This is a diagram that I have used to deploy this lab.
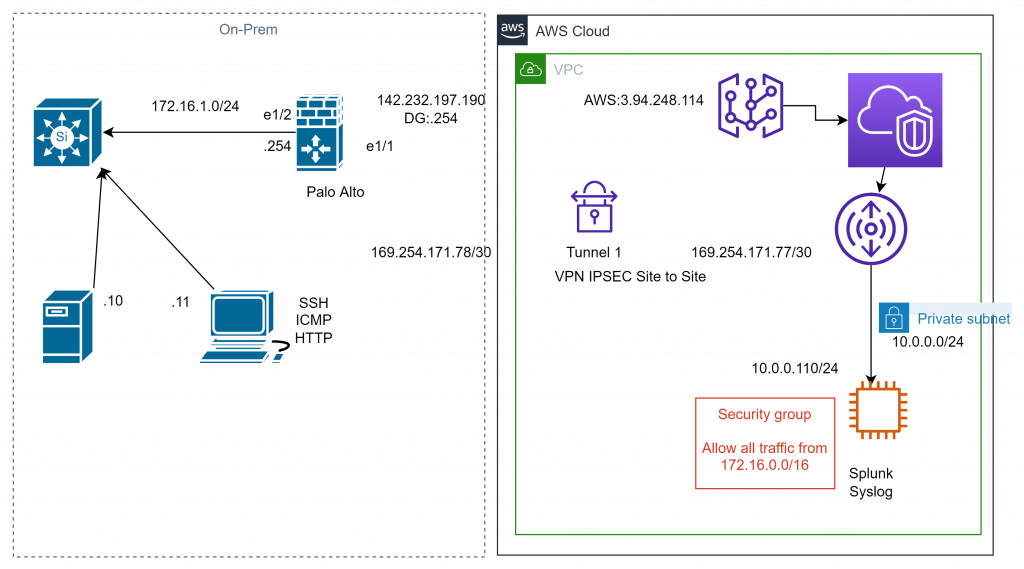
We need to deploy a VPN site to site between Palo Alto on-prem and AWS.
On AWS.
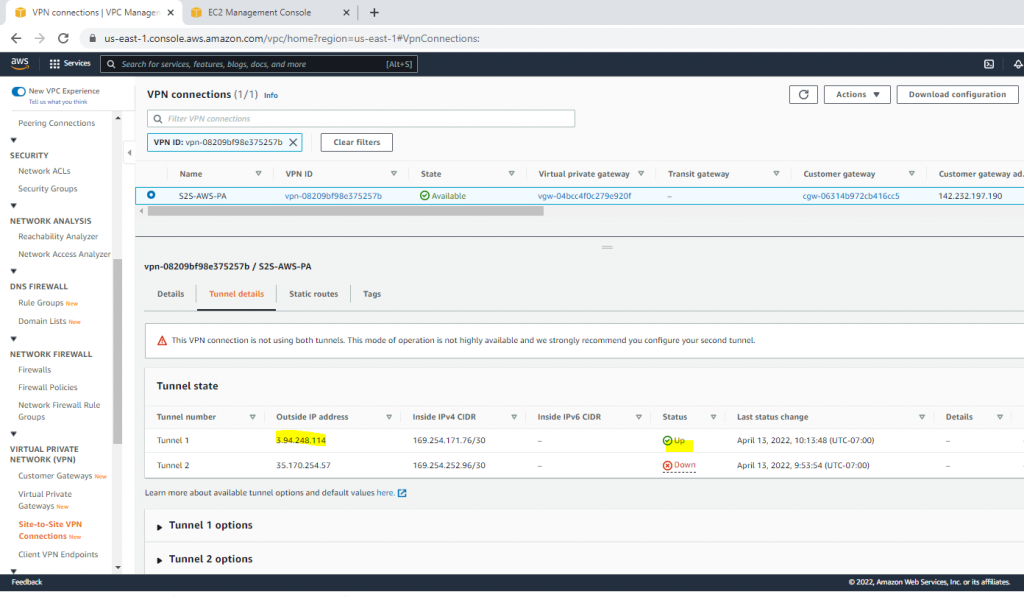
On Palo Alto.
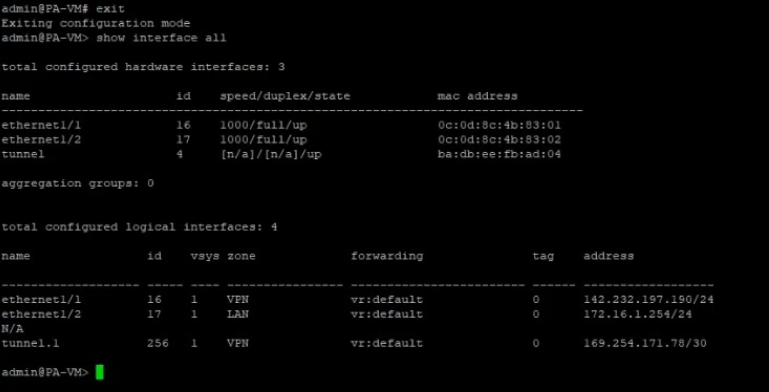
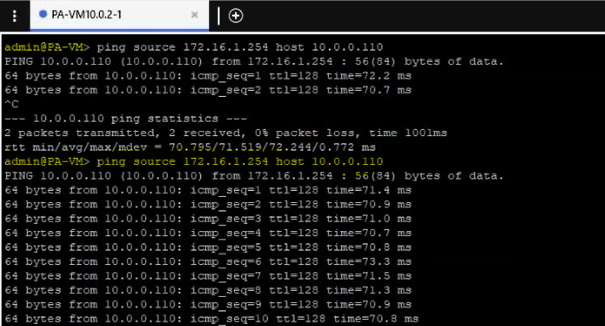
Pings Splunk instance (10.0.0.110) via ethernet 1/2 interface.
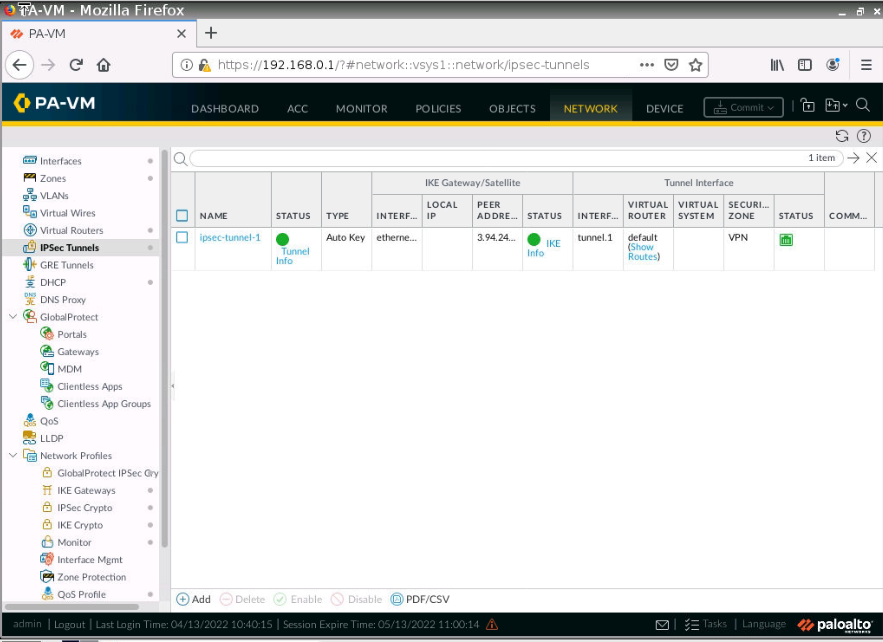
The VPN site-to-site tunnel is up in Palo Alto.
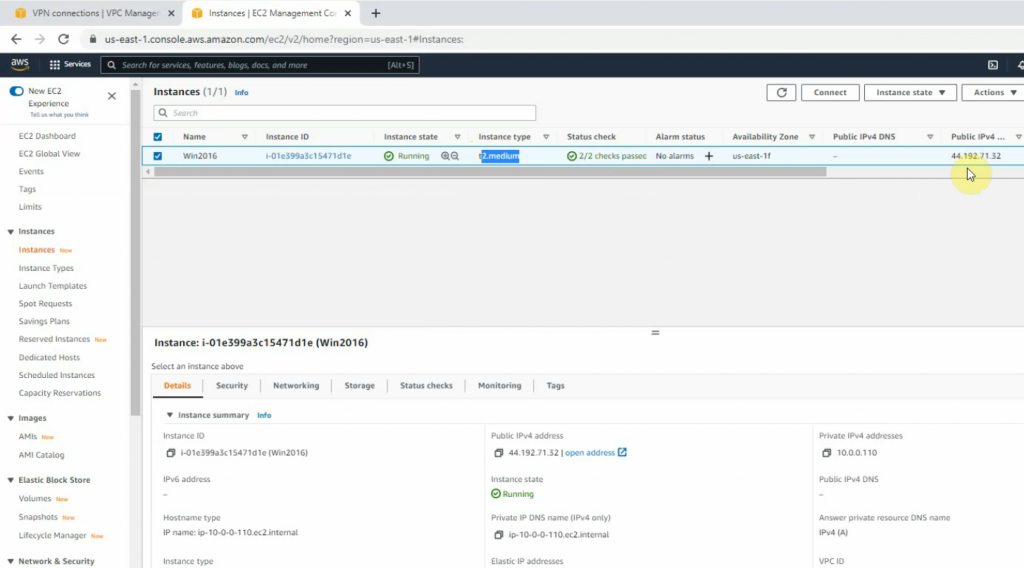
Set up a new Windows 2016 instance with 4 GB memory to run Splunk Enterprise on AWS.
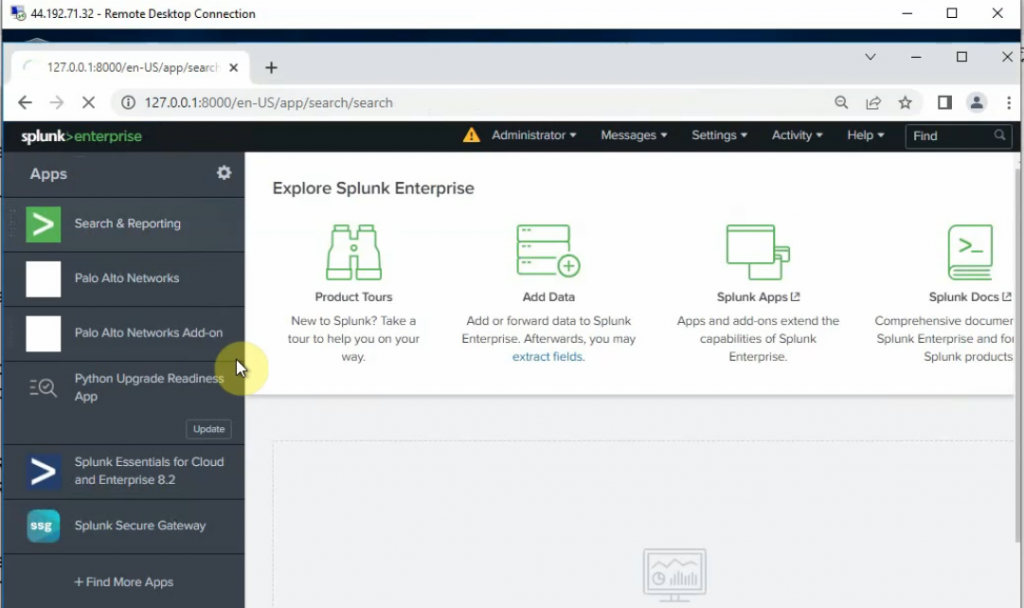
RDP to the instance and install Splunk Enterprise. Then, add Splunk for Palo Alto on this instance.
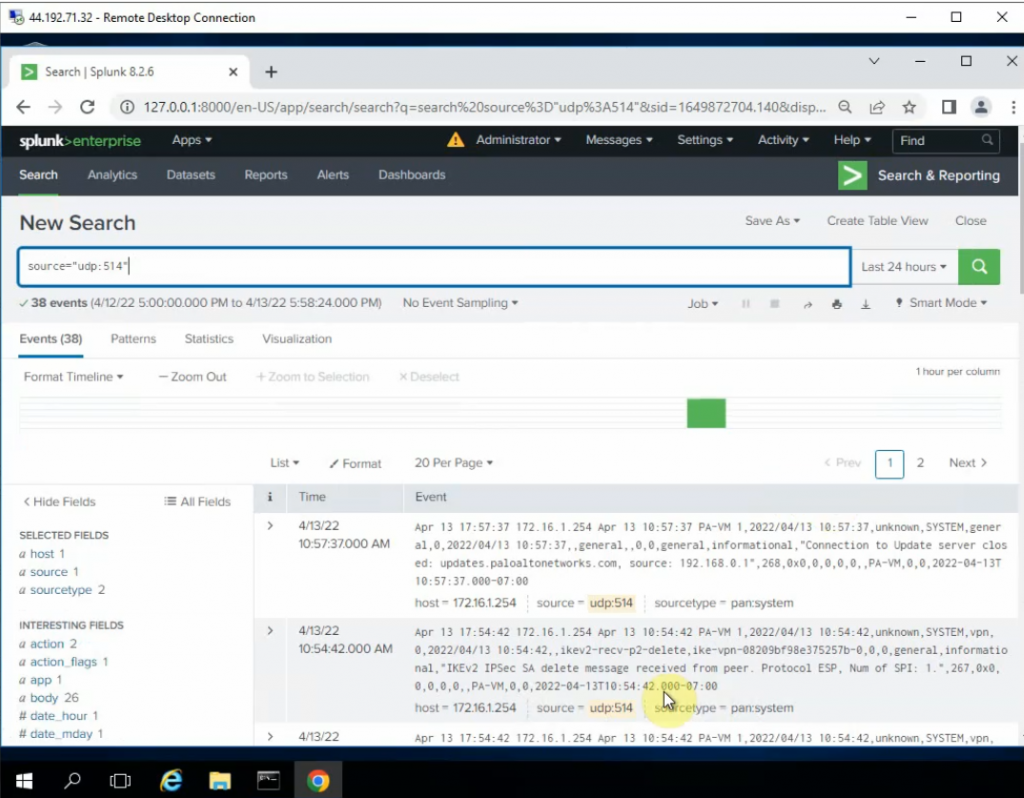
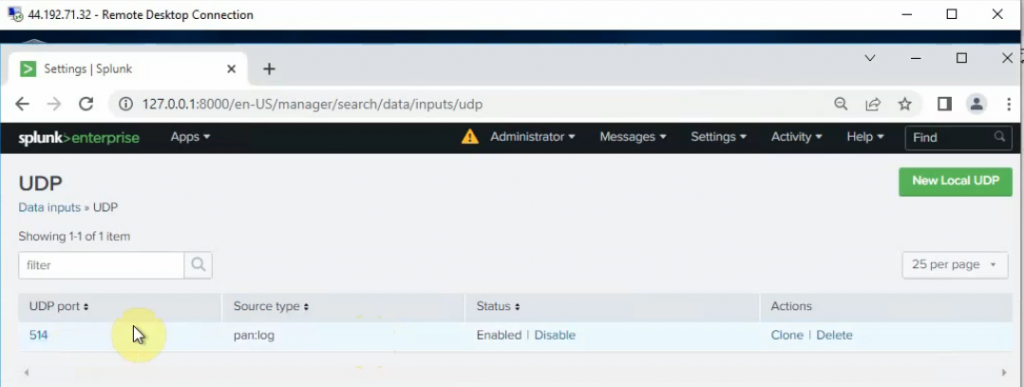
Configure Splunk to get Palo Alto logs via UDP port 514.
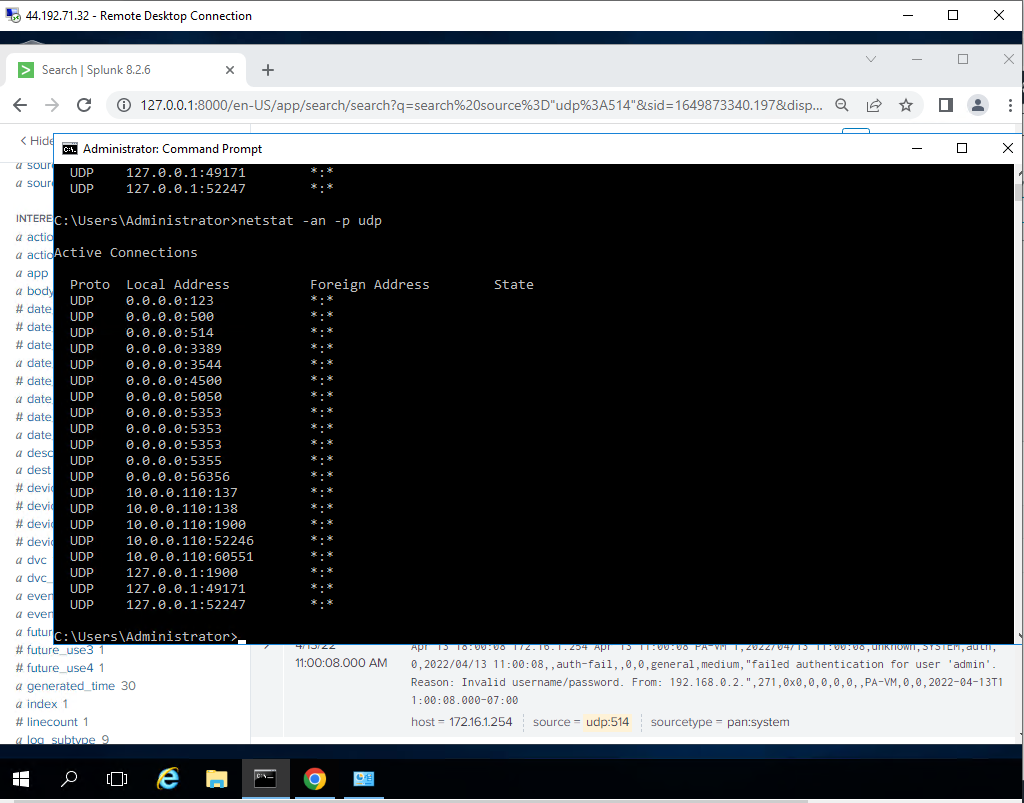
Check the UDP 514 port is running on the Splunk instance.
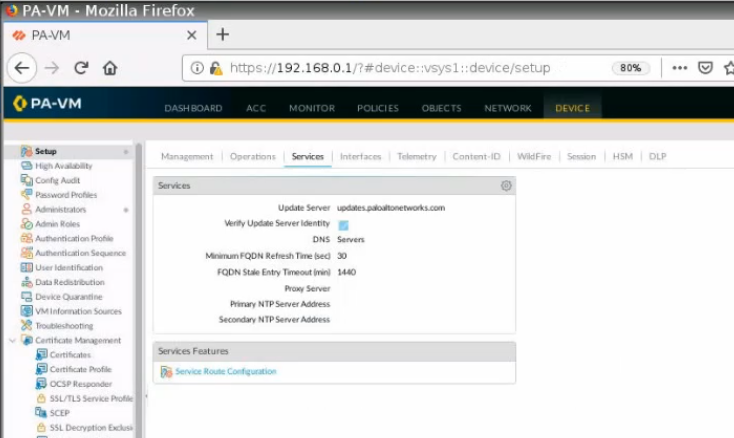
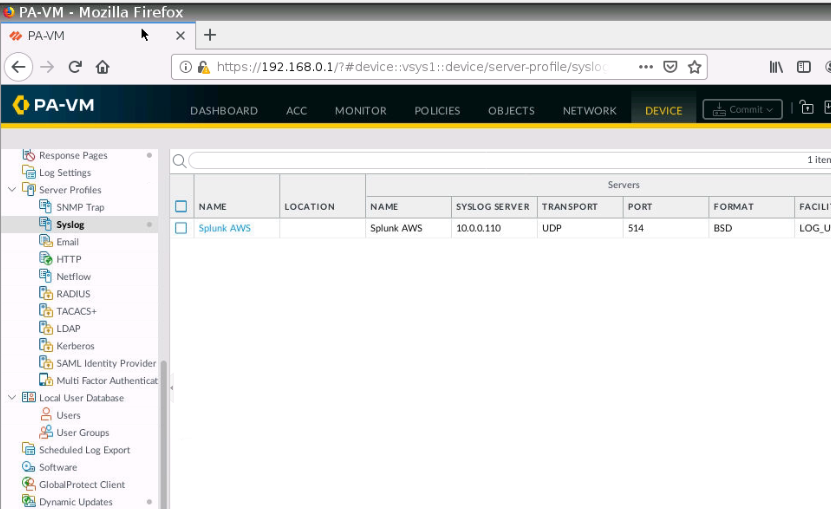
Go to Palo Alto, and configure Syslog to send logs to Splunk.
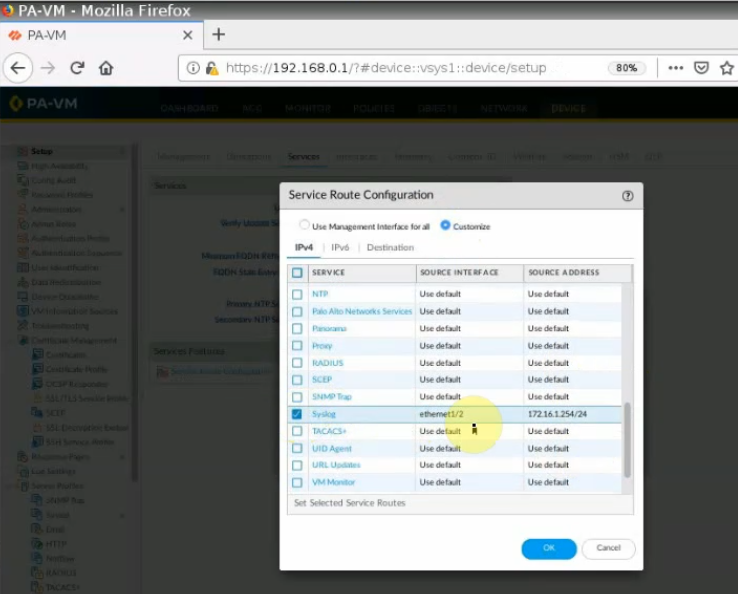
By default, Palo Alto uses a management interface to send logs. We need to change the interface to allow Palo Alto to send logs via ethernet1/2 (LAN interface).
Log on PA console, type configure, and the command below to change the interface to send logs.
set deviceconfig system route service syslog source interface e1/2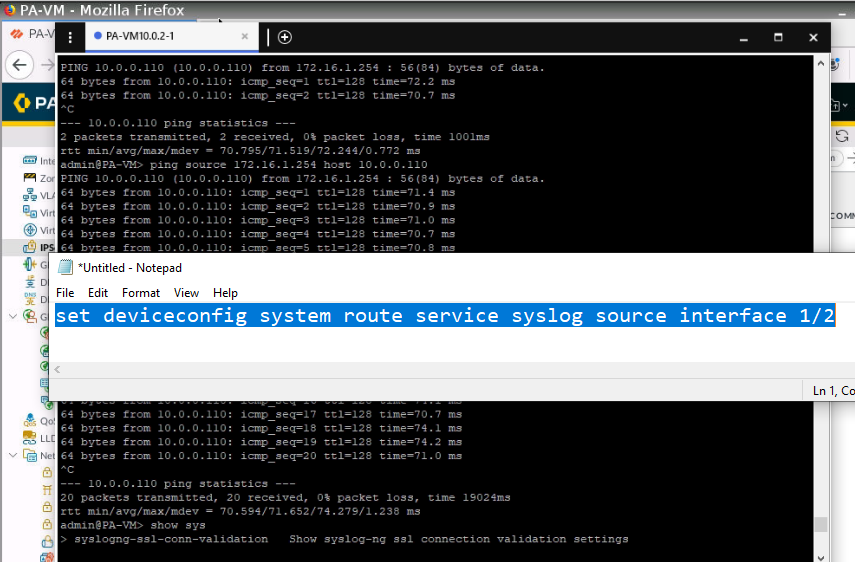
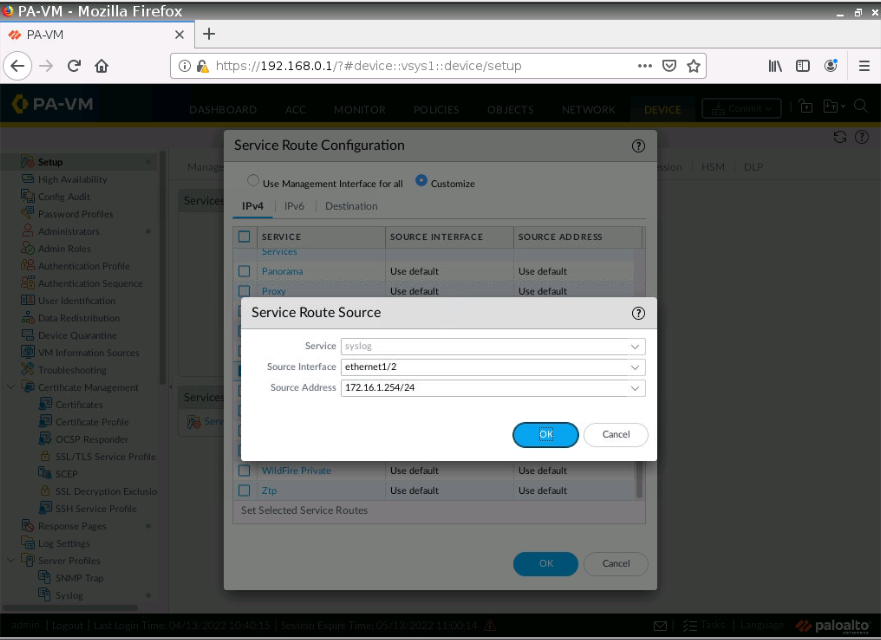
Also, we can go to Device – Setup – Service Route Configuration – Syslog. Configure the source interface and source IP address like the following screenshot.
Configure Syslog on Palo Alto.
IP address: 10.0.0.110 (Splunk instance)
Port: 514 UDP
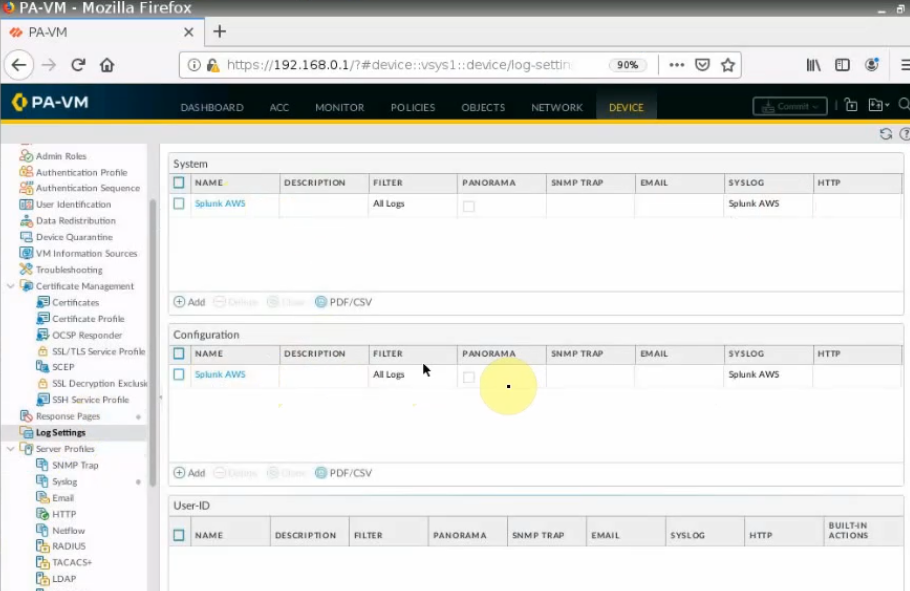
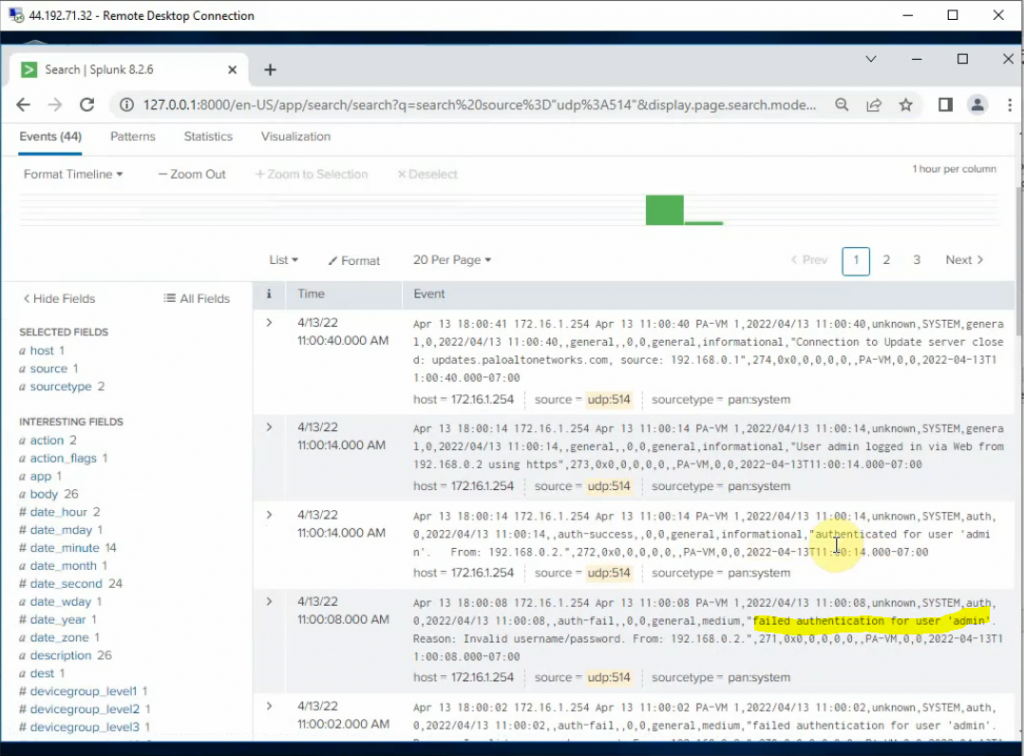
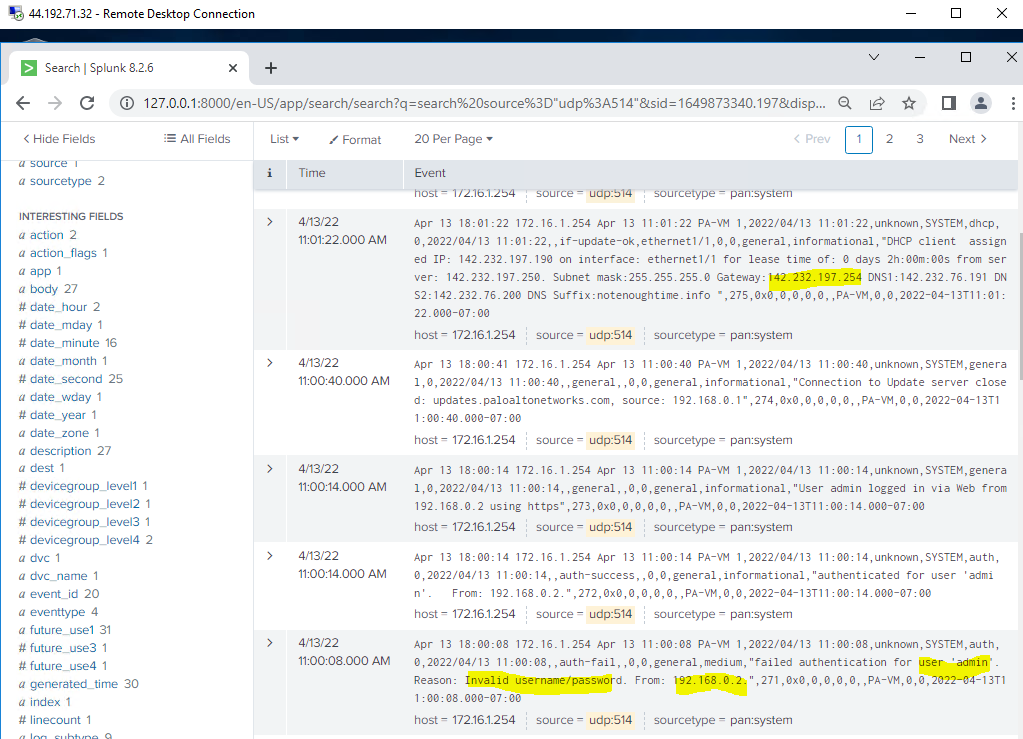
Log off and enter the wrong password on Palo Alto. Log back into Palo Alto to generate logs to send to Splunk.
We can see “failed authentication log” events have been generated on Splunk.