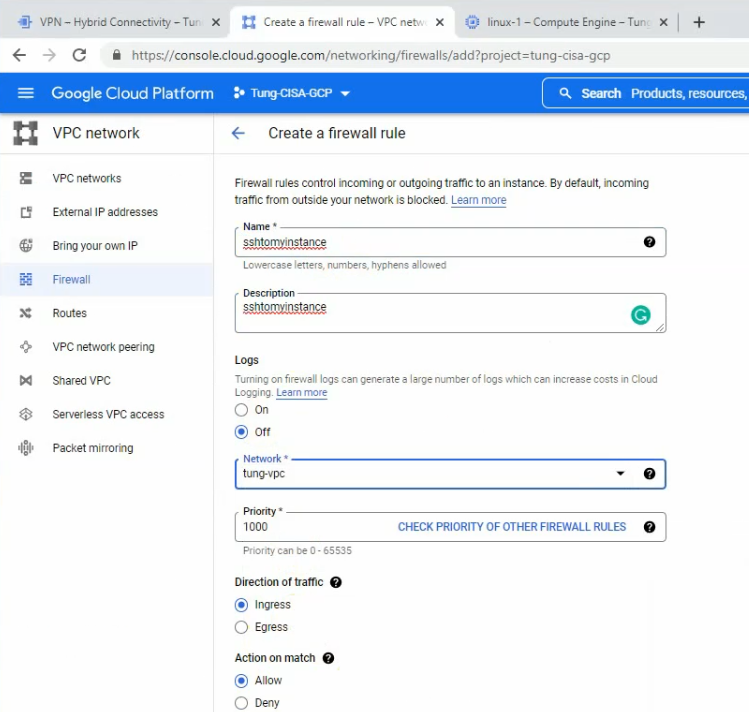
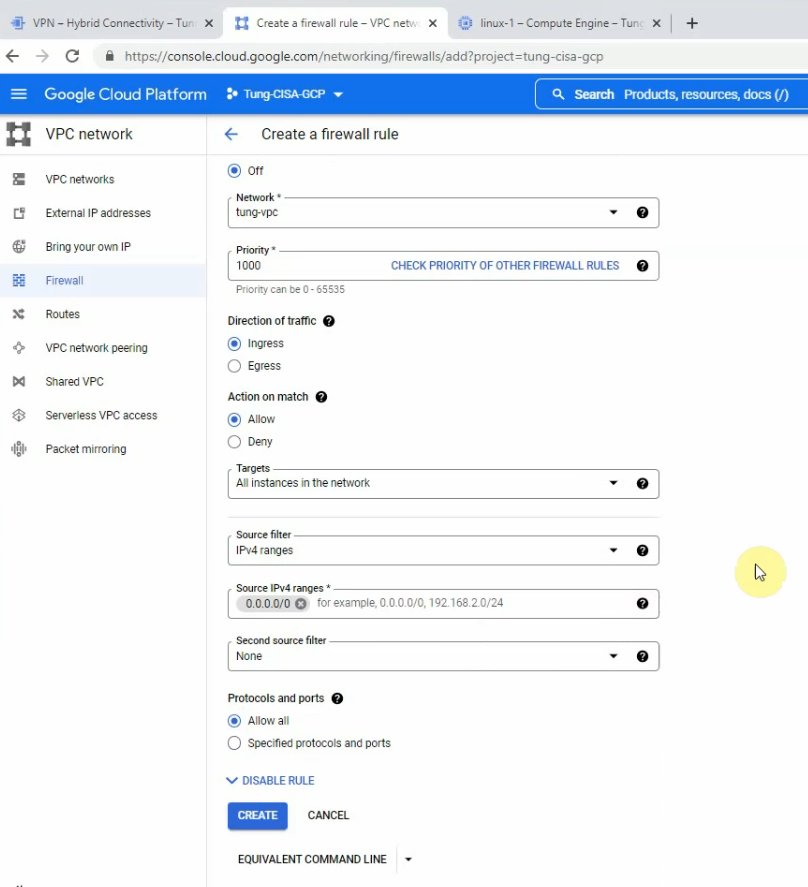
I have used “Allow all” to allow SSH from the Internet to Linux instance, We are able to change to only allow SSH protocol or port 22. Click Create.
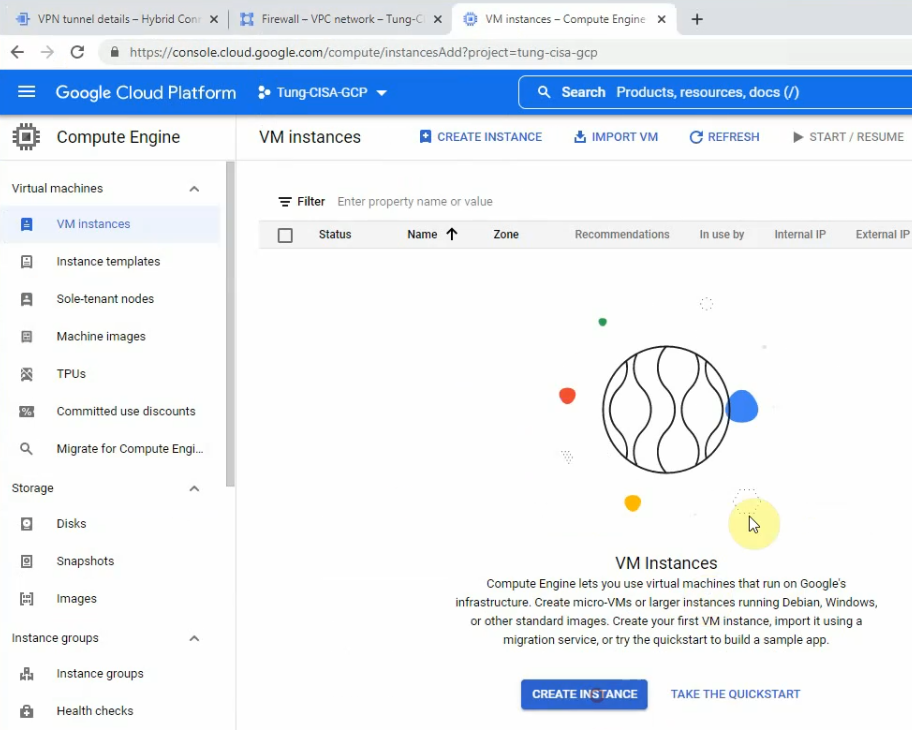
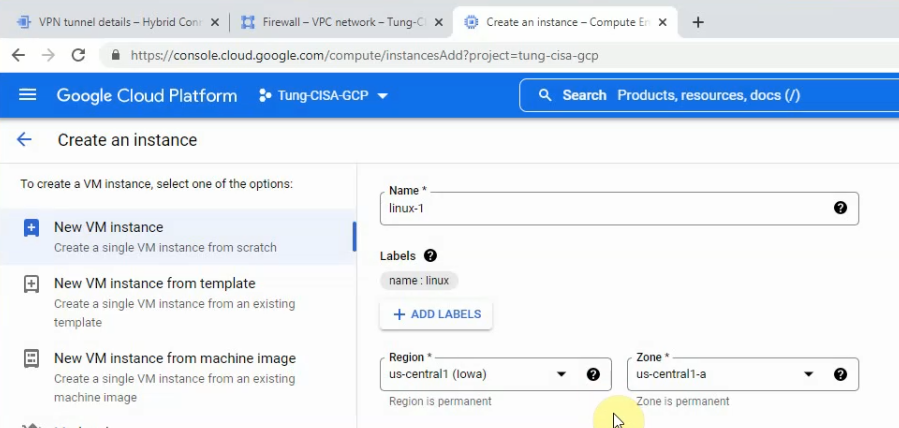
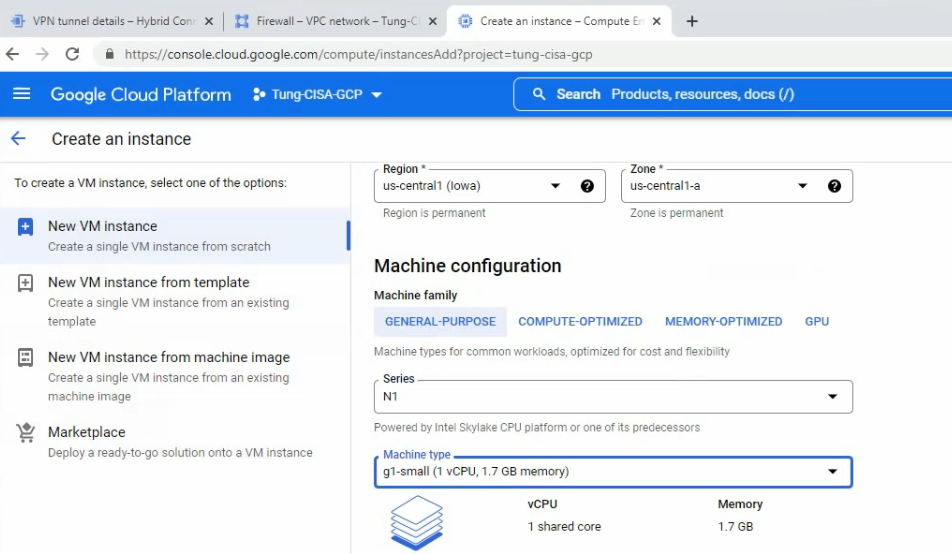
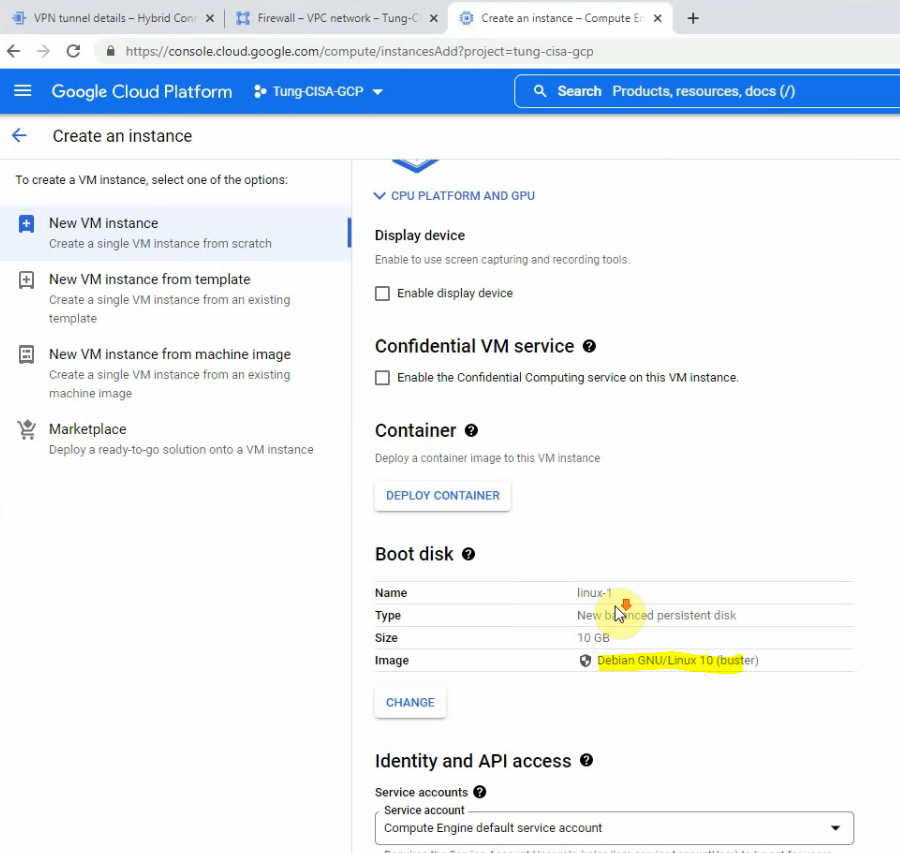
Search “compute engine”, and click create an instance.
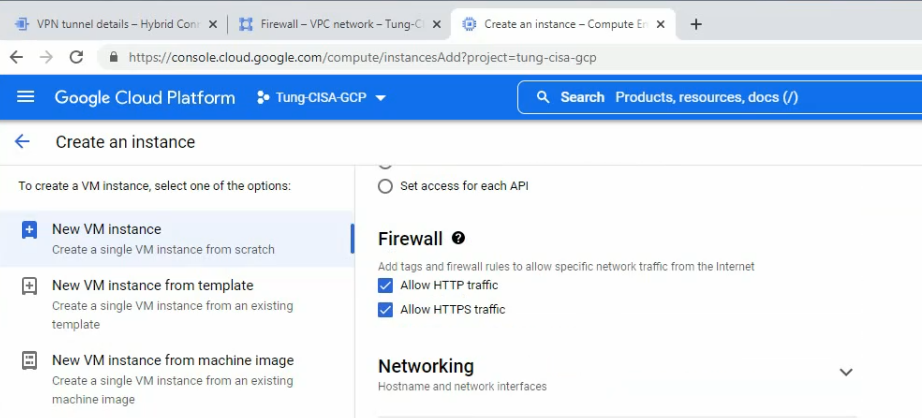
On network interfaces.
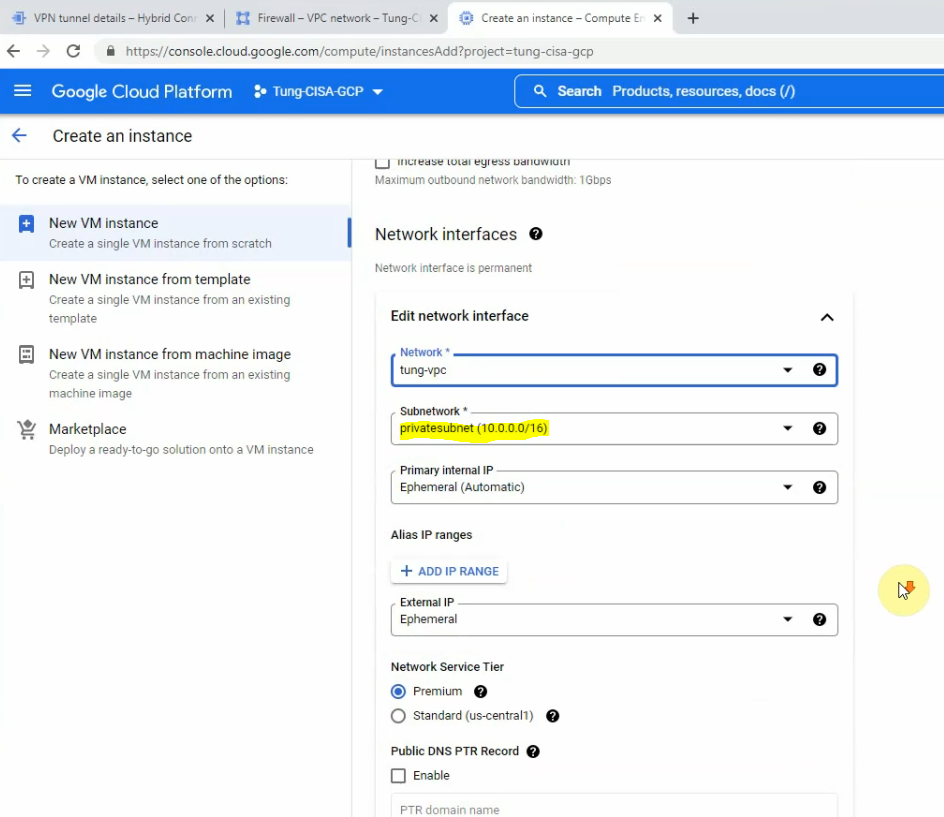
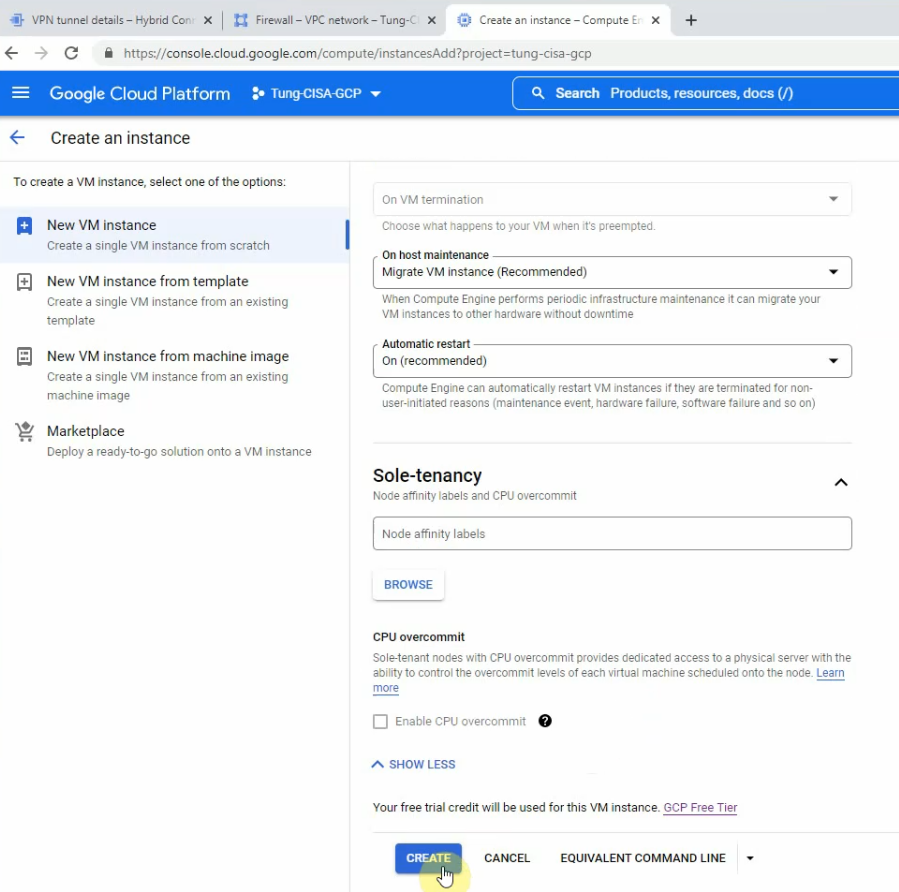
Click create.
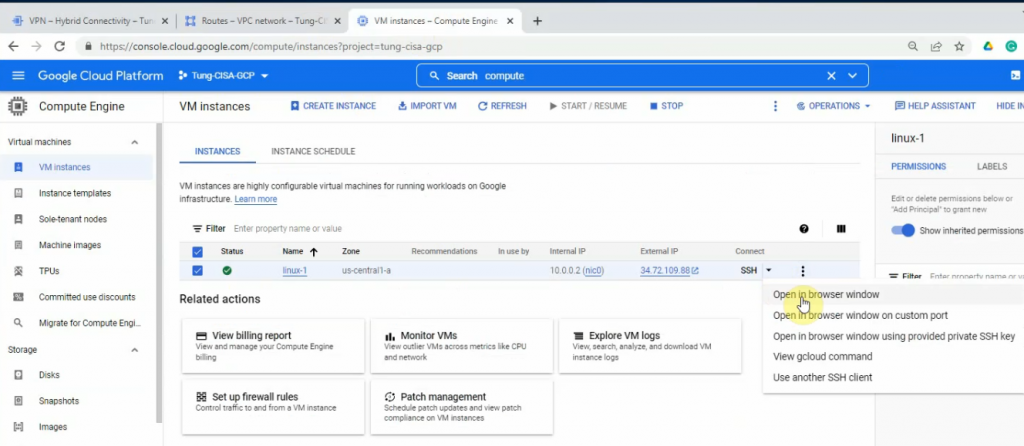
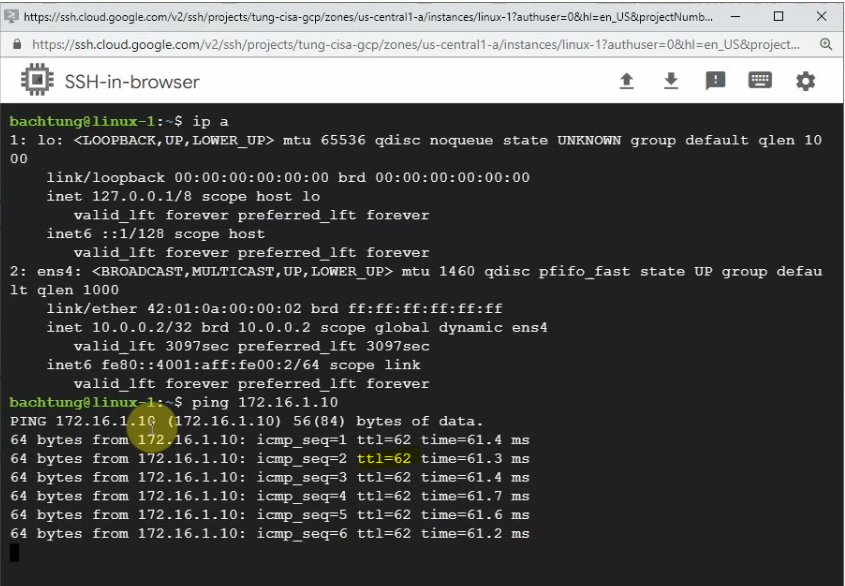
Open SSH in browser windows on the Linux instance.
Back to Palo Alto.
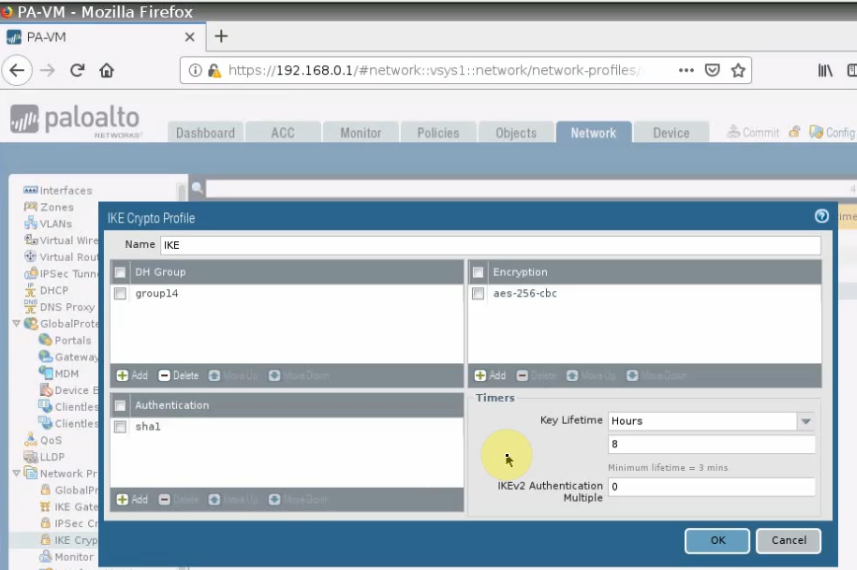
IKECrypto.
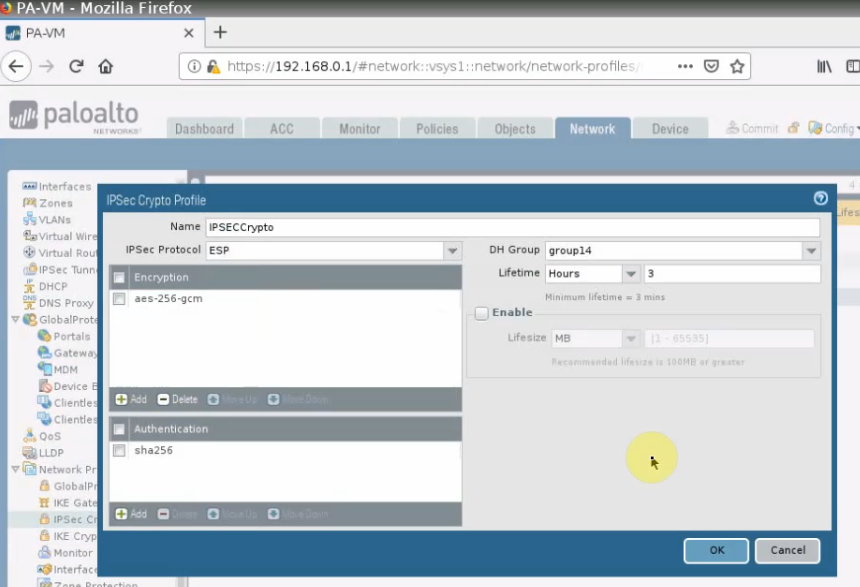
IPSECCrypto.
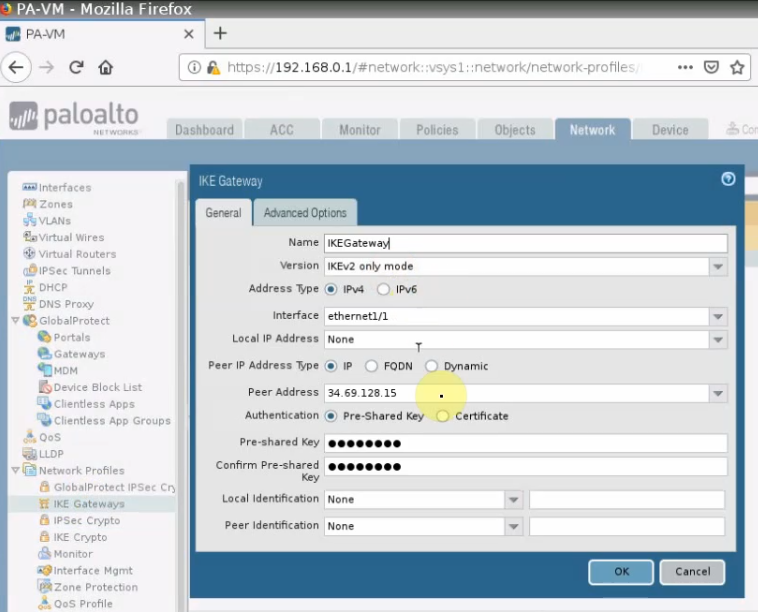
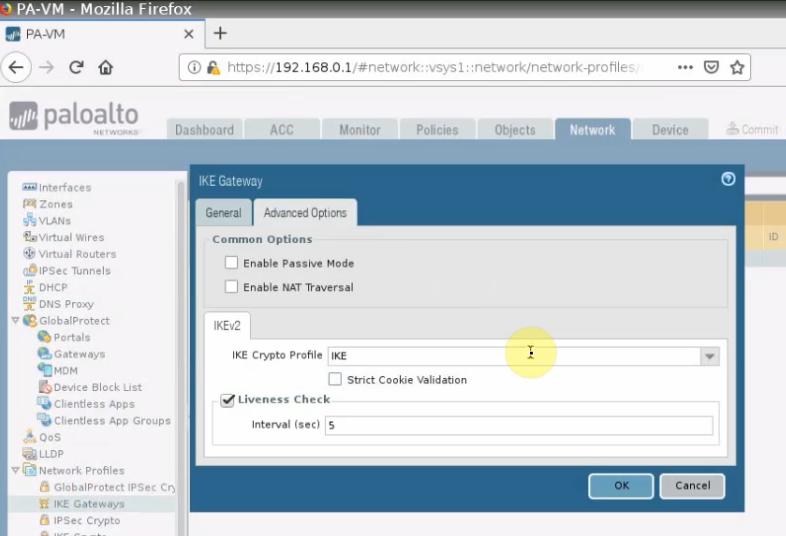
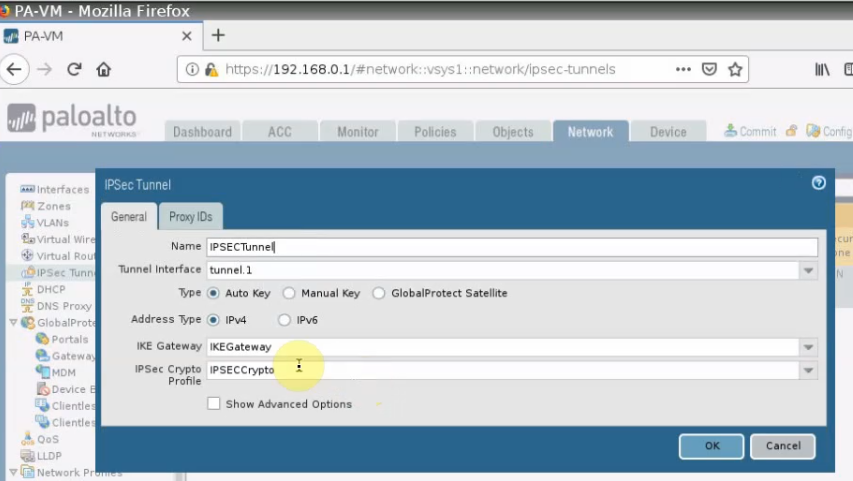
IPSECTunnel.
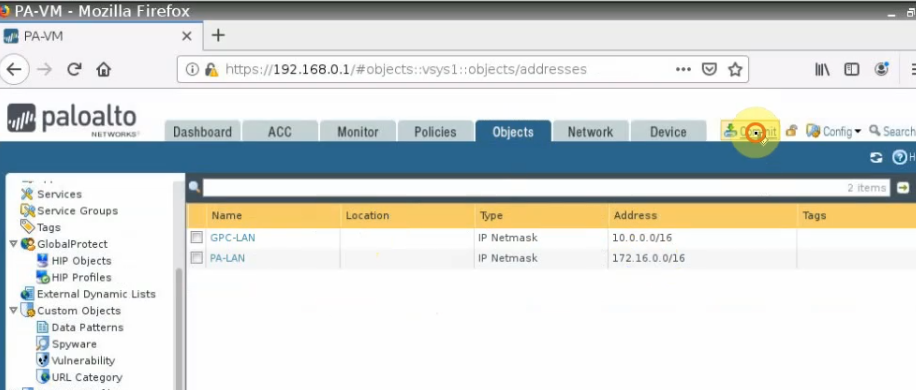
Create both network objects for the Palo Alto-LAN subnet and GCP-LAN subnet
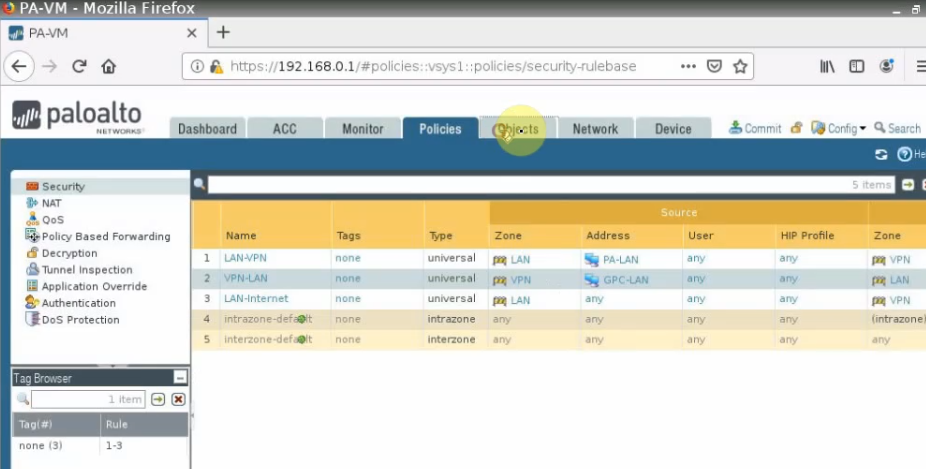
Create both access rules to allow traffic from Palo Alto LAN subnets to GCP privatesubnet.
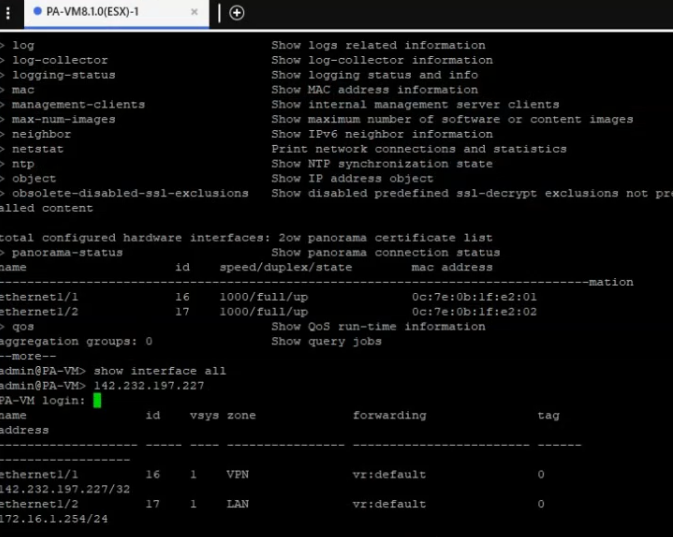
This is the network interface on PA.
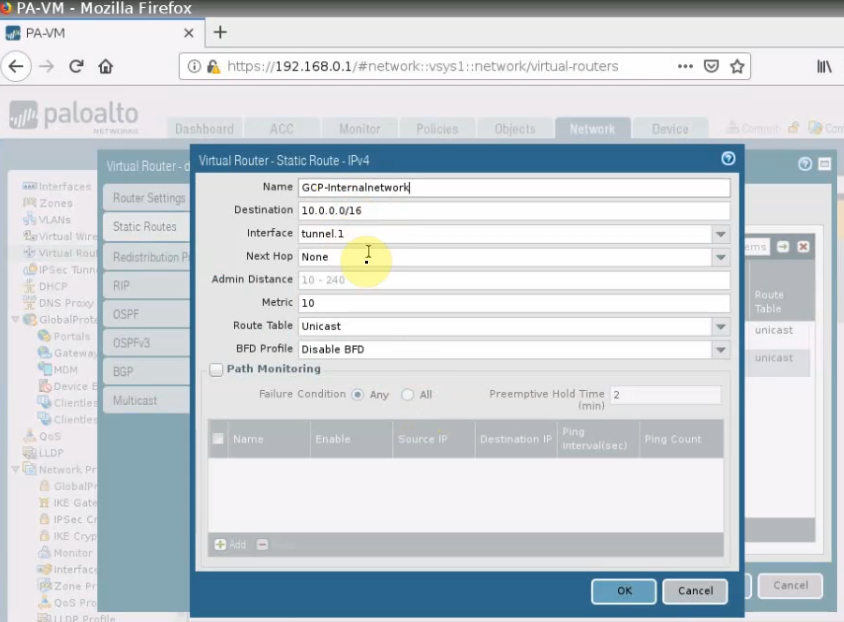
Create a new static route to allow traffic from PA LAN subnets to GCP privatesubnet.
Then, click commit.
Back to GCP.
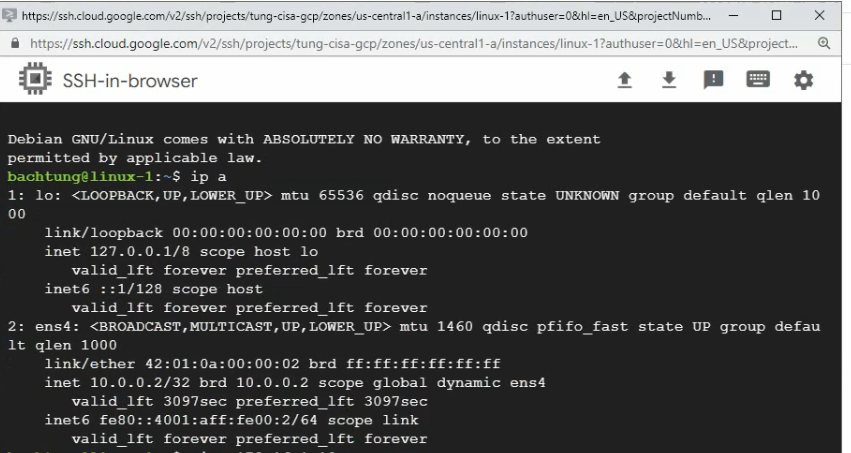
Ping Kali machine on PA LAN subnet from the Linux instance on GCP.
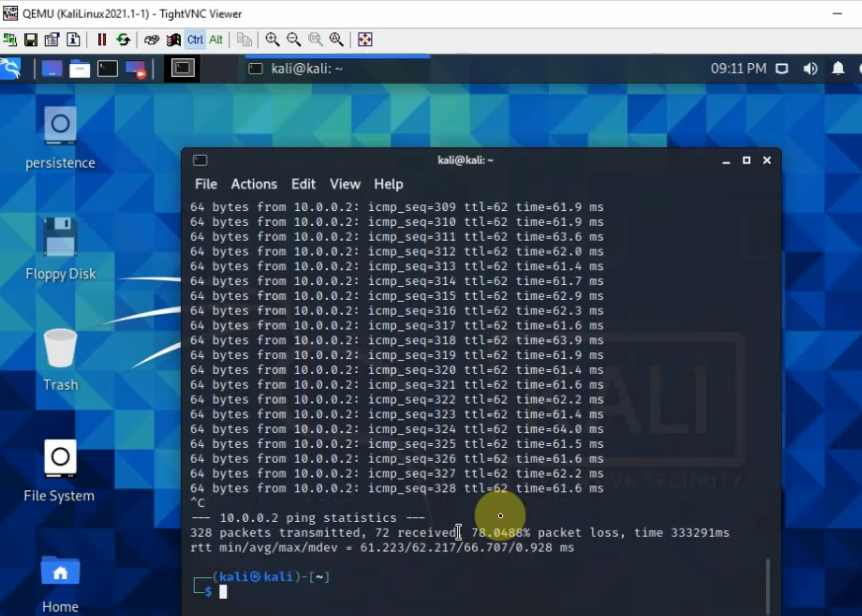
On Kali machine, ping Linux instance on GCP.
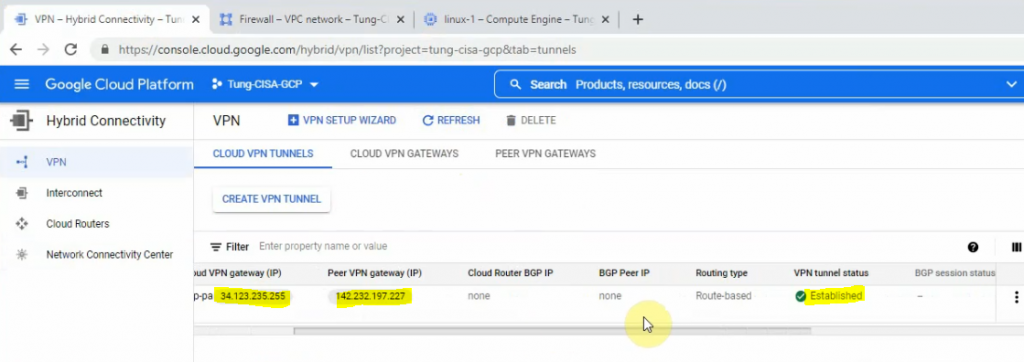
The Palo Alto VPN site-to-site tunnel with GCP is up.
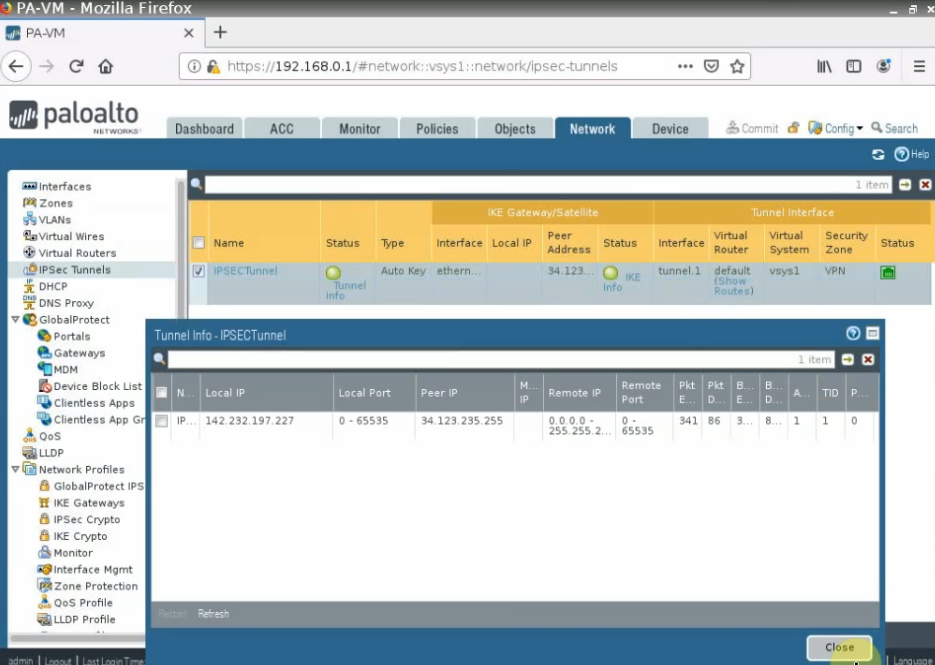
The IPSEC VPN site-to-site tunnel is up on GCP as well.