This is a diagram that I have used to deploy this lab.
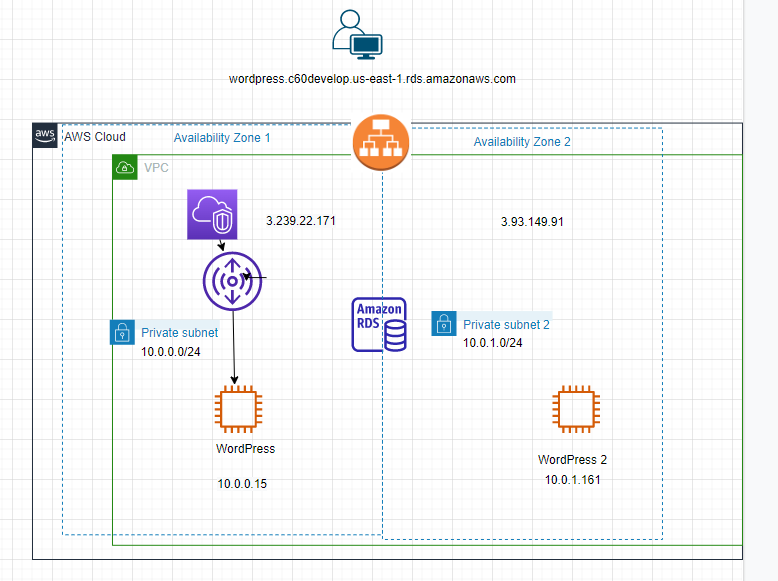
There are a couple of main steps that I have used in the lab.
- Create both private subnets on both AZs
- Create a WordPress instance on the first AZ.
- Create a new MySQL instance.
- Create an AMI for the WordPress instance.
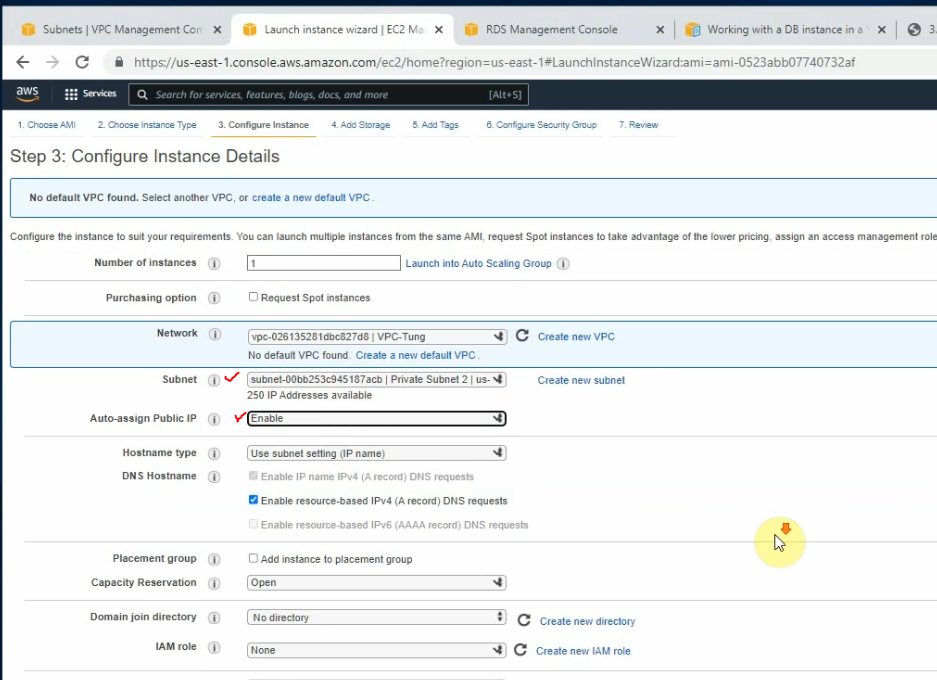
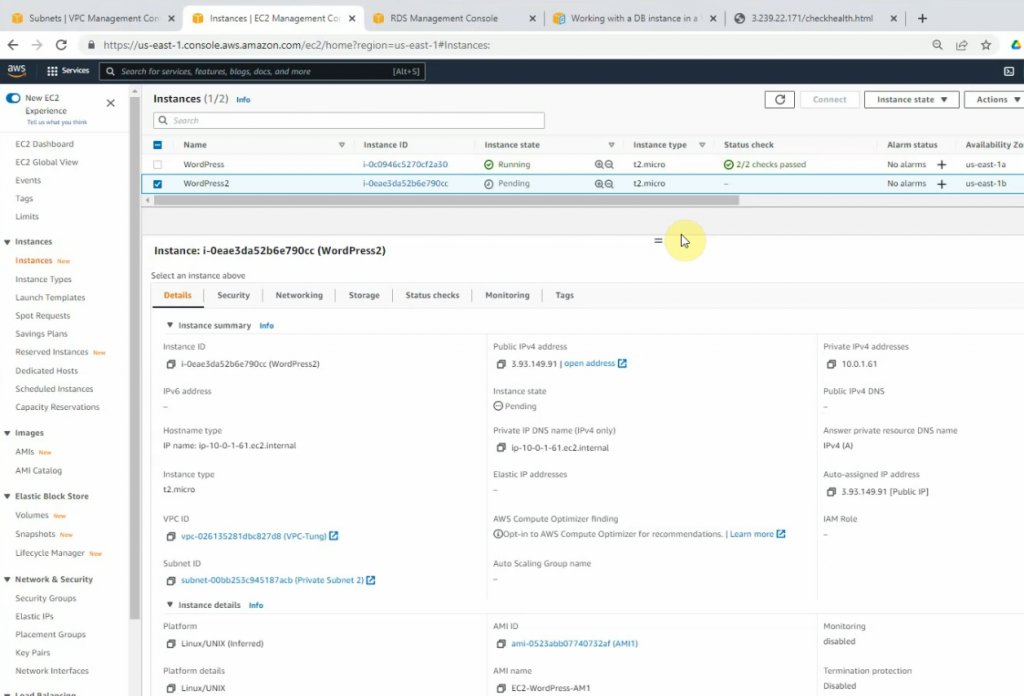
- Launches a new WordPress instance 2 on the second AZ by using your customized AMI.
- Create an Application Load Balancer for WordPress on multiple AZs
- Set up a checkhealth.html file to test the Application Load Balancing
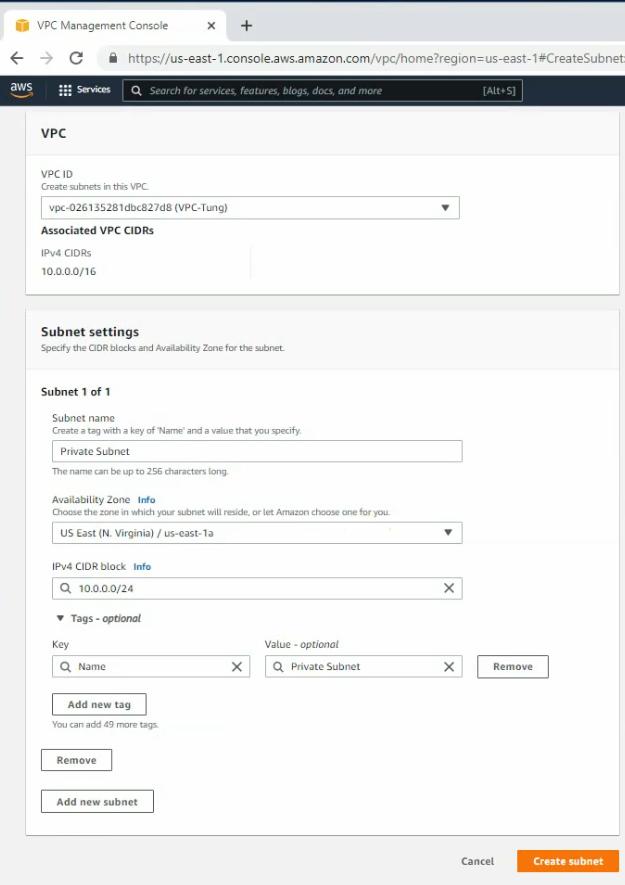
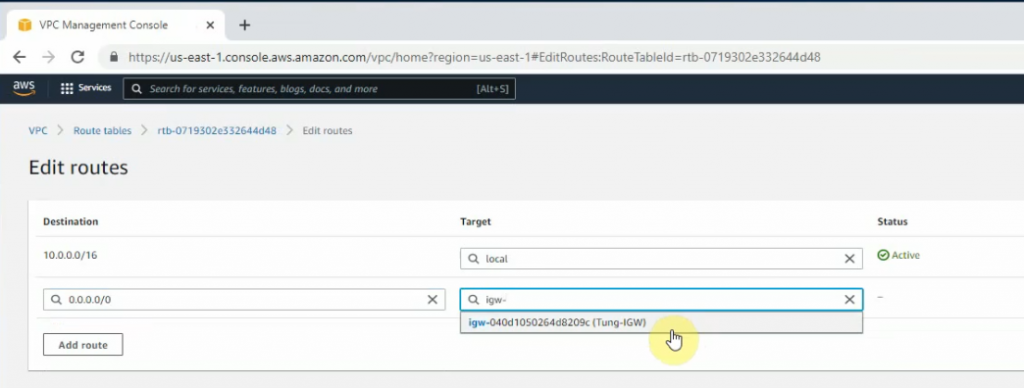
Create a new VPC with CIDR 10.0.0.0/16
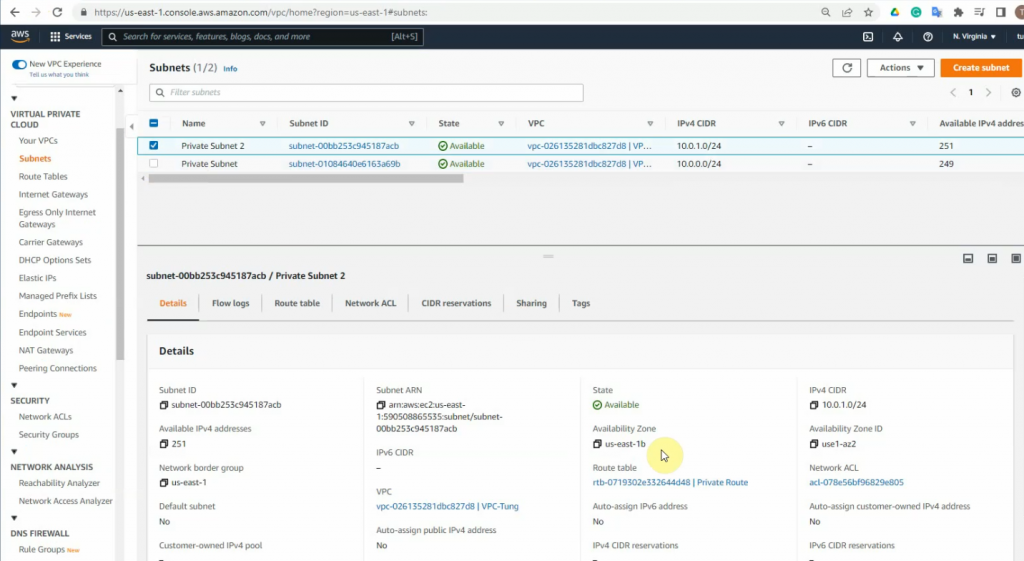
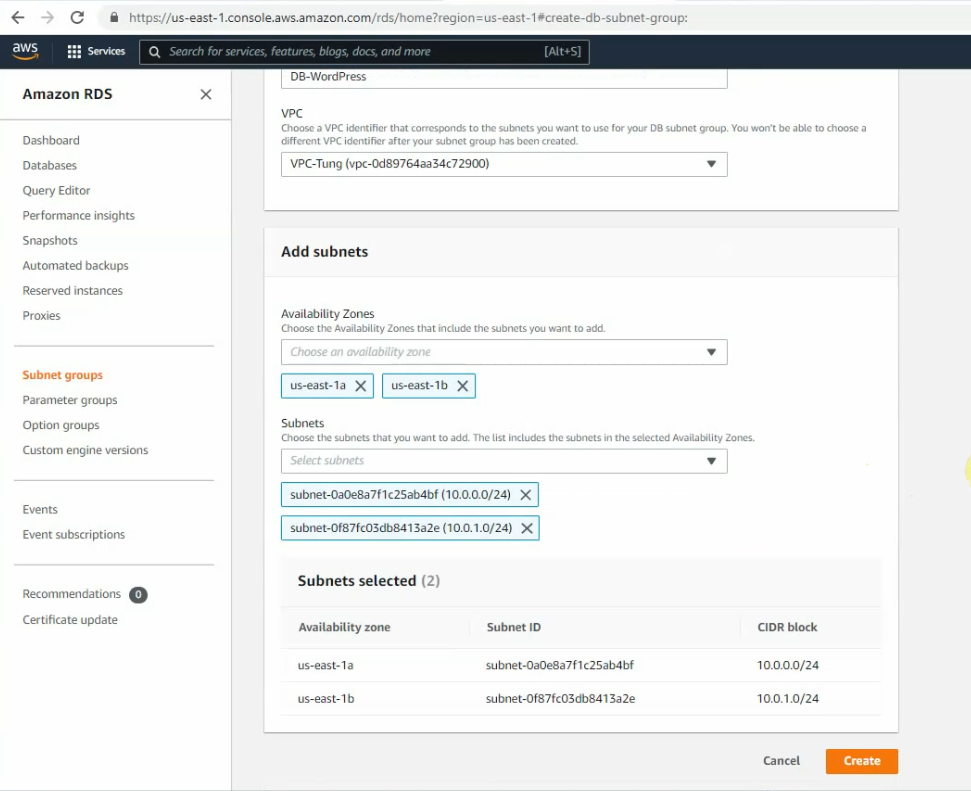
Create both private subnet, 10.0.0.0/24 on us-east-1a and 10.0.1.0/24 on us-east-1b.
Create a new Internet Gateway and attach this to your VPC.
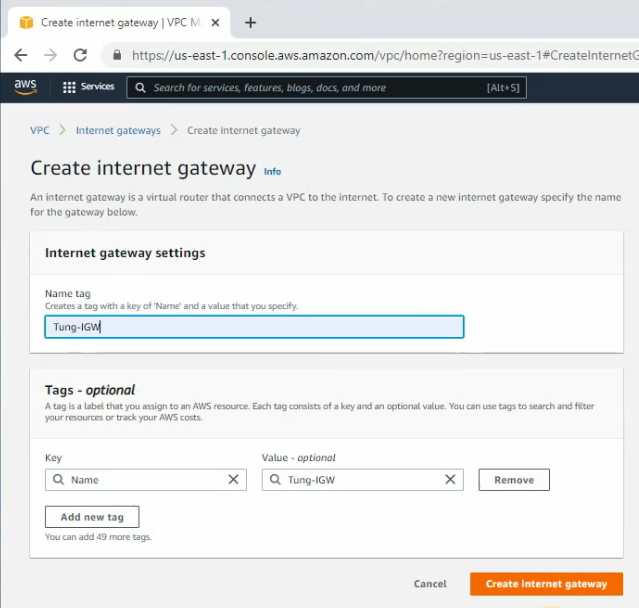
Add a static route 0.0.0.0/0 on your Internet gateway.
Launches a new Linux instance to run WordPress on AZ1.
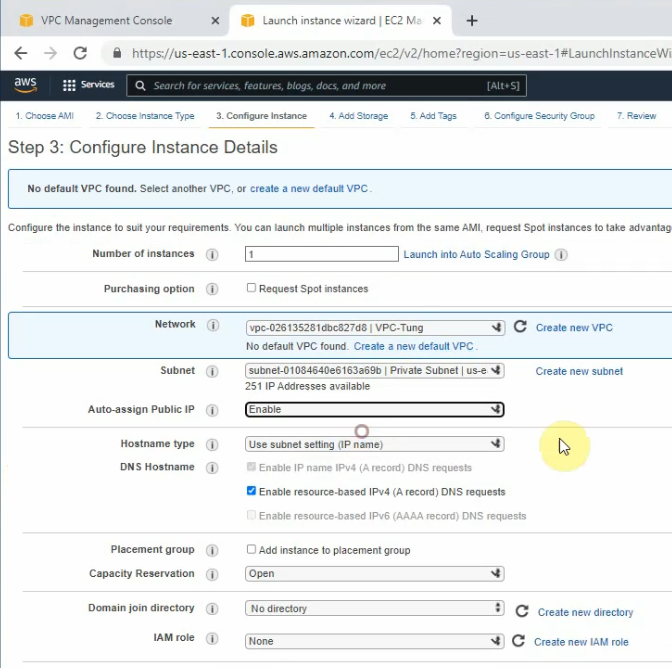
Copy it into the User data setting.
#!/bin/bash
yum update -y
# Install Apache web service
yum install httpd -y
# Download WordPress
wget https://wordpress.org/latest.tar.gz
tar -zxf latest.tar.gz
# Install php7.4
amazon-linux-extras install php7.4 -y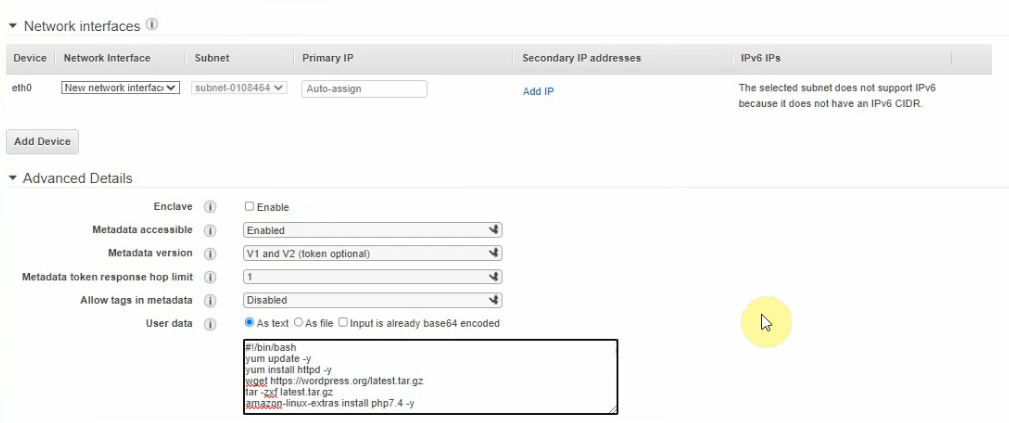
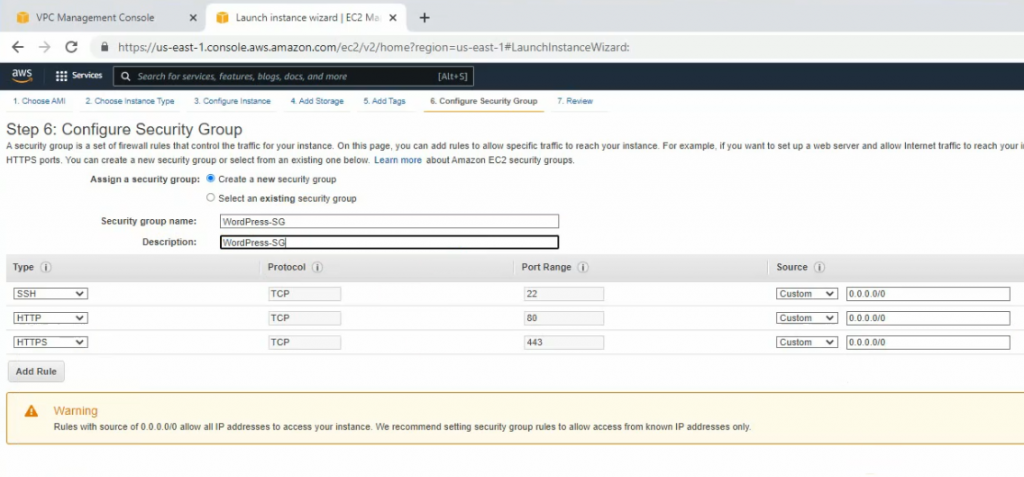
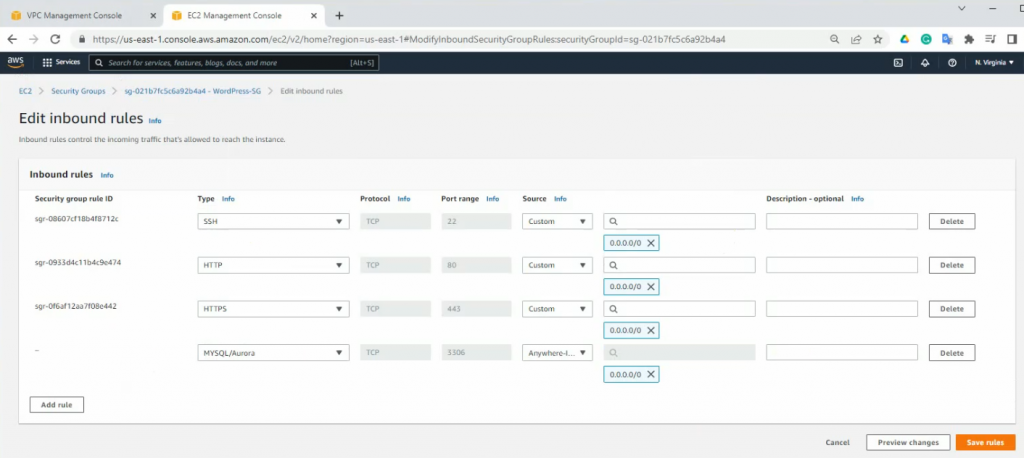
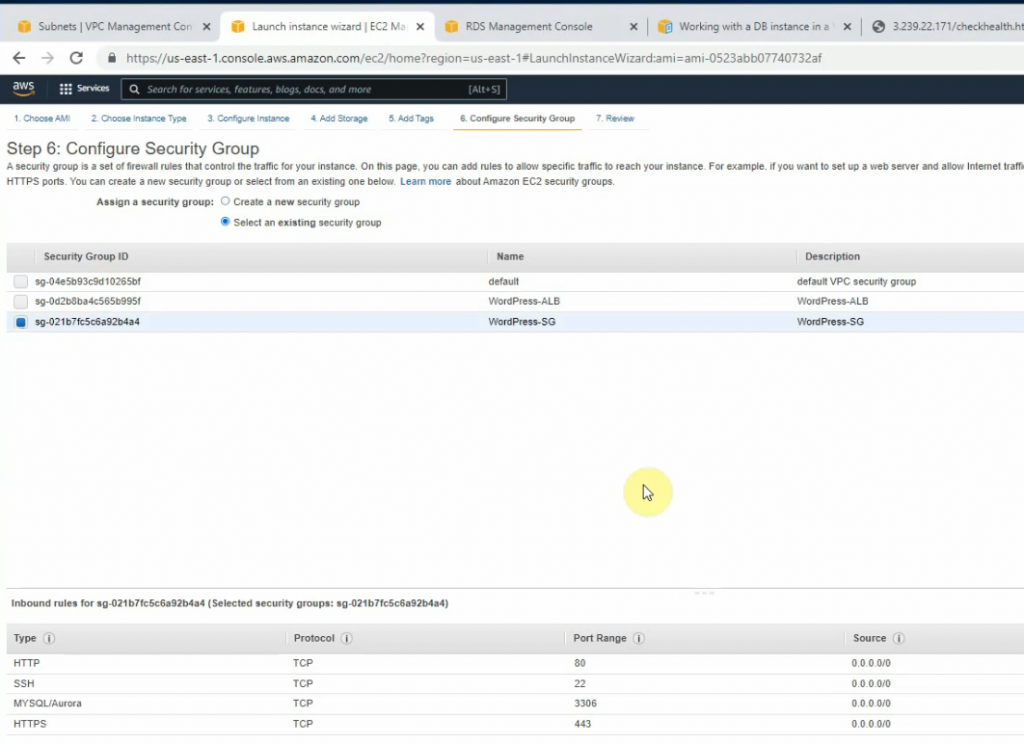
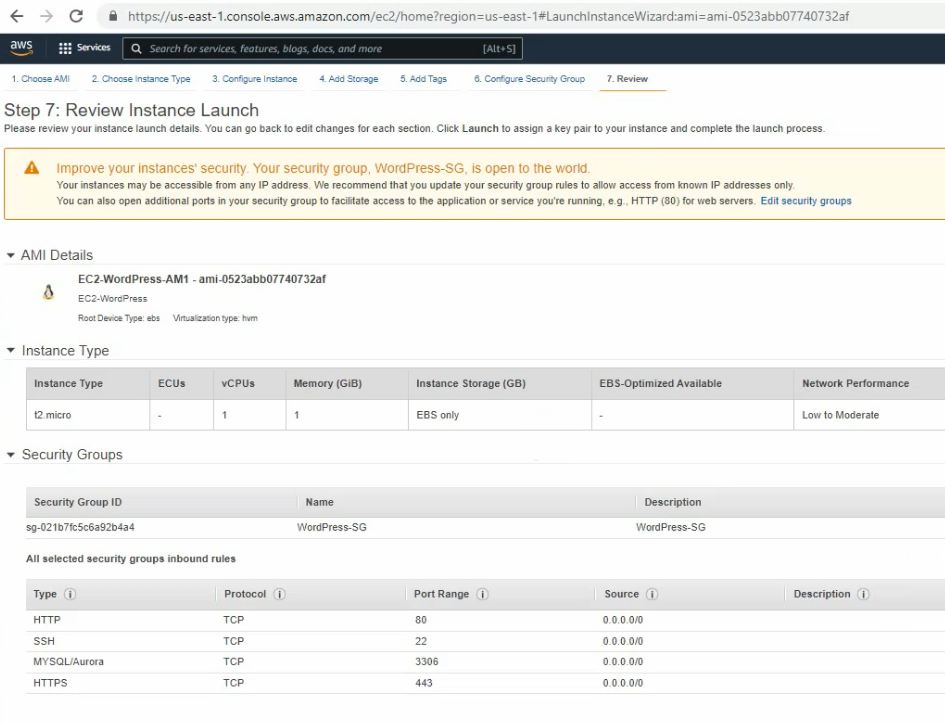
On Security Group, allow SSH, HTTP, HTTPS, and MySQL/Audora from 0.0.0.0/0.
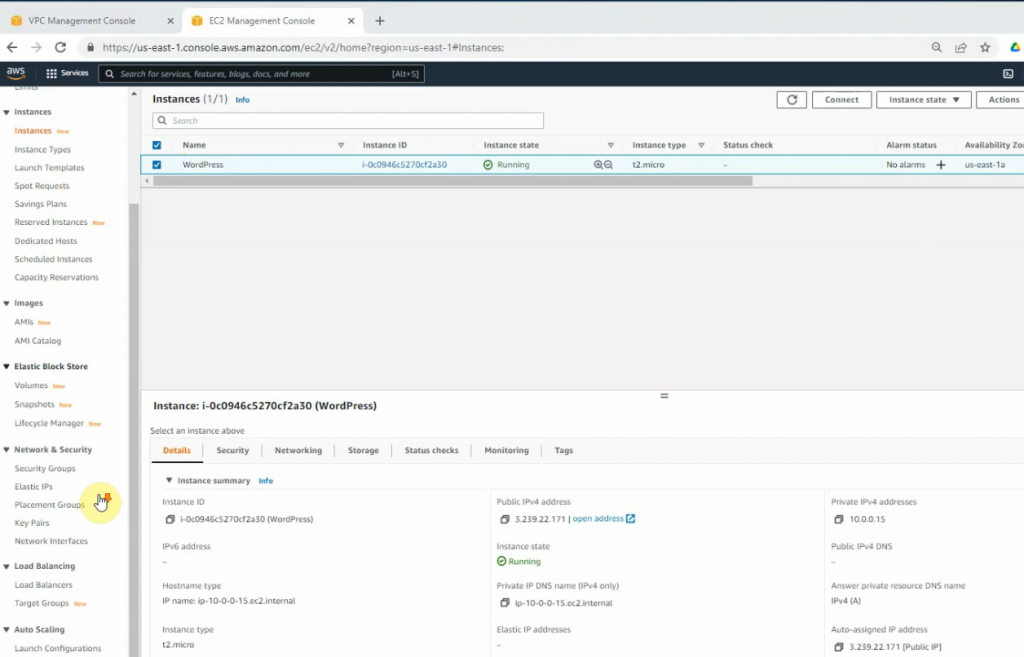
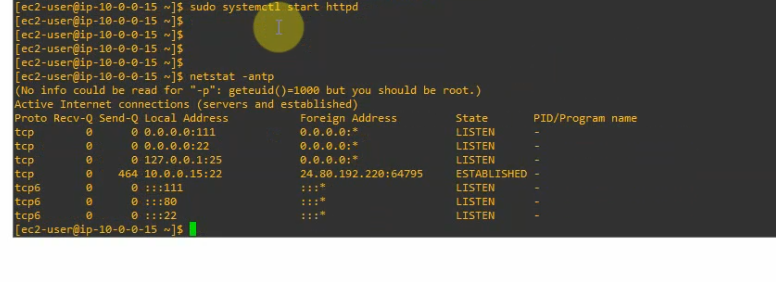
SSH to Linux instance.
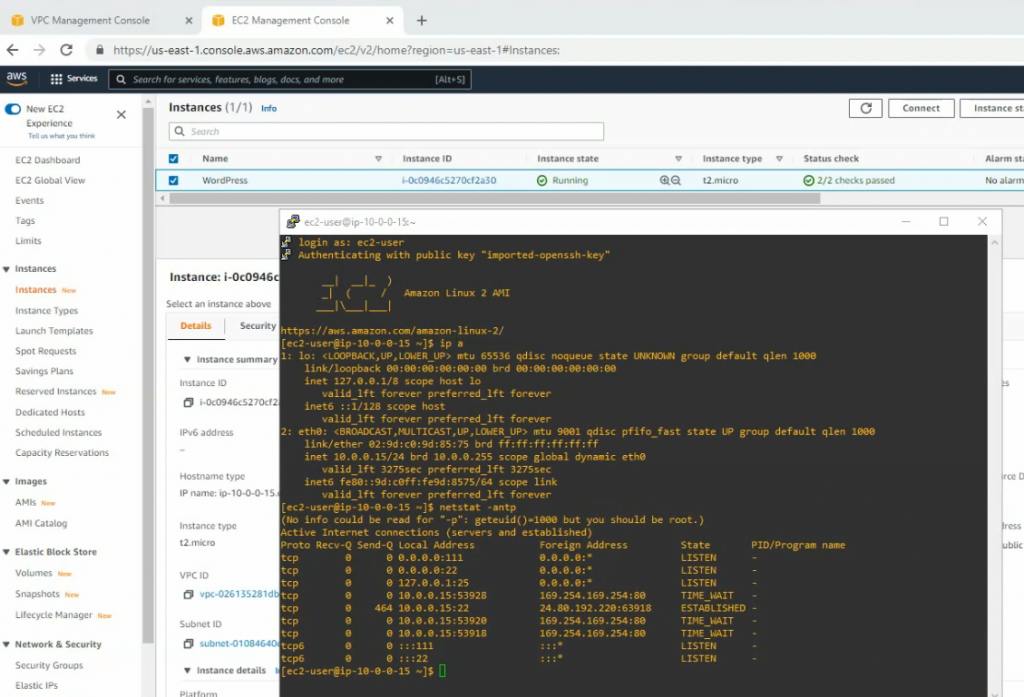
Check httpd, php is installed on the machine.
rpm -qa | grep httpd
rpm -qa | grep php
sudo yum install php -y
sudo systemctl start httpd
sudo systemctl enable httpd
netstat -antp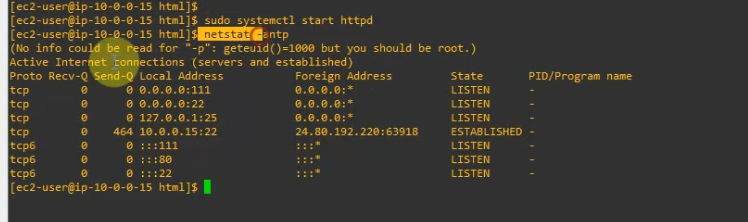
Copy all files on WordPress directory to /var/www/html
cd /wordpress
sudo cp -r * /var/www/html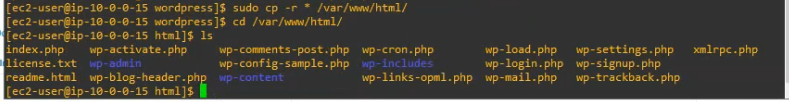
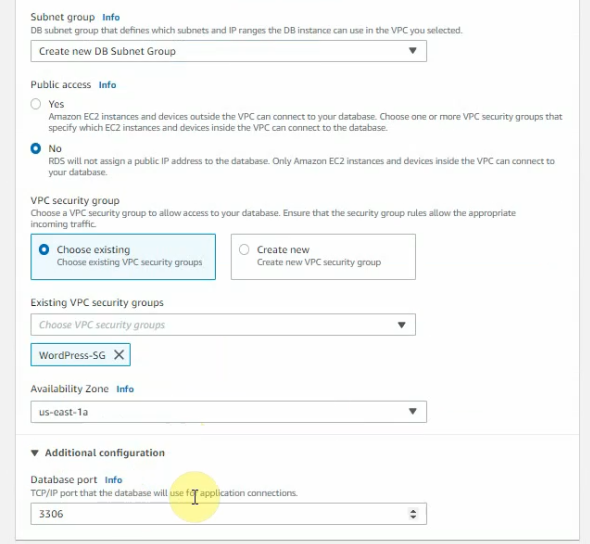
Go to Amazon RDS, create subnet groups on Amazon RDS.
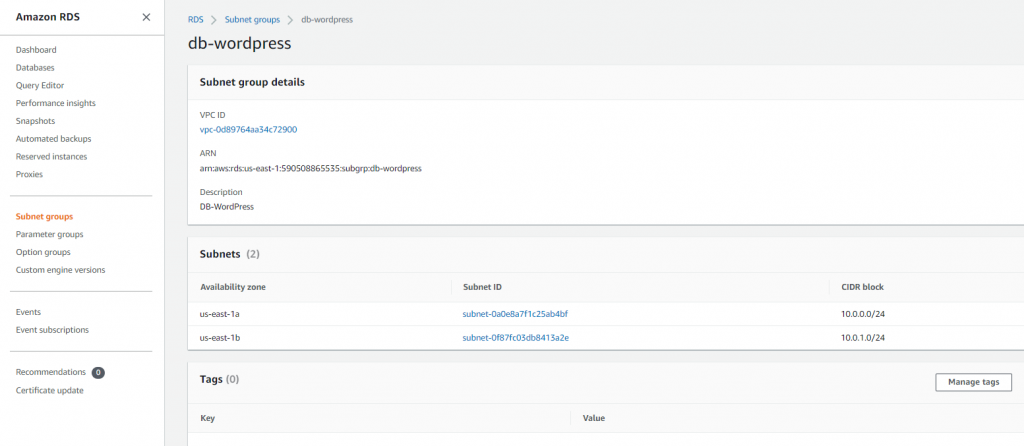
Create a new Database instance on AWS.
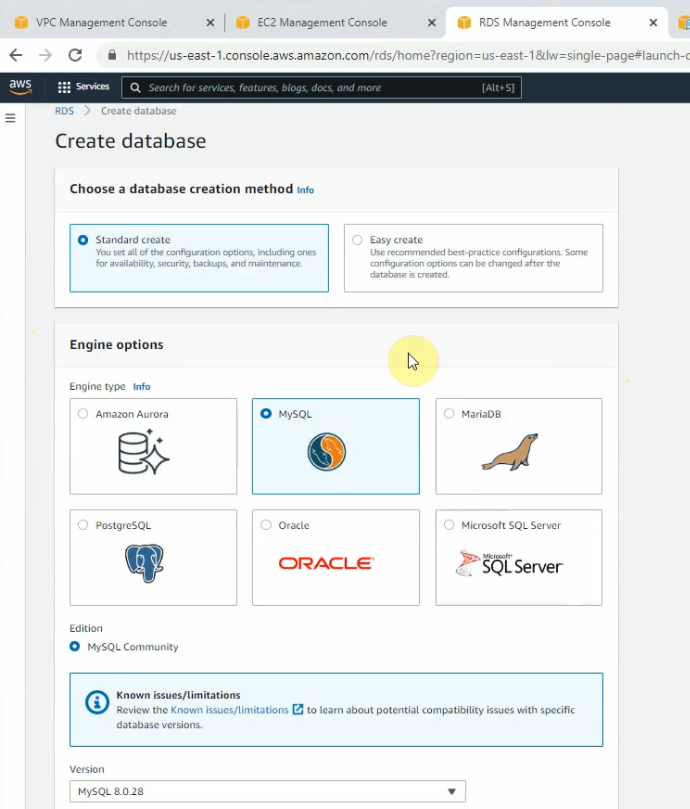
Choose the Free tier.
Enter wordpress on “DB instance identifier”, “master user name and password”
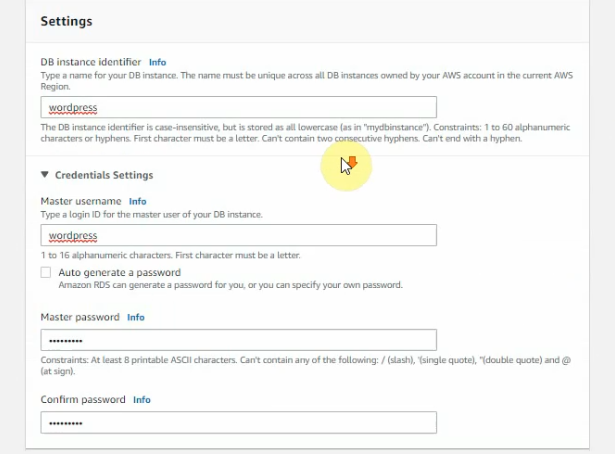
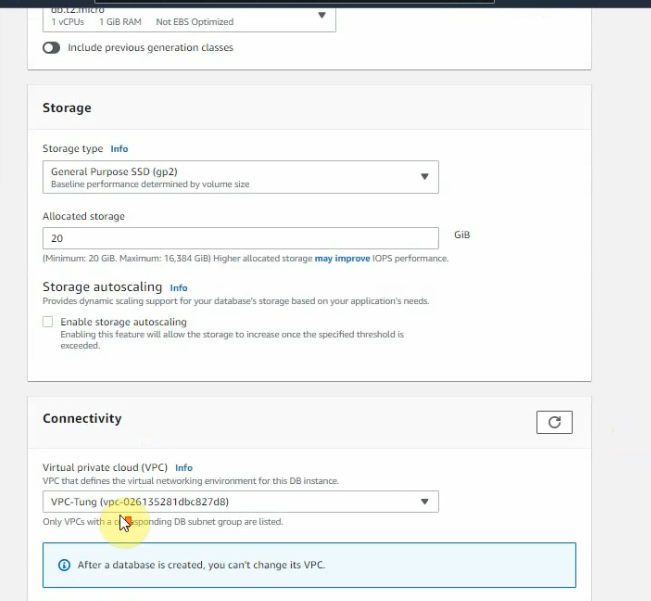
Public access is No.
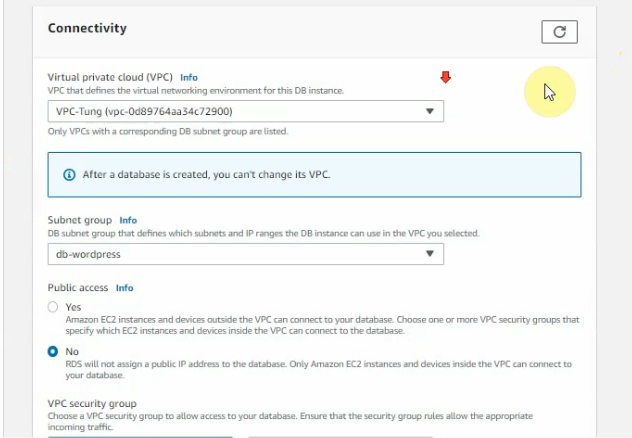
Choose the Availability zone as the following screenshot.
Enter “wordpress” on the initial database name.
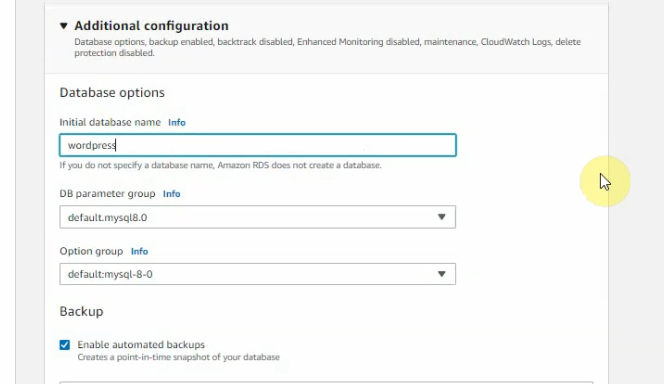
Backup retiontion period: 0, then click “Create database”.
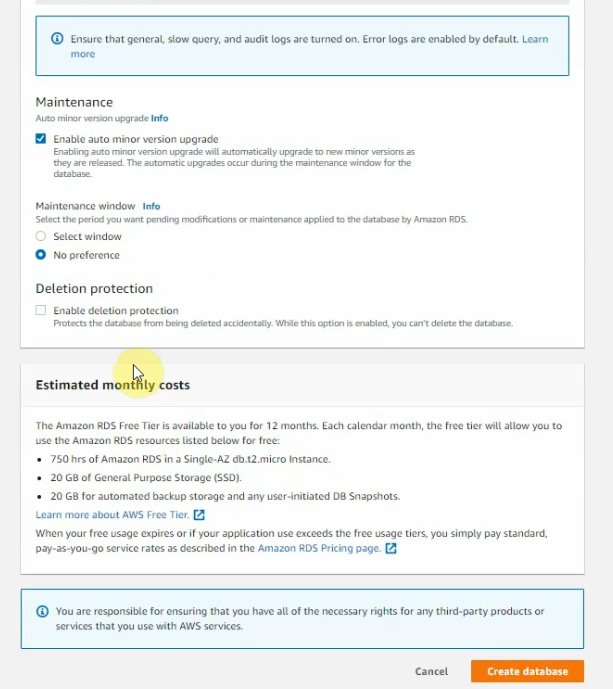
Wait a couple of minutes to completely create the database instance.
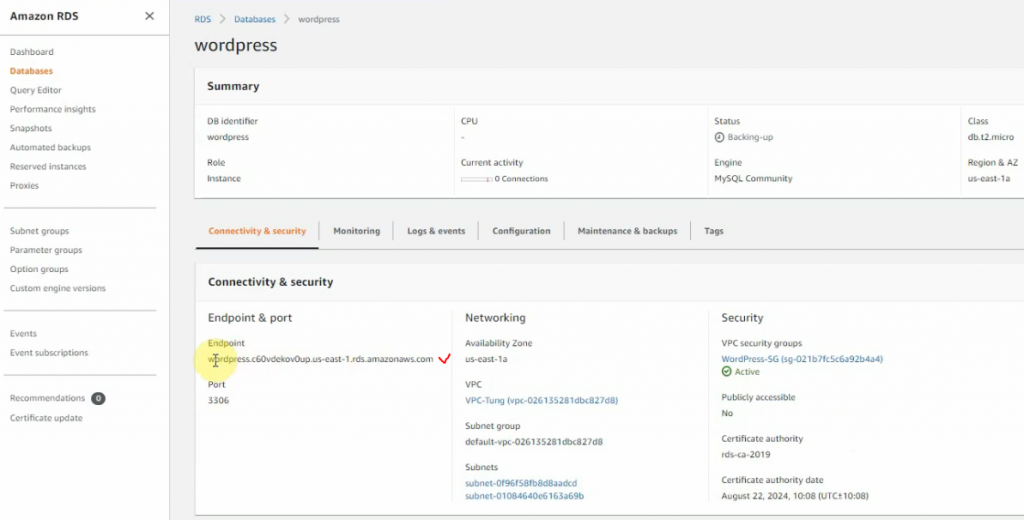
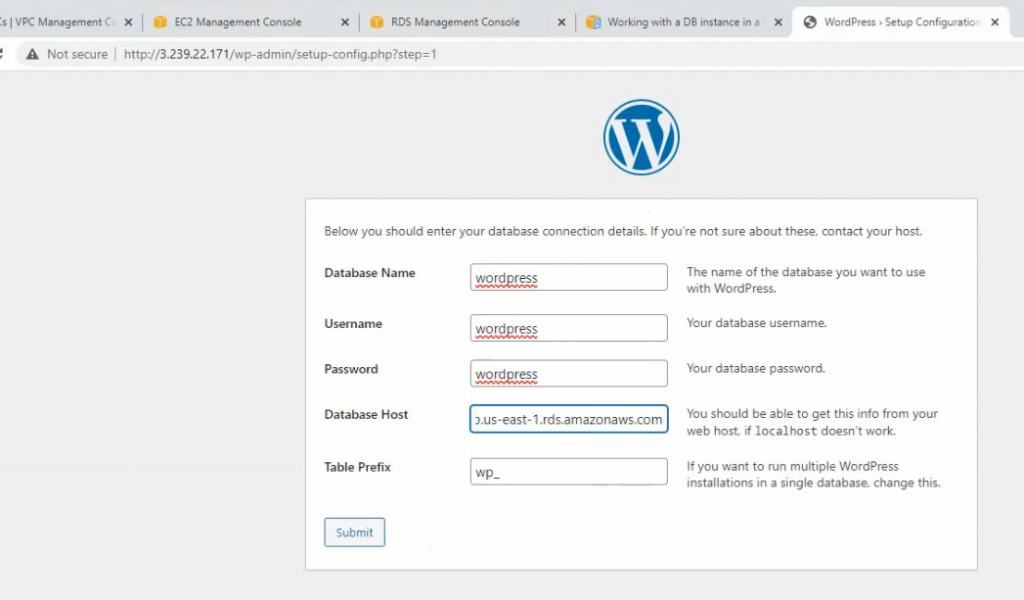
Access WordPress site via the public IP address of WP.
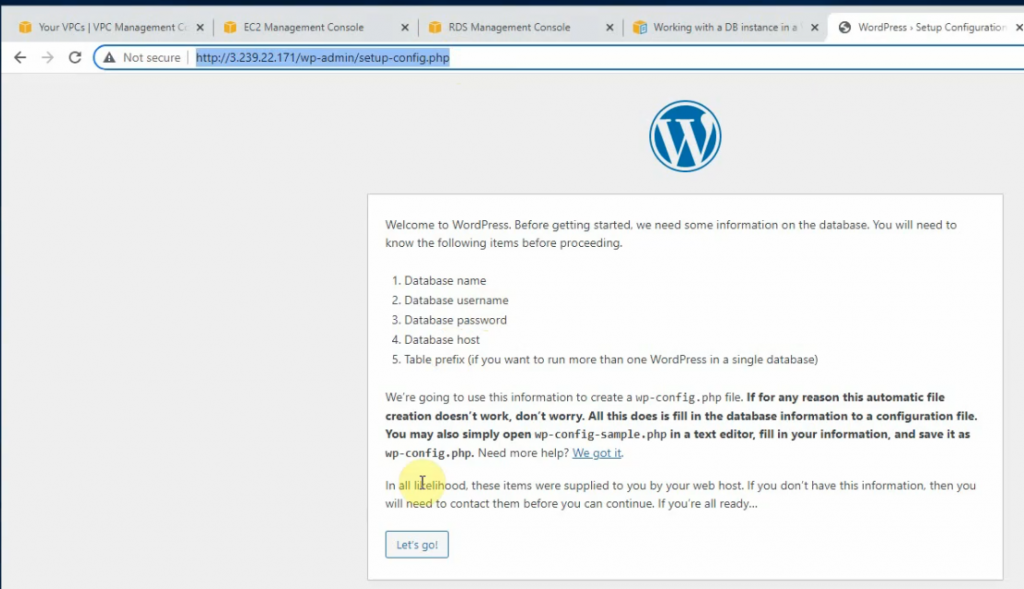
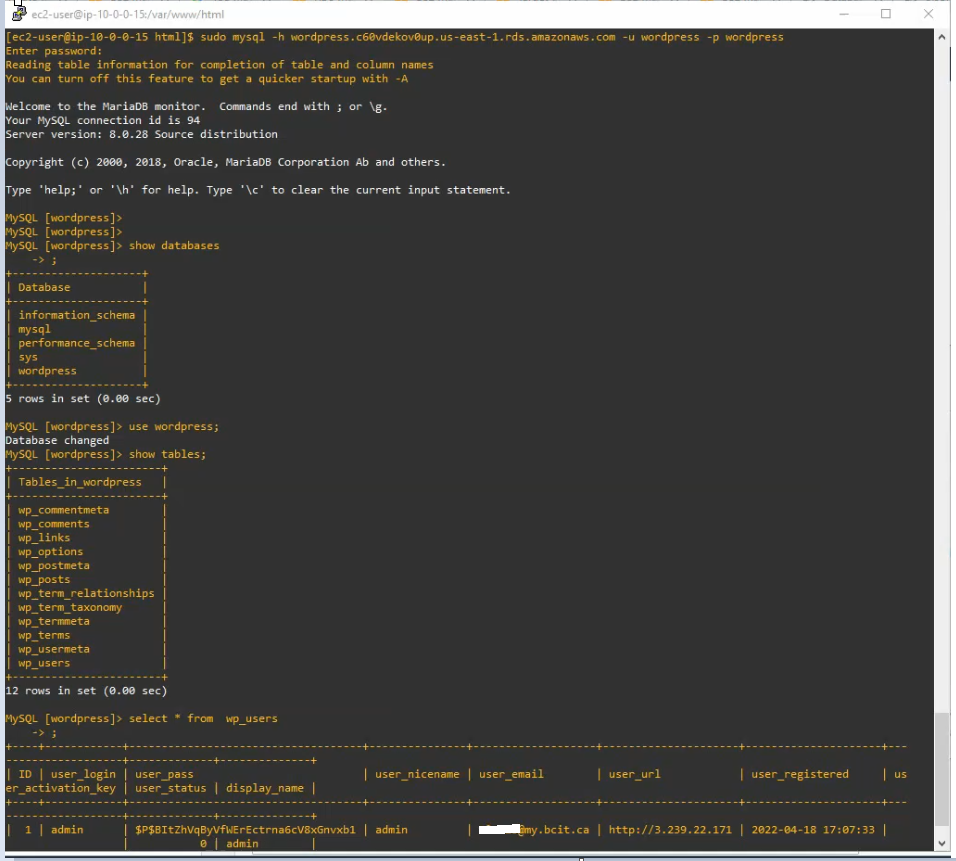
Database, username, password is wordpress.
Database Host is the endpoint address of the RDS database on AWS on the previous screenshot.
Click Submit.
Copy entire content, open SSH shell on Linux instance. Create a new wp-config.php under /var/www/html.
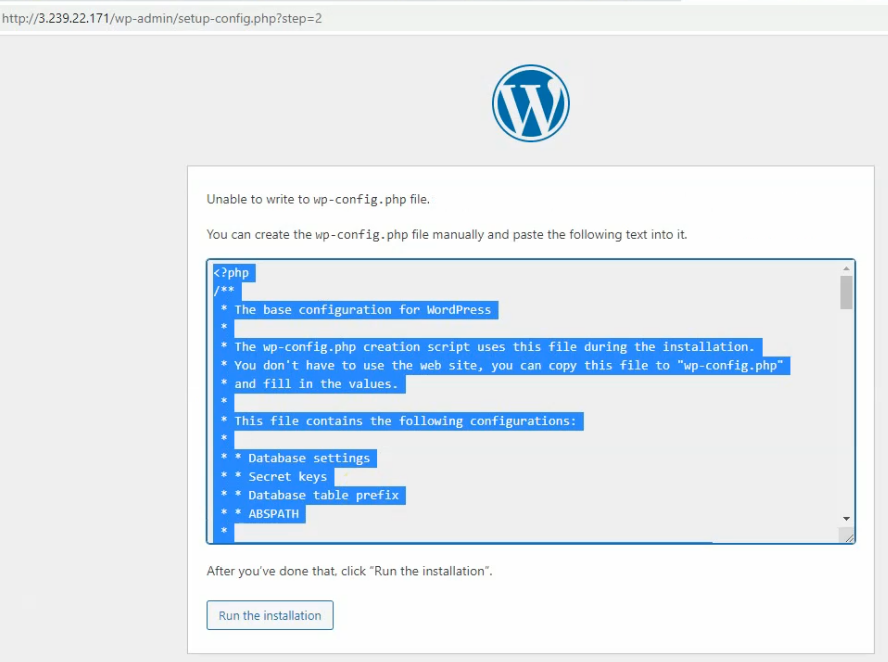
sudo nano wp-config.php 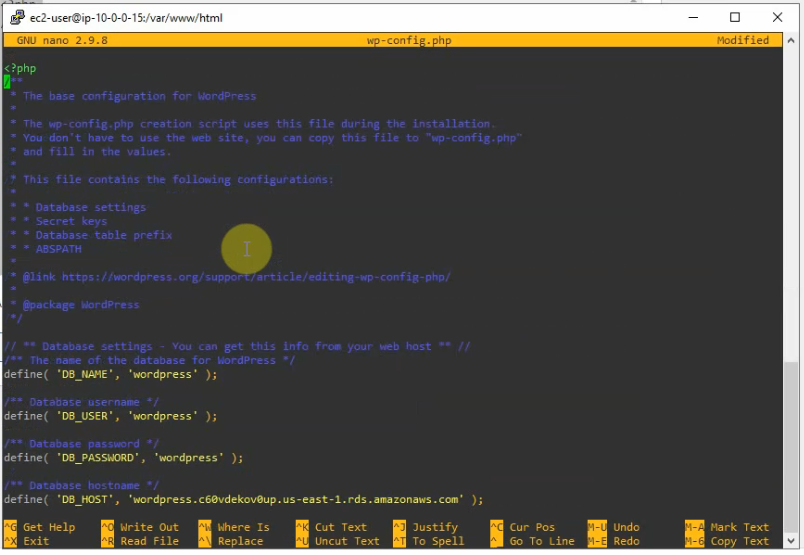
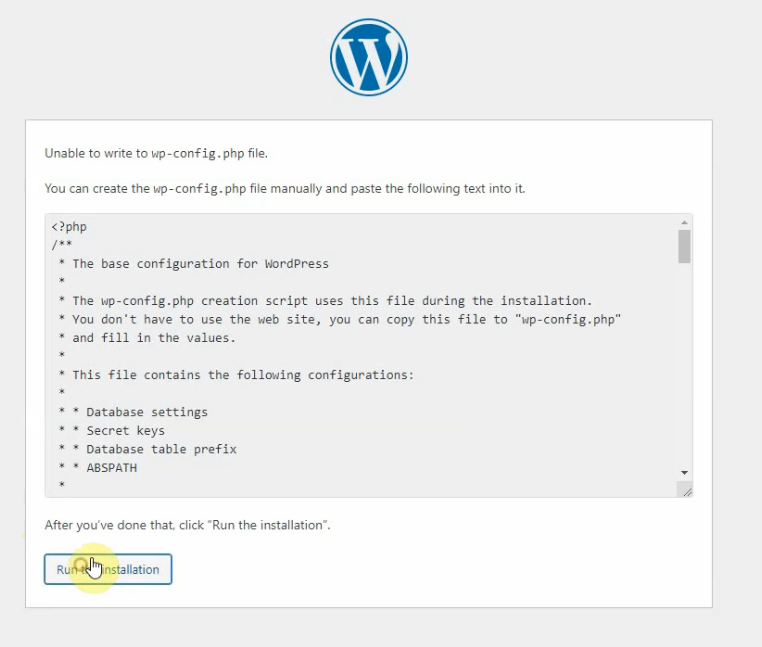
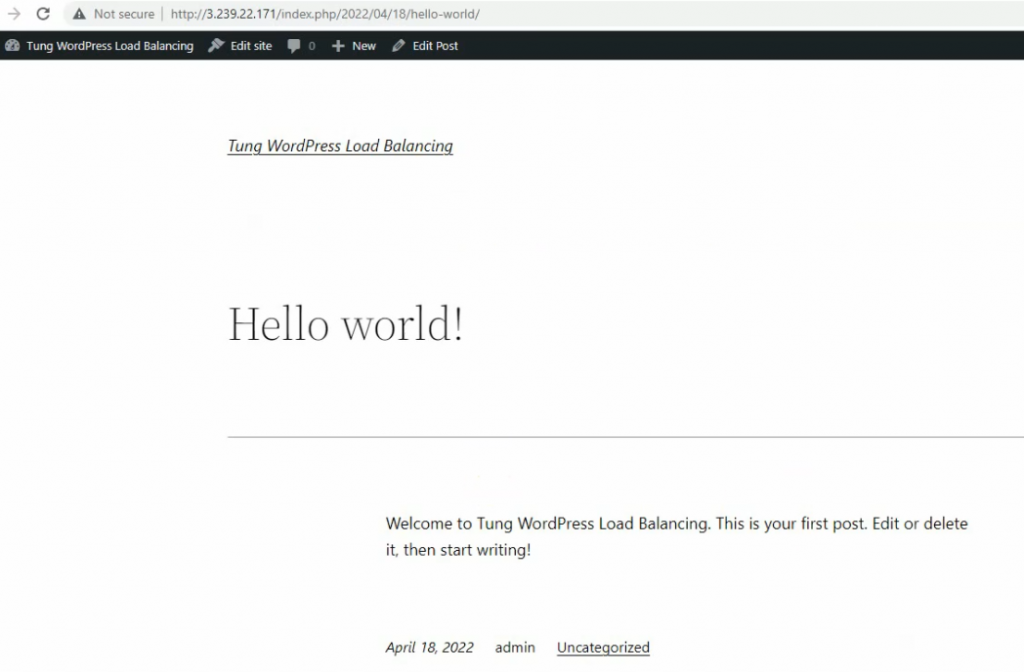
Back to WP web interface set up, click “Run the installation”.
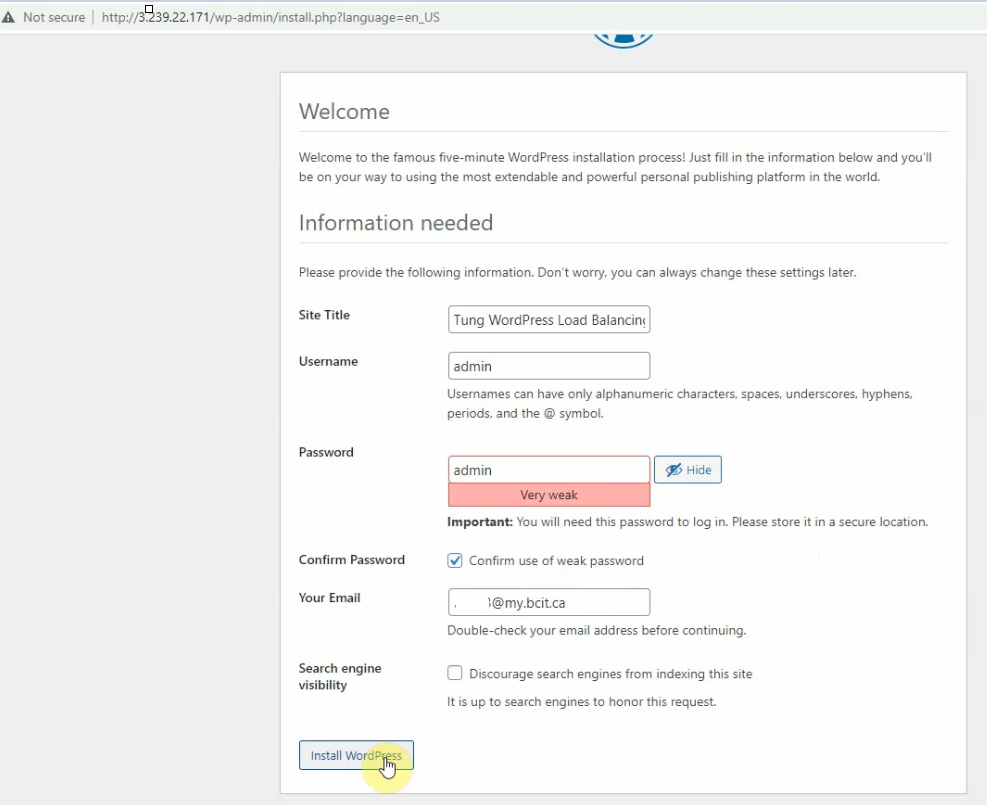
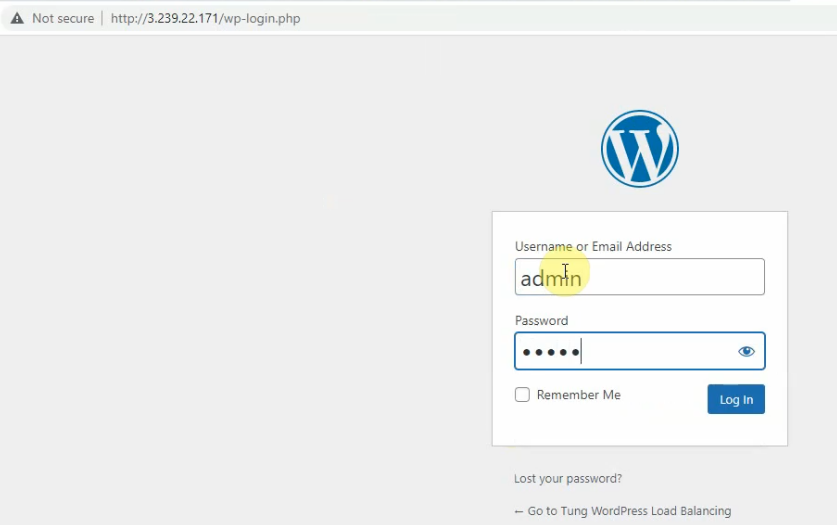
Log in WP.
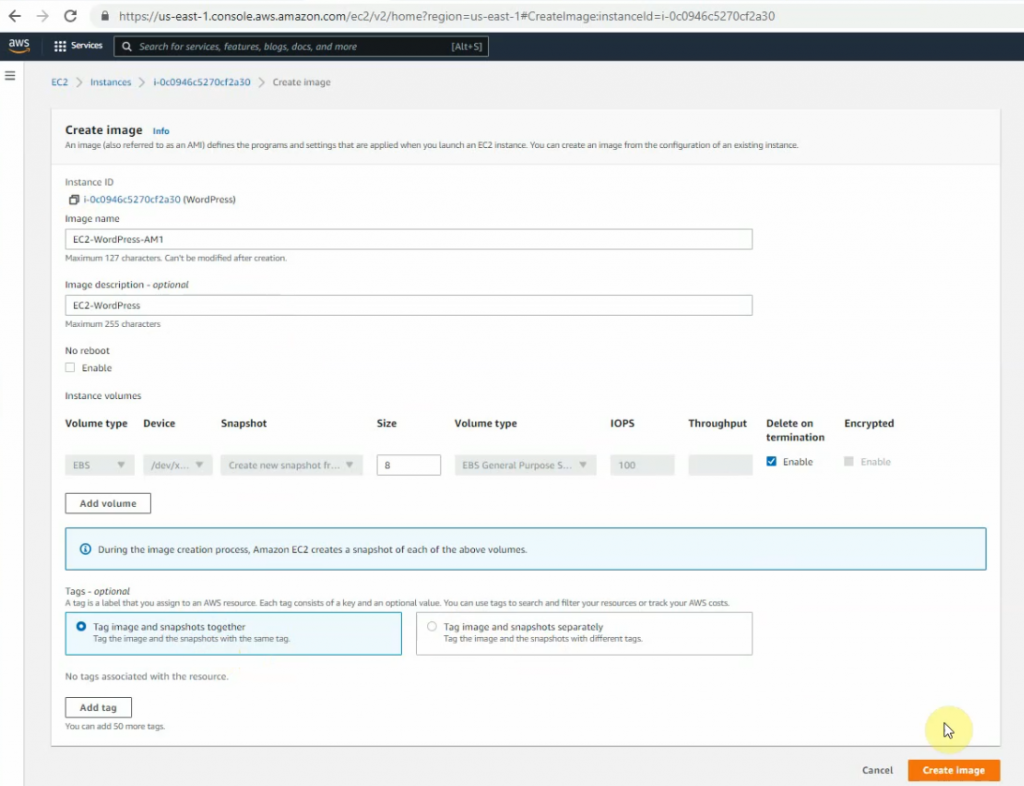
Now, create a new AMI image for this WP. Right-click the WP instance, on Actions – Image and templates – Create image.
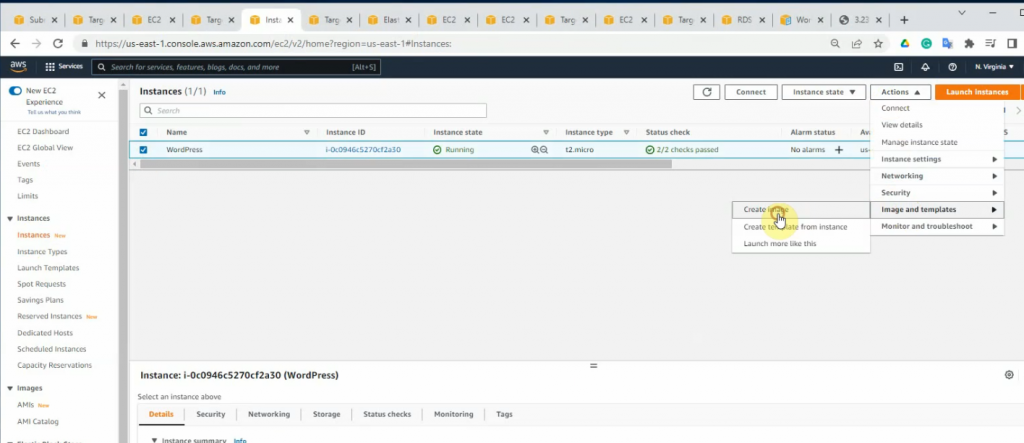
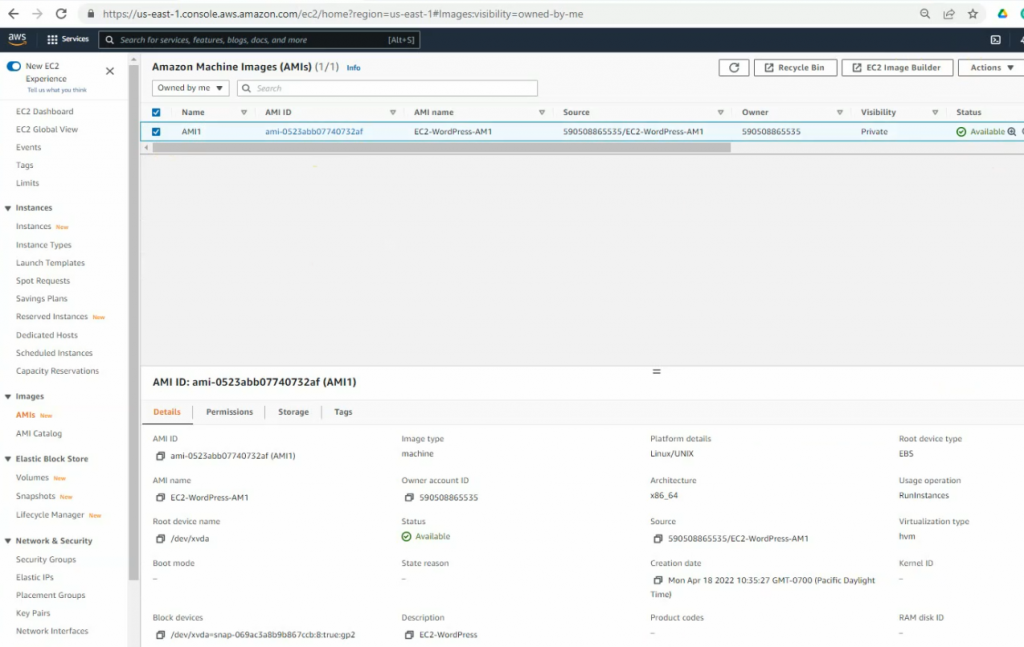
Right-click AMI. Click Actions – Launch an instance from AMI.
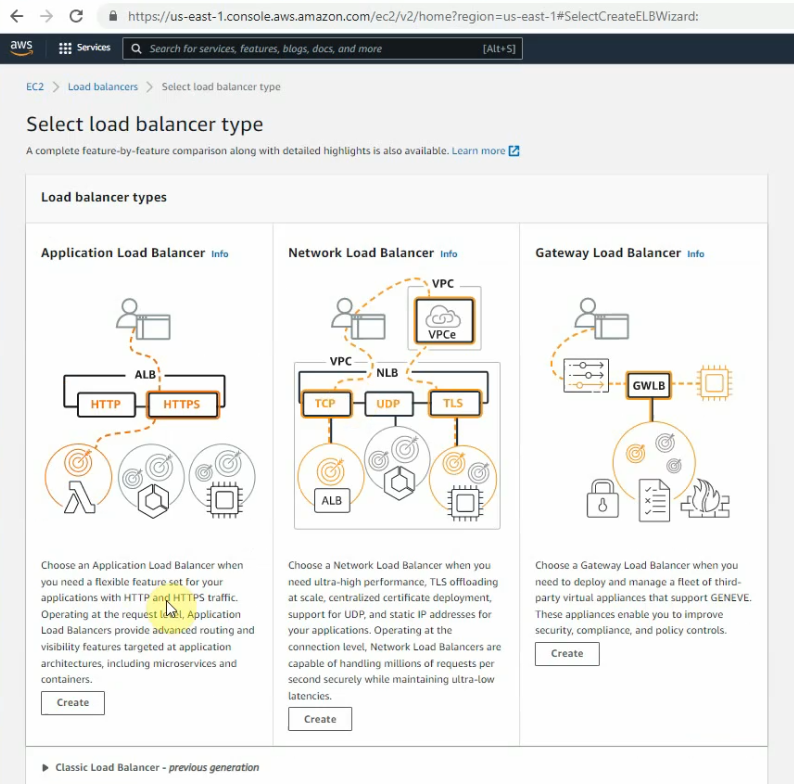
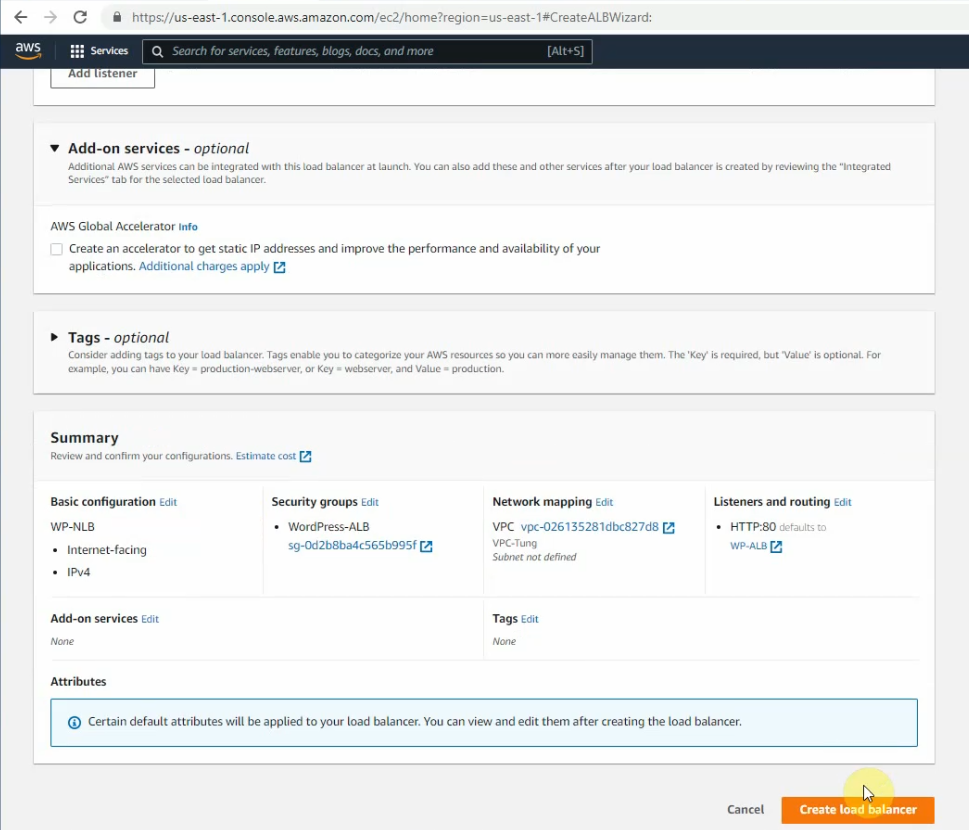
Go to the load balancer, and create a new application load balancer.
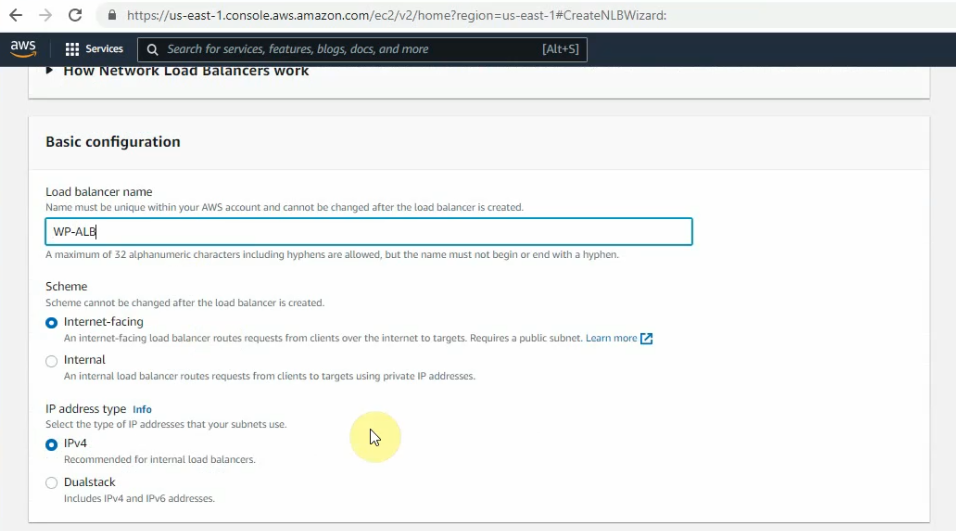
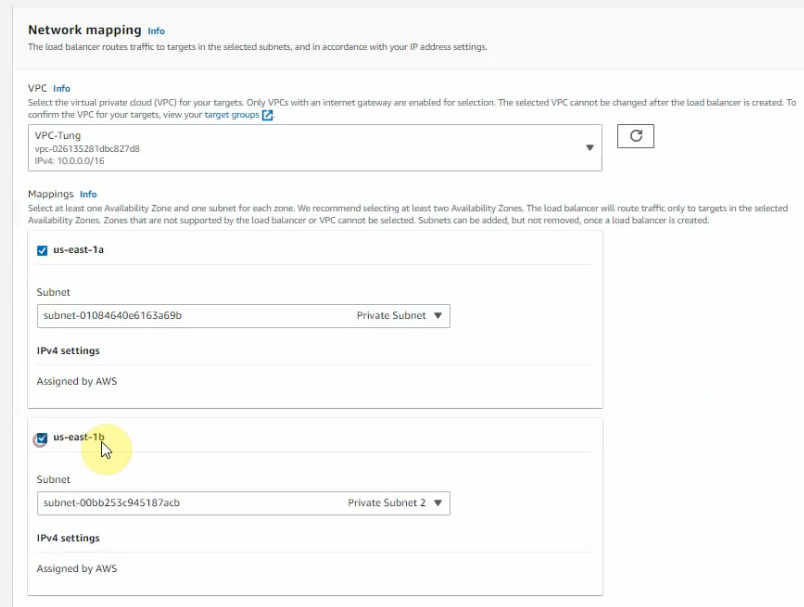
Create a new WordPress ALB SG. Allow HTTP from 0.0.0.0/0 on this Security Group.
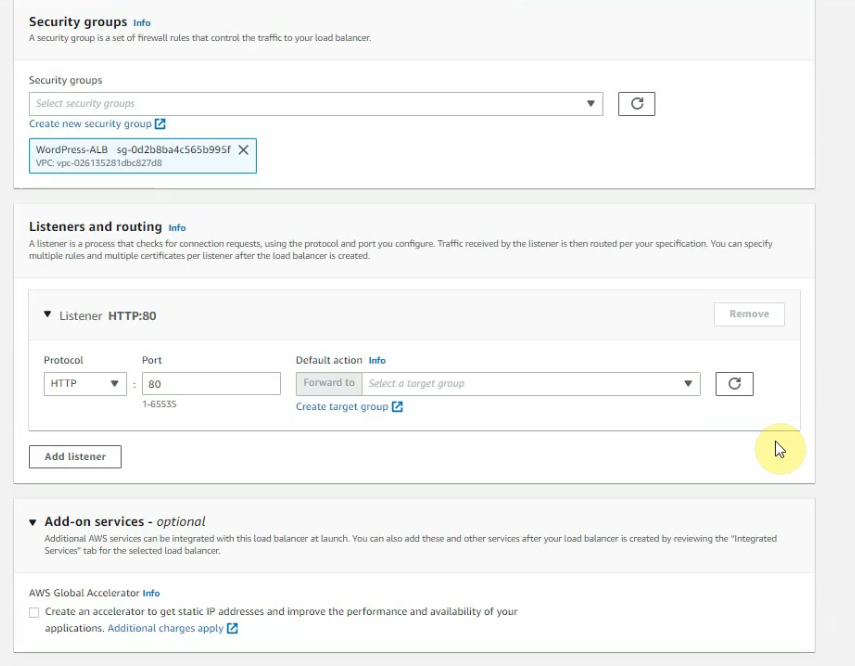
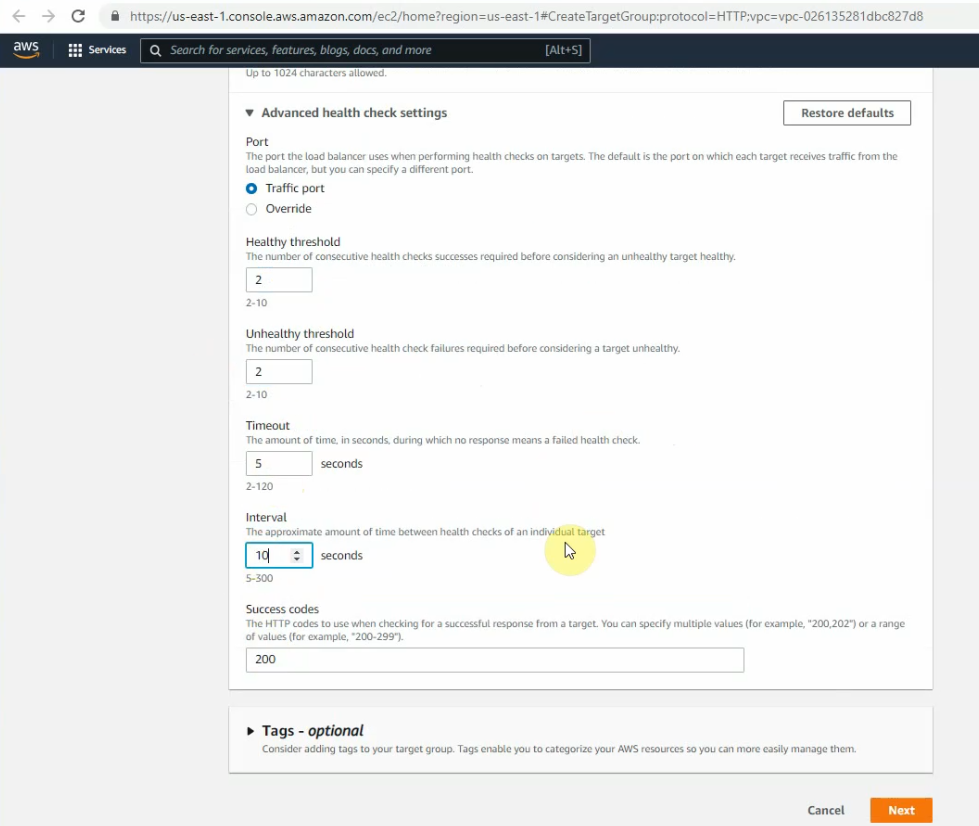
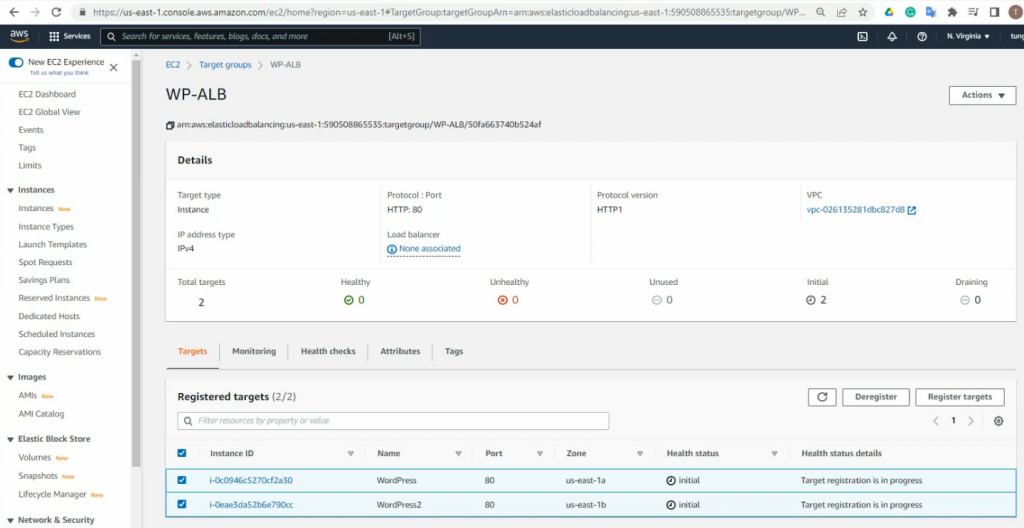
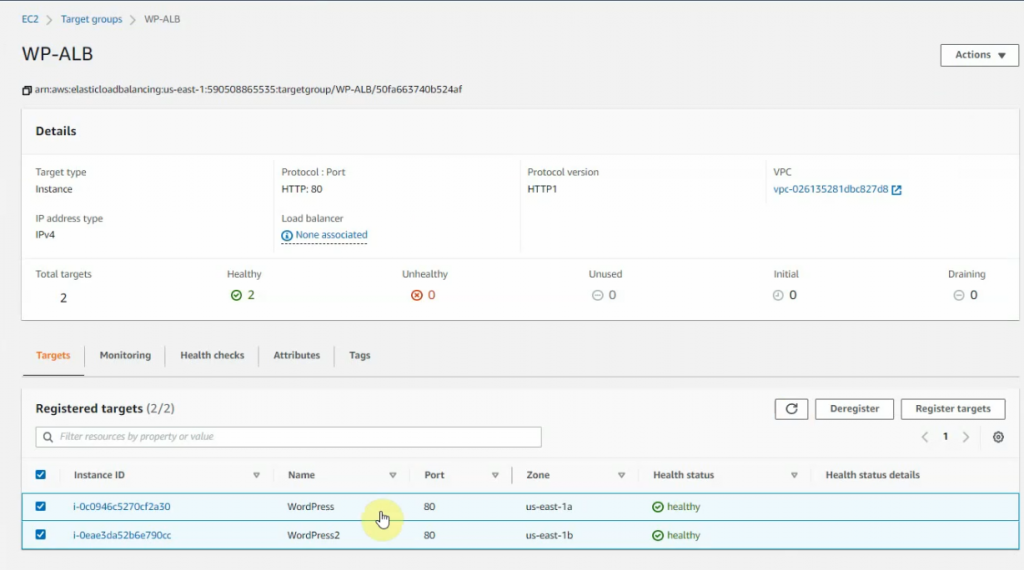
Create a target group.
Select “Instances”.
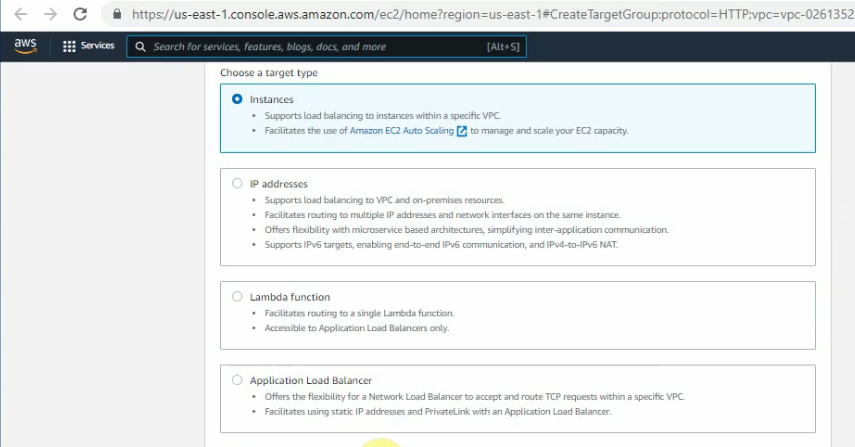
Enter “AP-ALB” on the target group name and checkhealth.html for the health check WP instance.
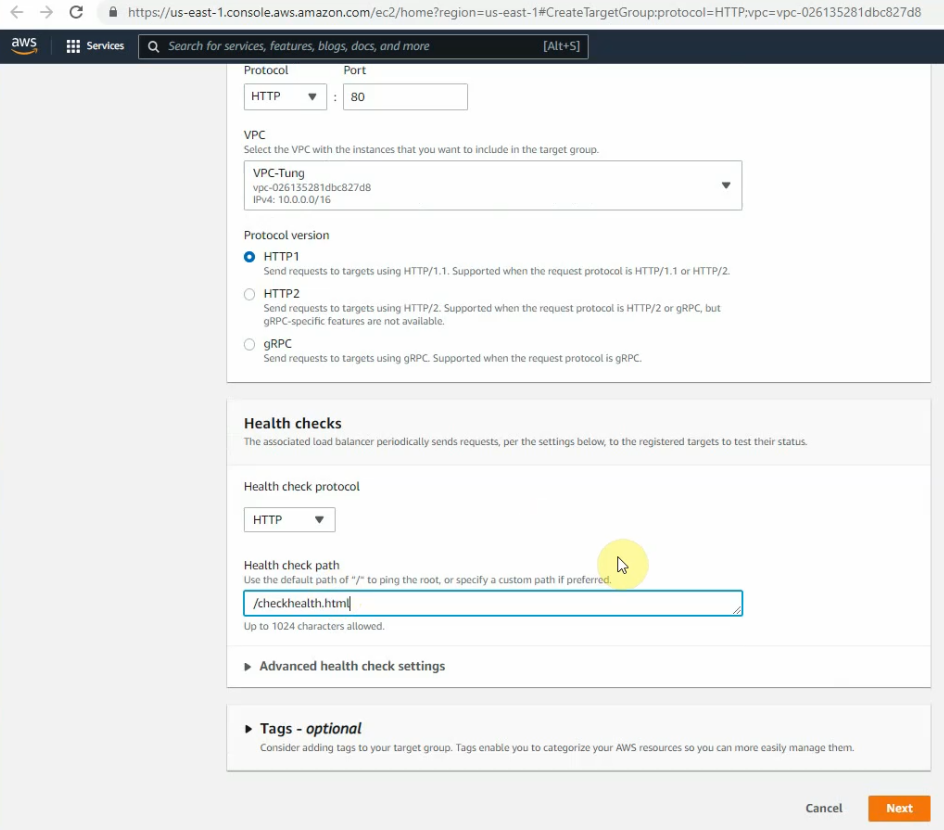
Change the settings as the screenshot below. Click Next.
Select both instance IDs and click “Include as pending below”.
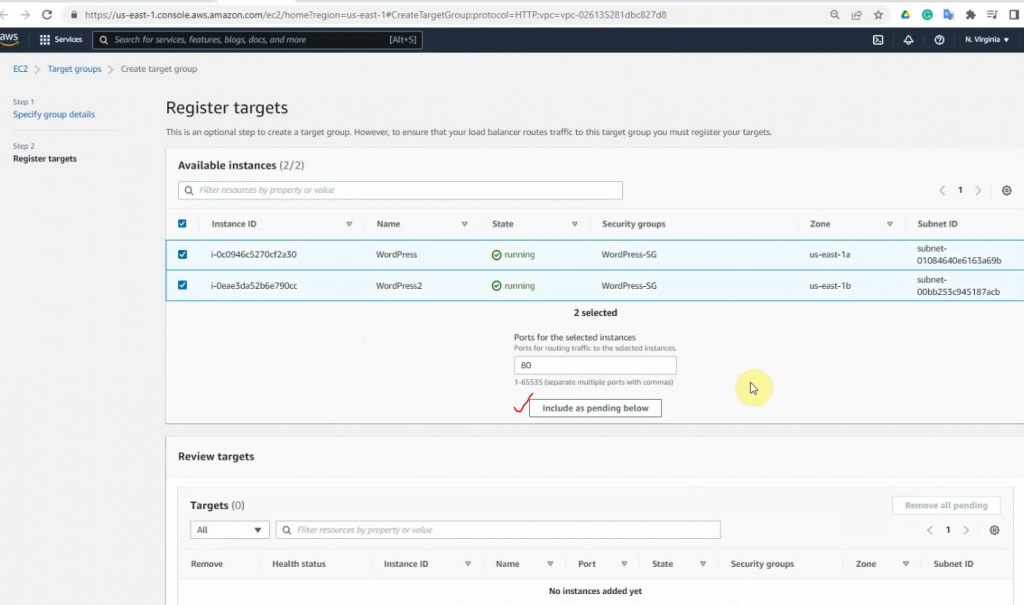
Create a target group.
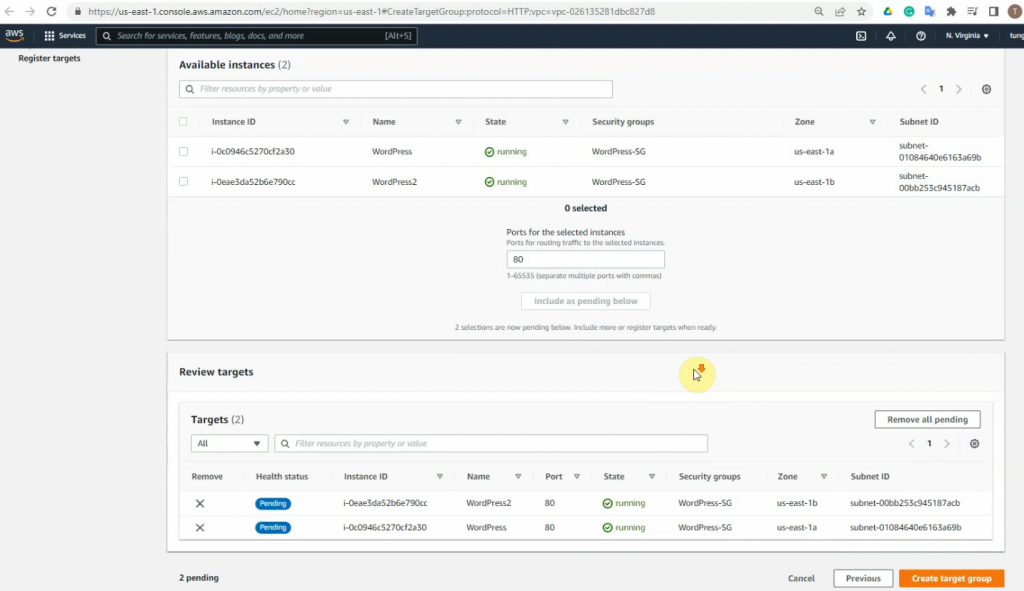
Back to the Application Load Balancer setup, choose the “WP-ALB” on the target group.
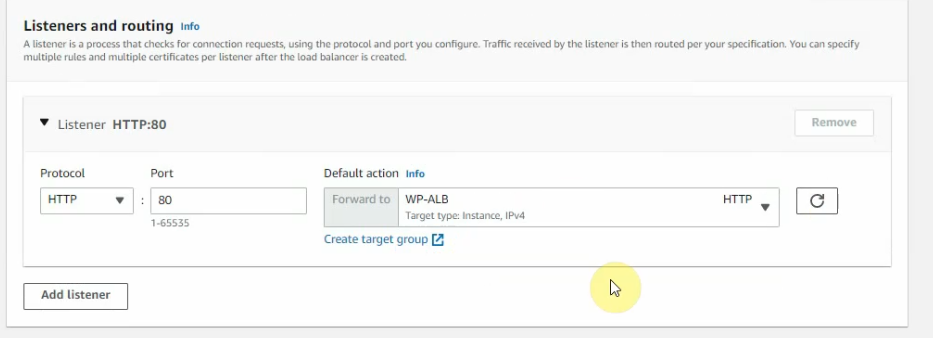
Create a load balancer.
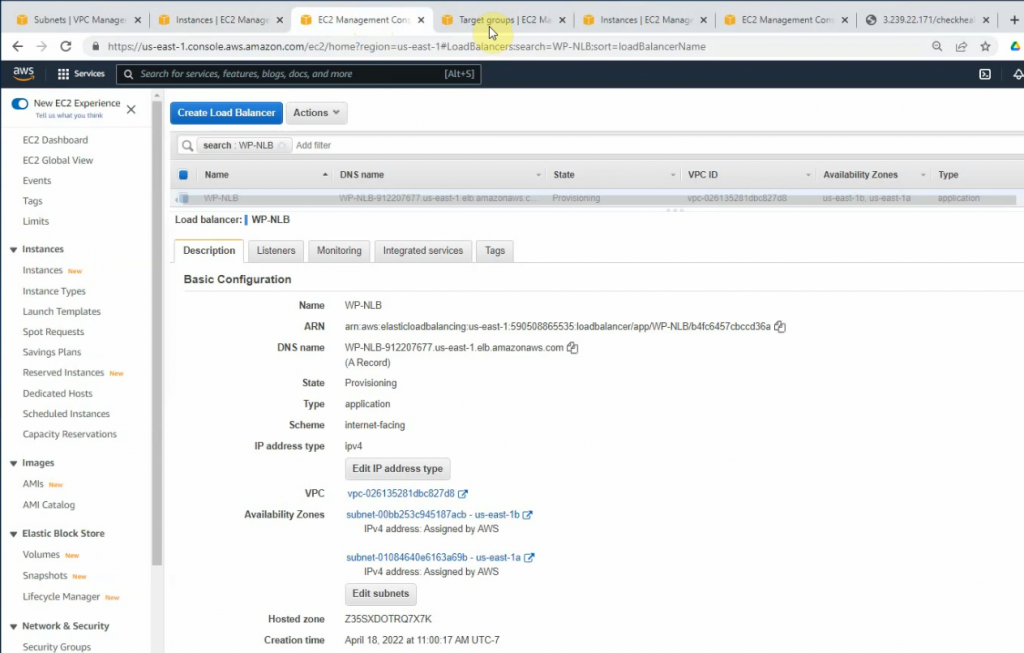
Wait a few minutes to see “Health status” is Healthy.
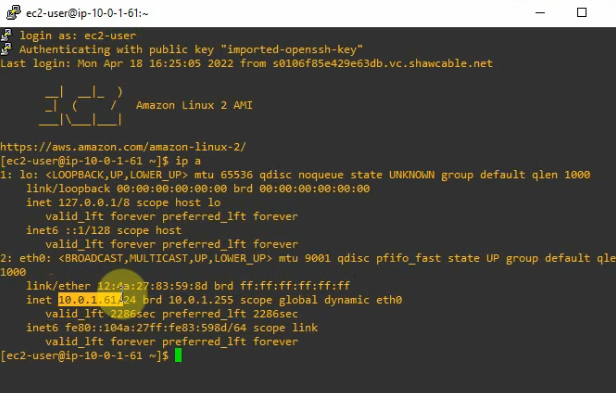
SSH to Linux instance on WordPress server 2.
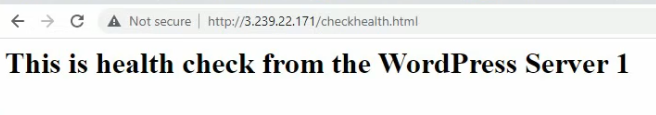
On WP1.
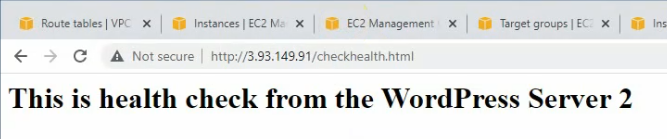
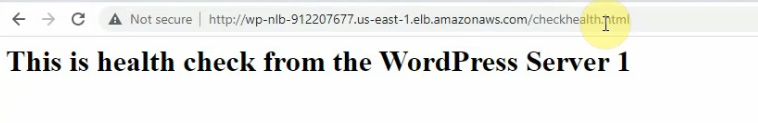
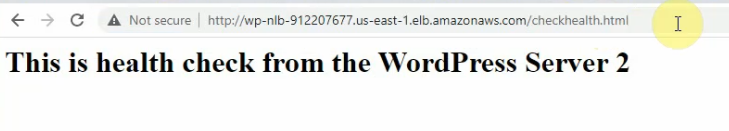
<h1> This is health check from the WordPress Server 1 </h1>On WP server 2.
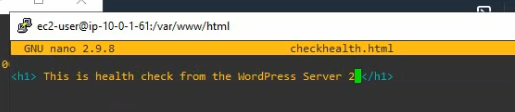
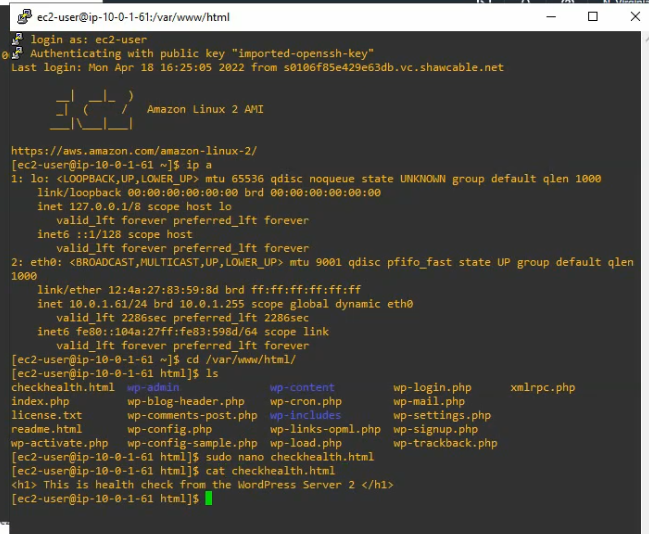
Start the httpd daemon.
sudo systemctl start httpd 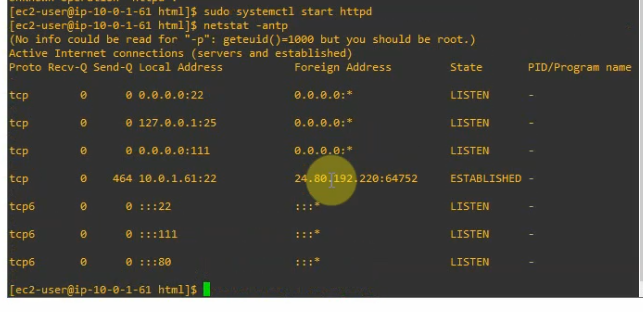
Do the same on WP1 to make sure the httpd daemon is running after making the AMI template.
Access WP health check on WP server 1.
Make sure both WP servers have Healthy status on WP-ALB.
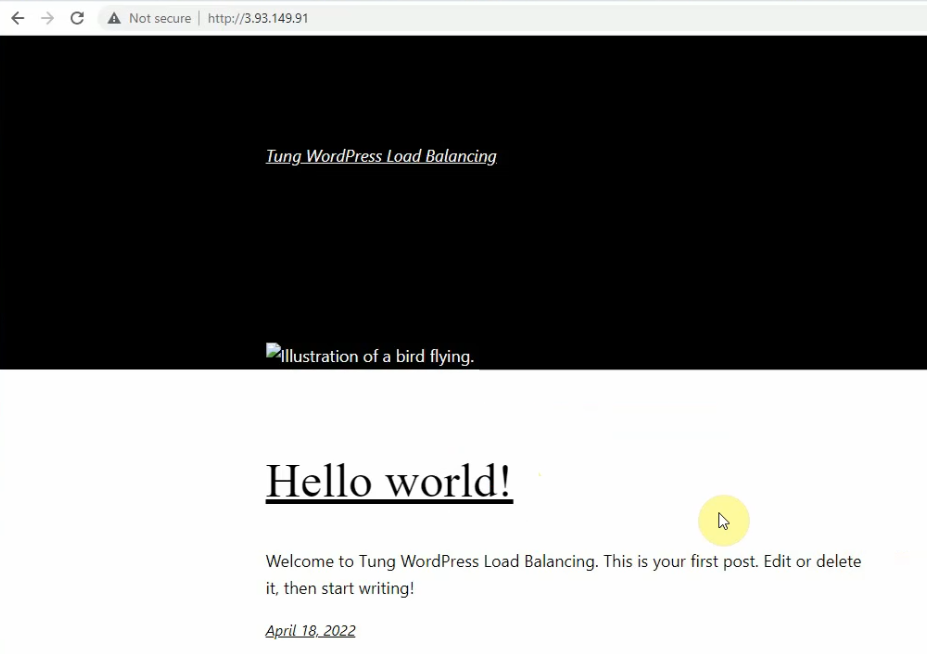
Copy the Amazon ALB link into your web browser.
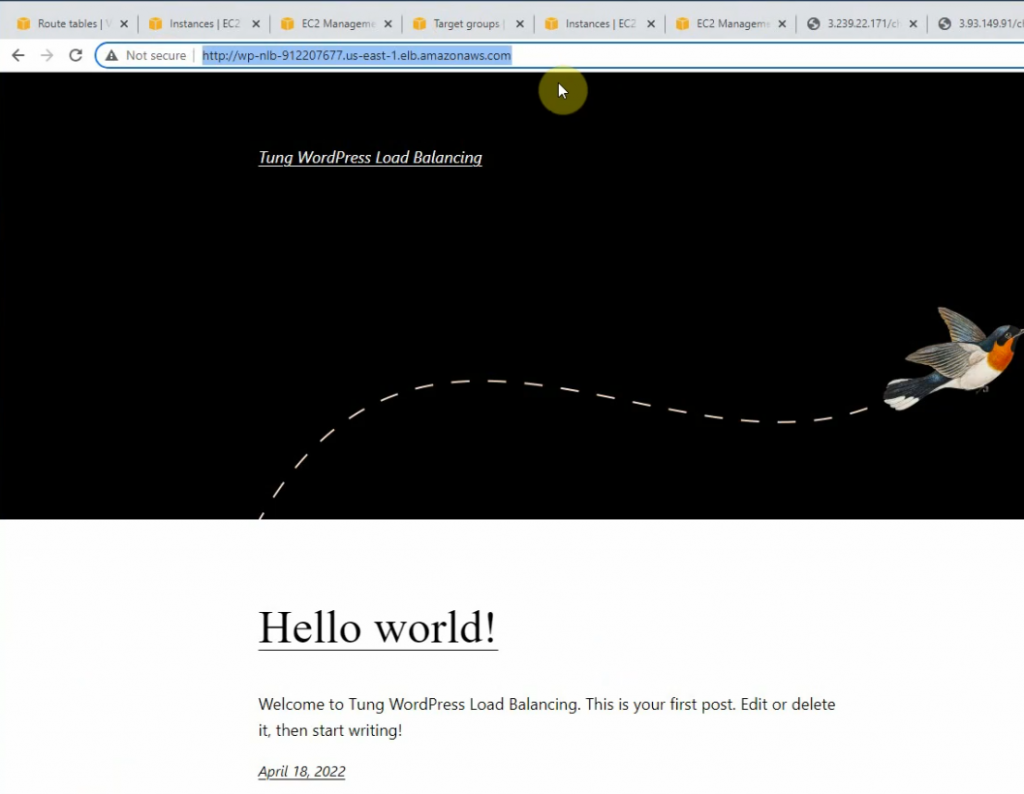
Refresh, it can be seen that the web traffic is loaded balancing on the WP server 2.
Check the connection from WP instances to the Amazon RDS database.
I will set up Amazon Route 53, Amazon CloudFront with a real domain name such as awsbigfan.ca, and load balancing via HTTPS (WordPress SSL certificate will be issued by Amazon), not HTTP. Also. I will configure a strict Security Group policy to strengthen security from WordPress to the Amazon RSD database in the next labs.
