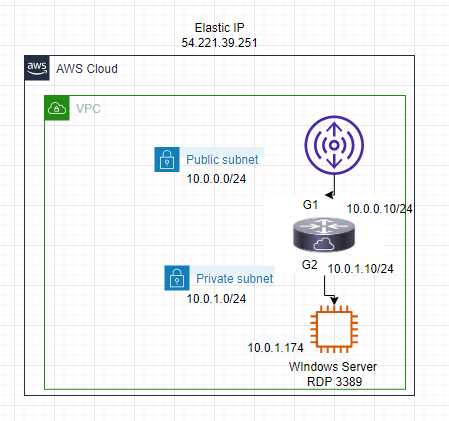
Below is a diagram that I have used to deploy this lab.
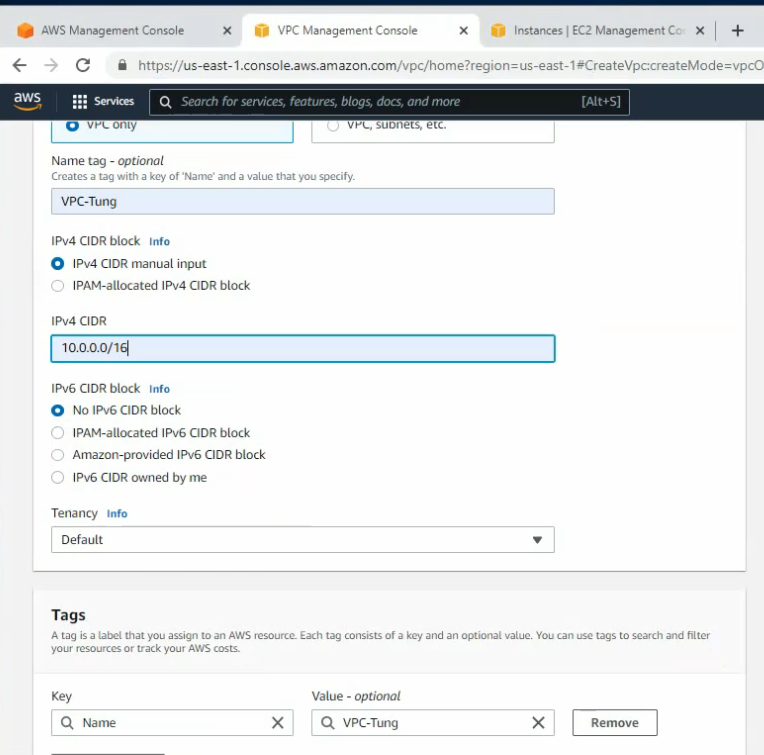
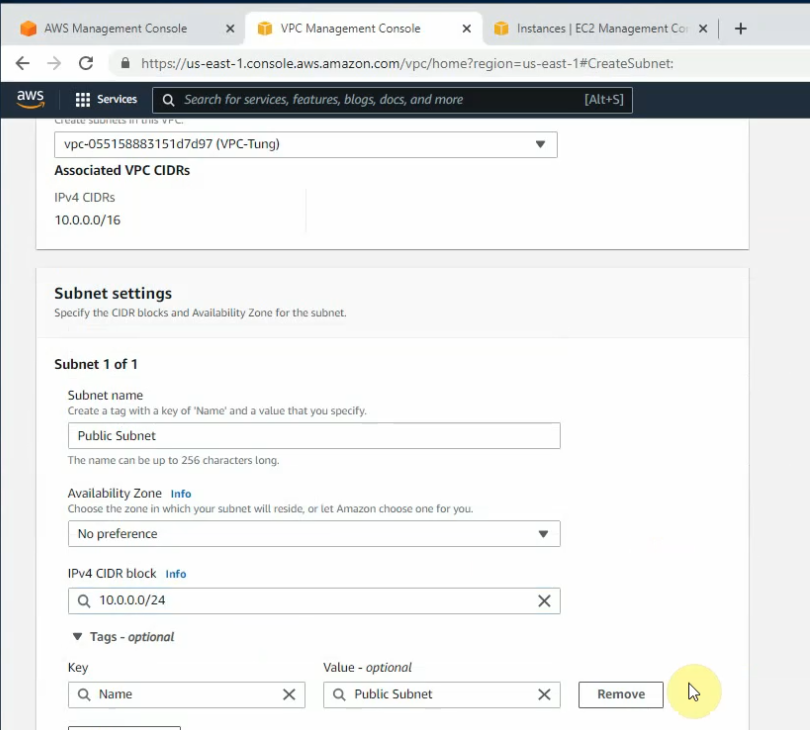
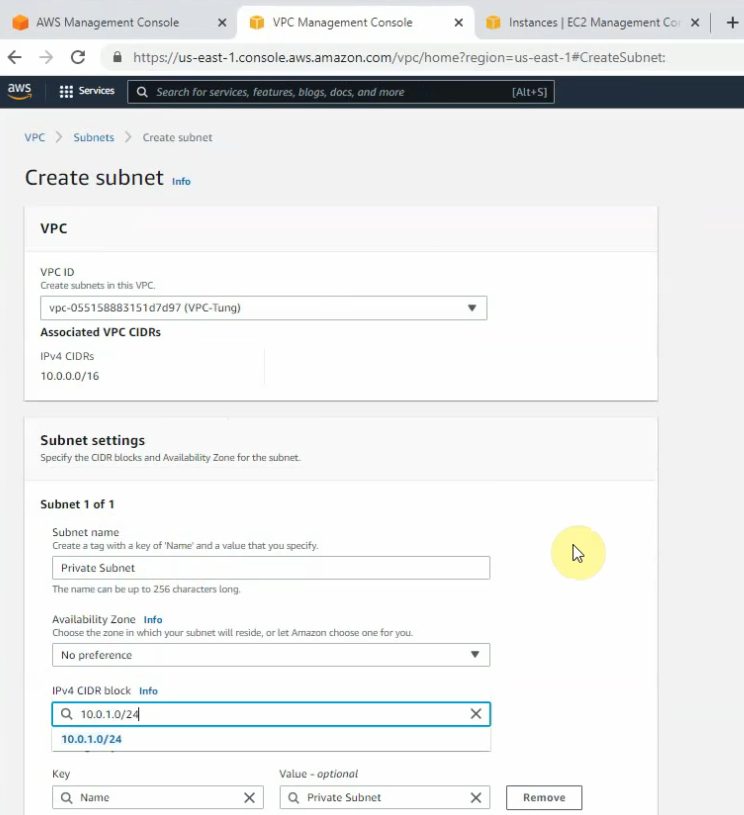
Create a new VPC.
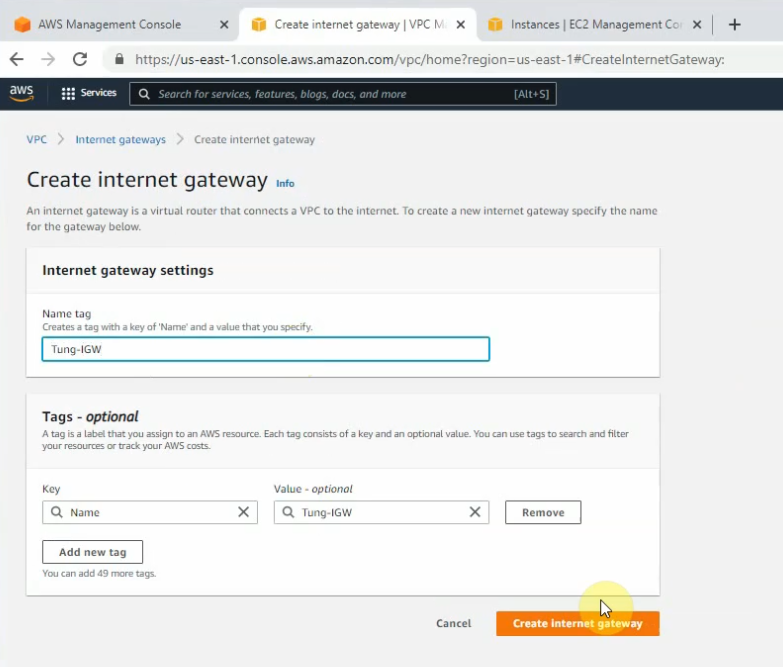
Create and attach a new Internet gateway to your VPC.
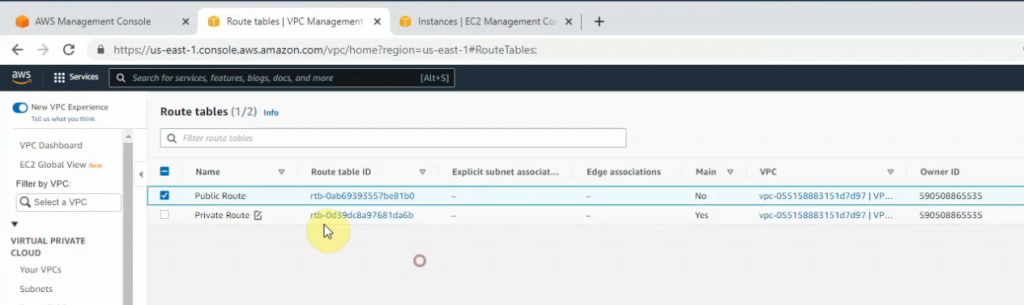
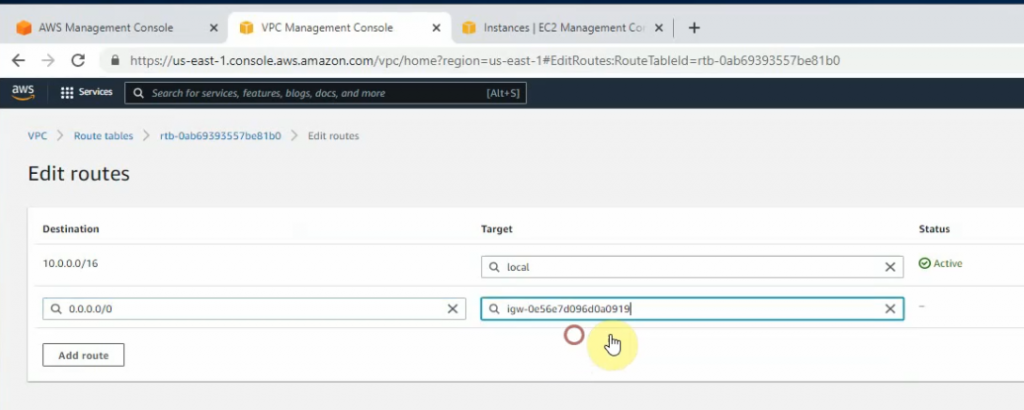
Create a new route to 0.0.0.0/0 to your Internet gateway.
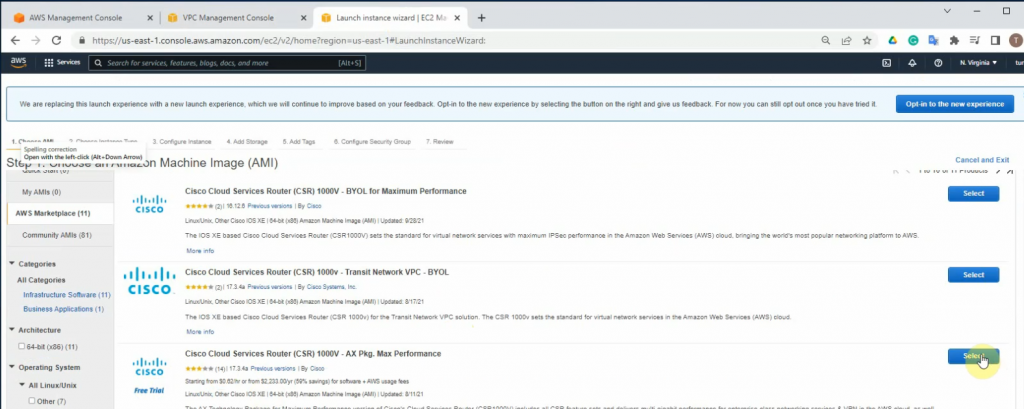
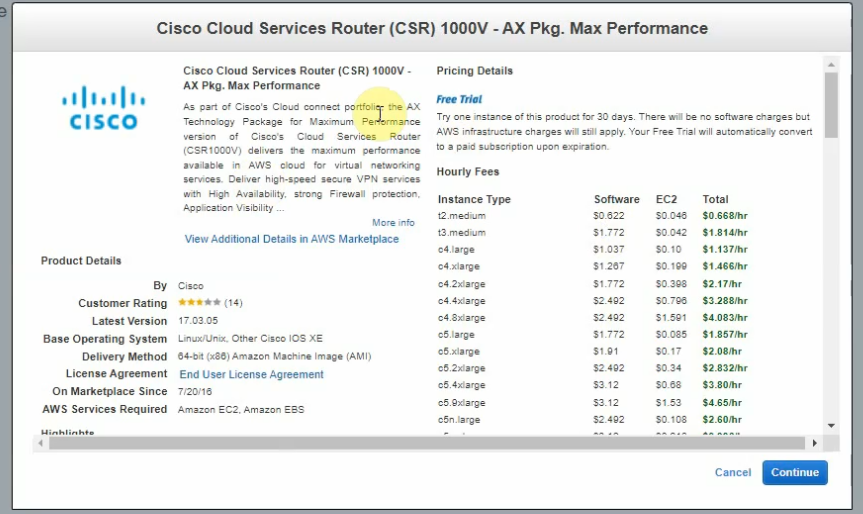
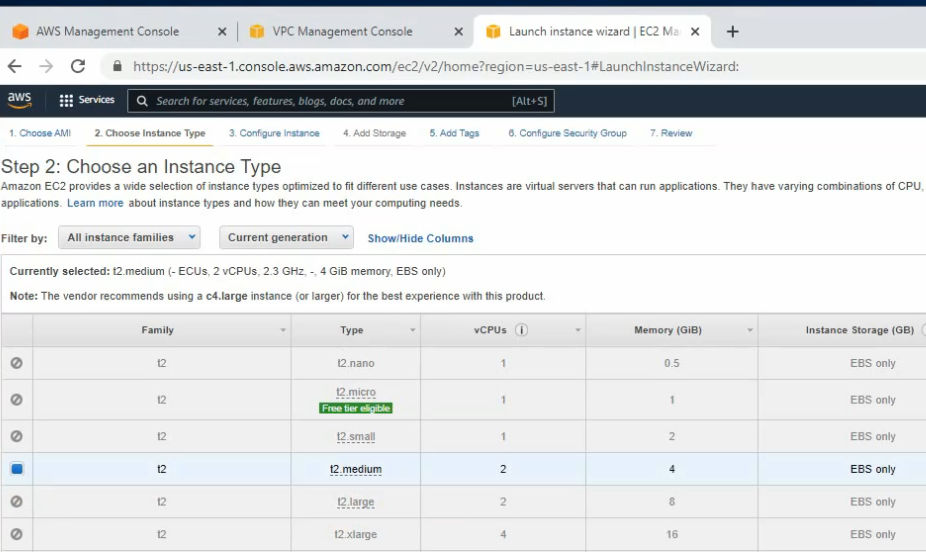
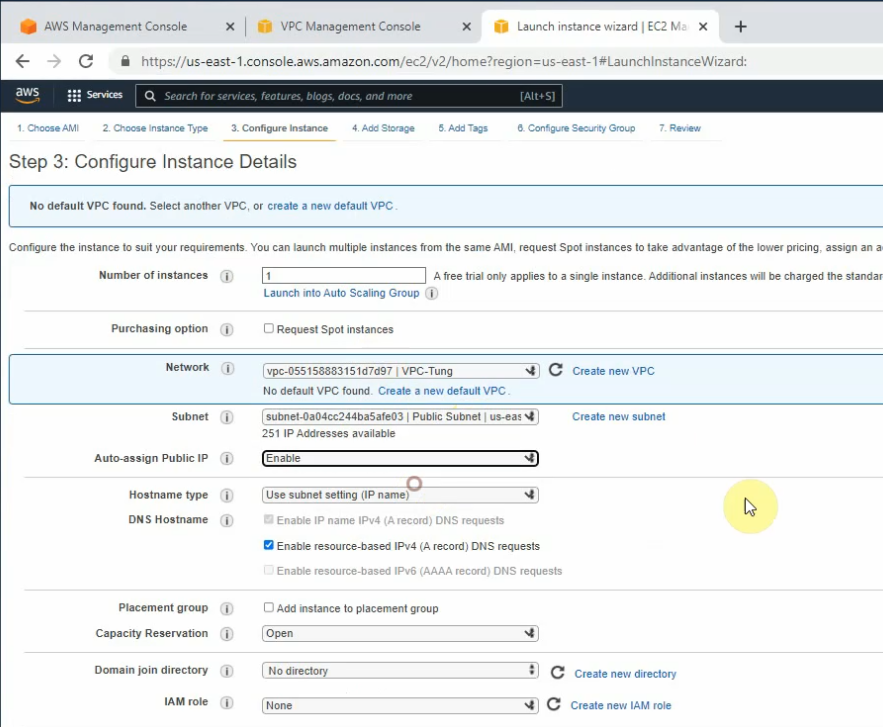
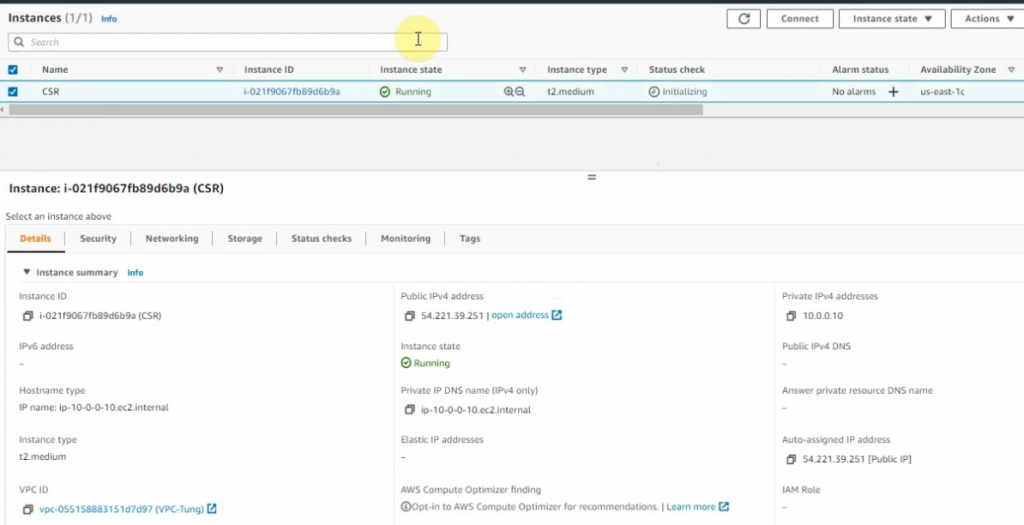
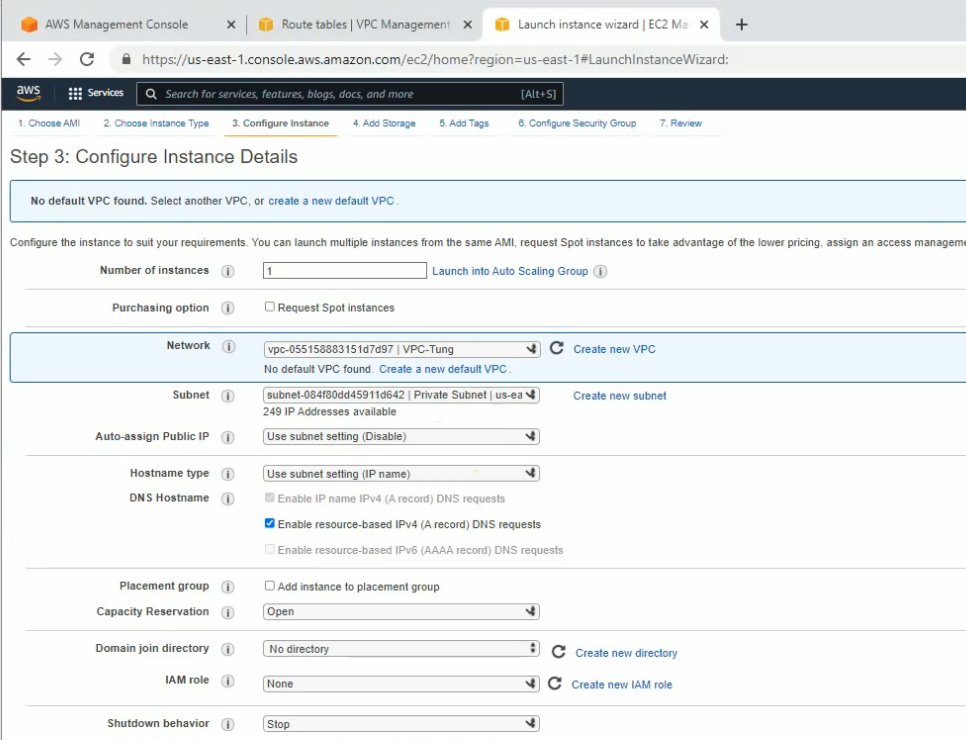
Launches a new CSR instance.
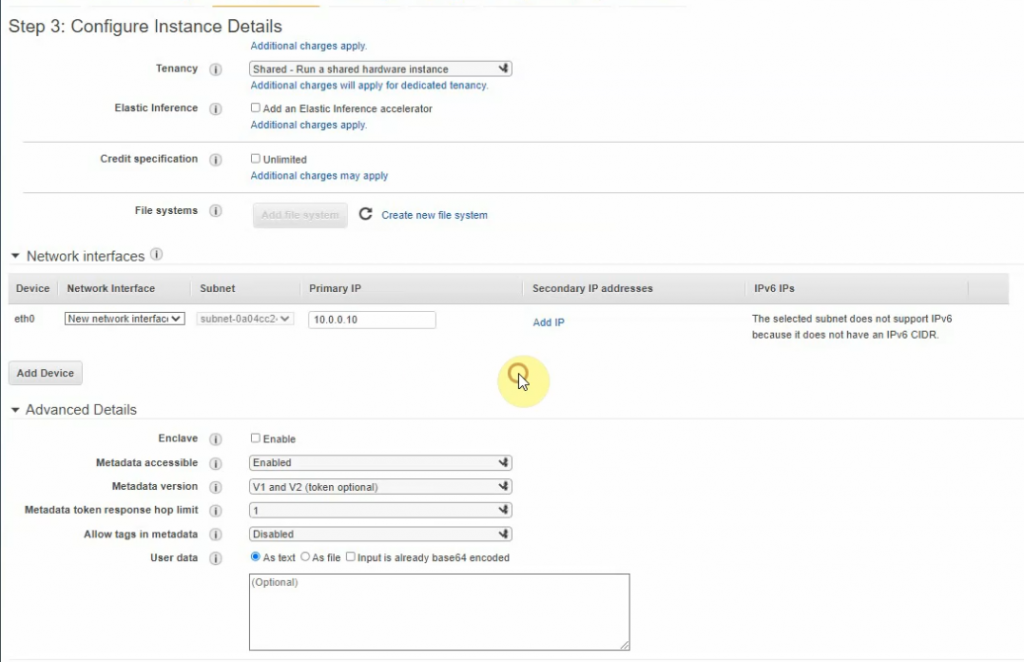
Enter 10.0.0.10 on Primary IP setting.
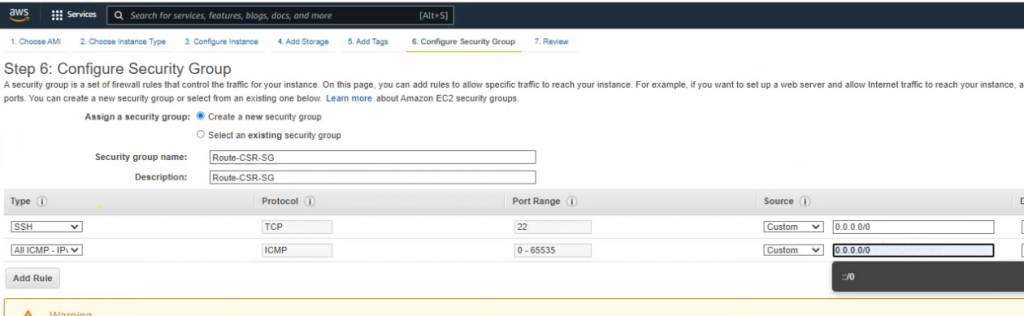
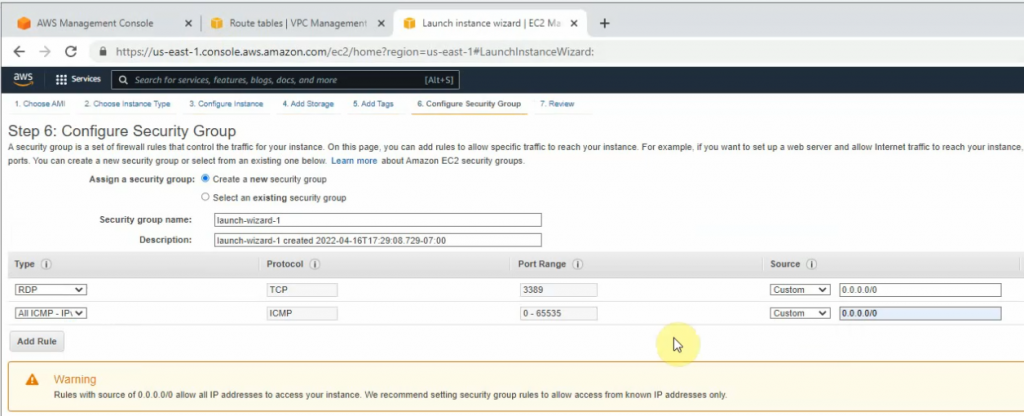
Security Group.
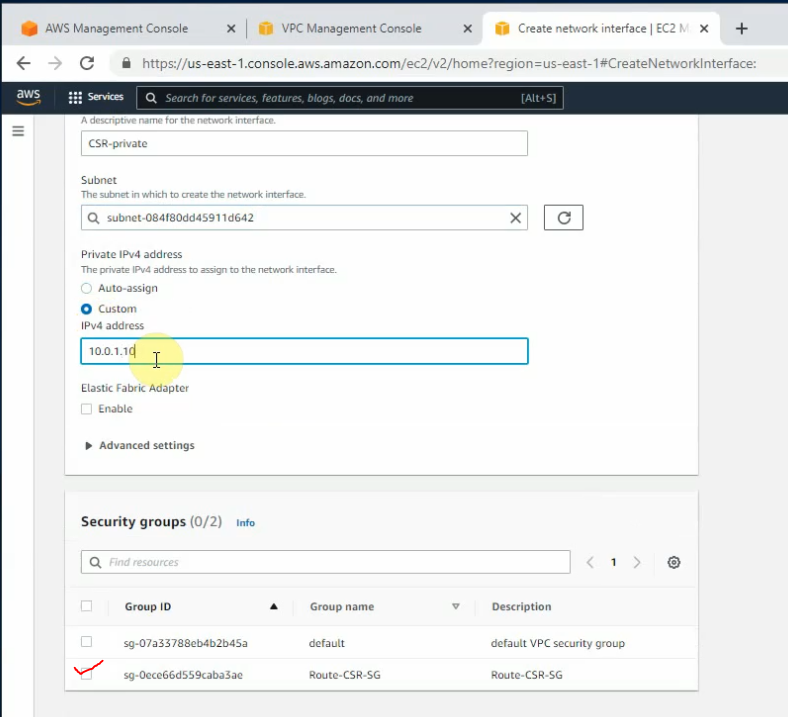
Go to Network interfaces, and create a new network interface for Router CSR.
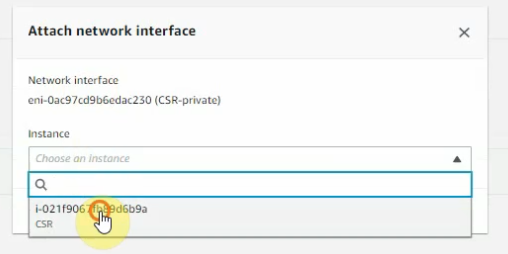
Then attach this network to Router CSR.
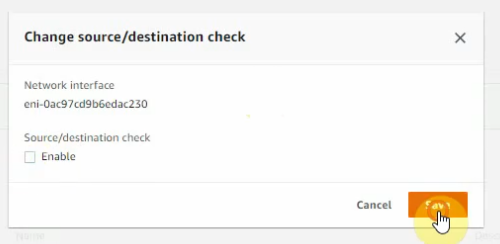
Disable “Change/source/dest check” for both Cisco CSR interfaces.
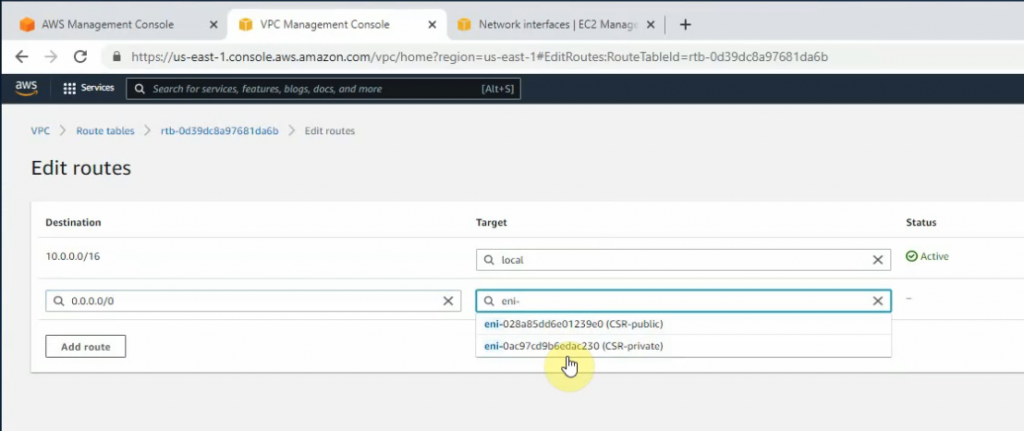
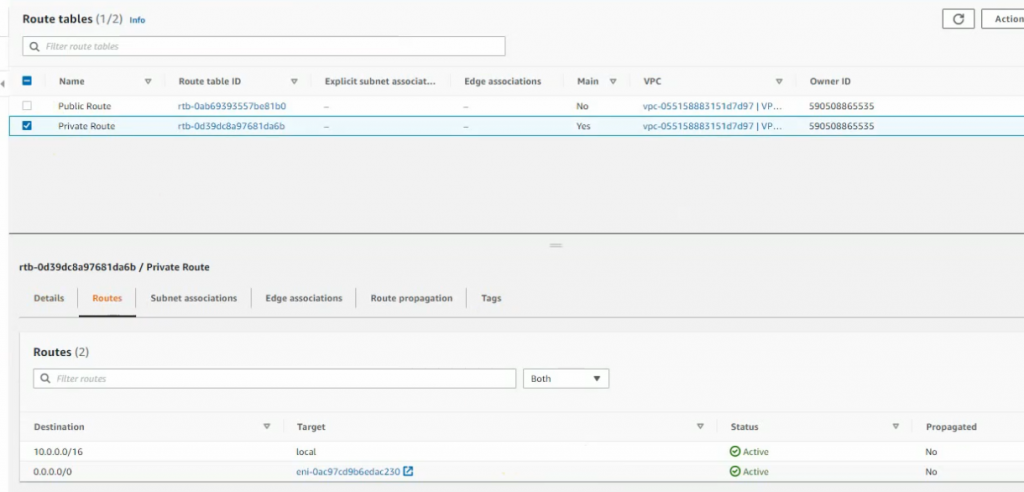
Back to route tables, configure the new route to the private Cisco CSR interface.
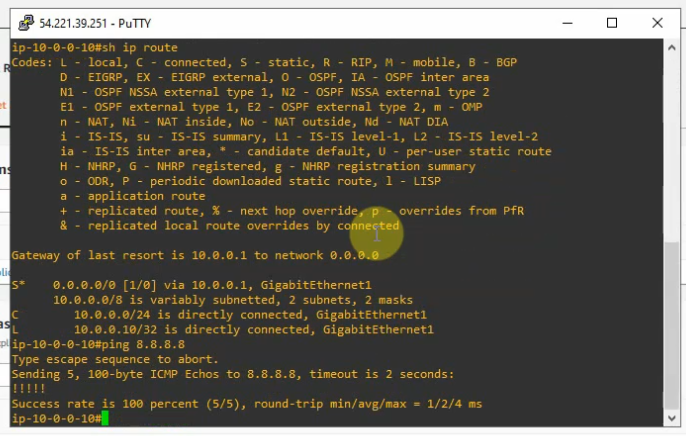
SSH from putty to Cisco Router.
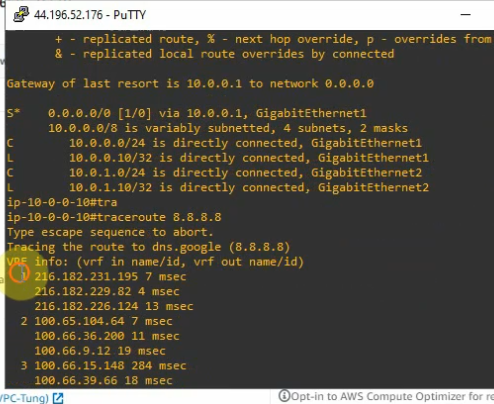
conf t
int g2
ip add 10.0.1.10 255.255.255.0
no shut
exit
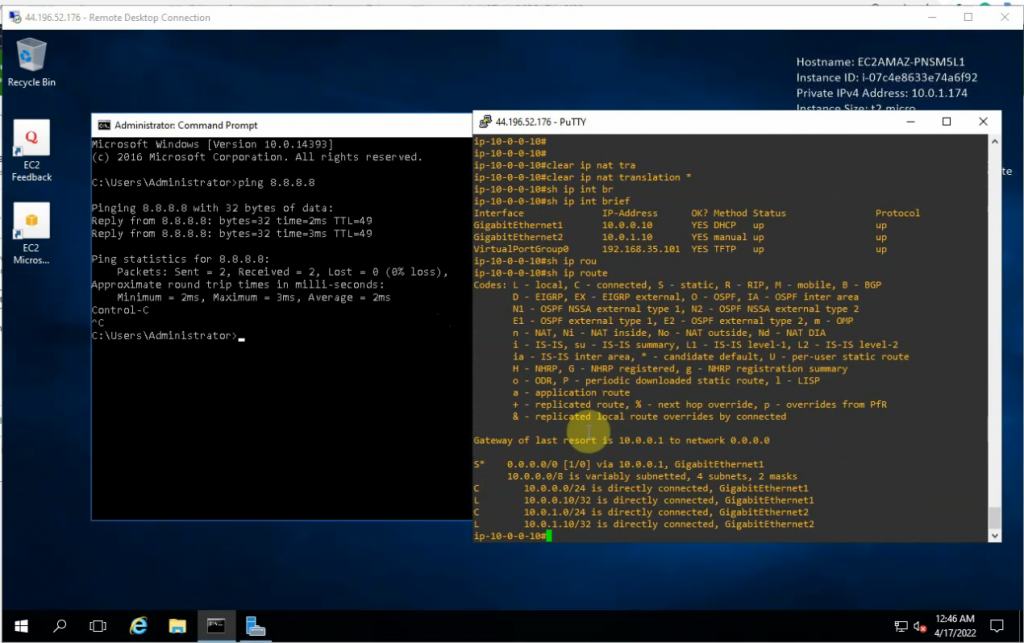
ping 8.8.8.8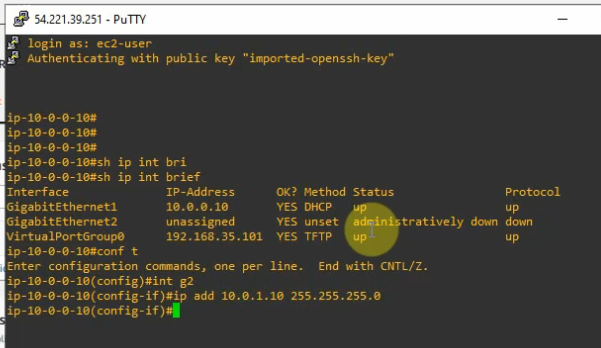
Launches a new Windows 2016 machine to test RDP traffic from the Internet.
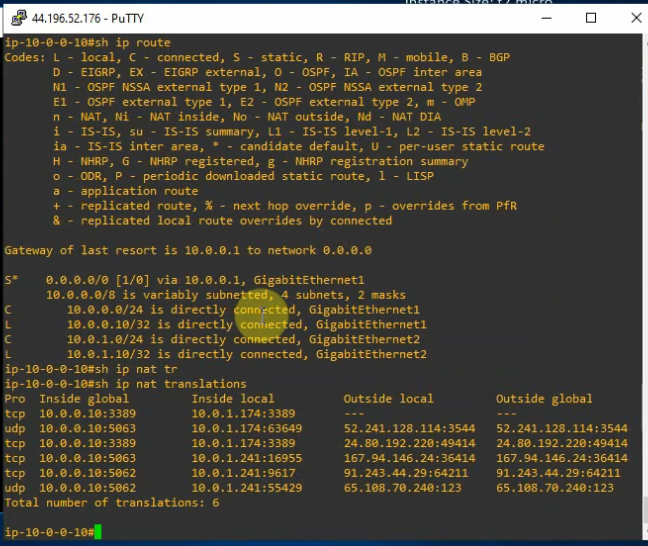
Enable SNAT and DNAT on the Router.
conf t
access-list 1 permit any
# Allow inside to outside
ip nat inside source list 1 interface g1 overload
# Allow outside to Windows server via the RDP service
ip nat inside source static tcp 10.0.1.174 3389 10.0.0.10 3389
int g1
ip nat outside
int g2
ip nat inside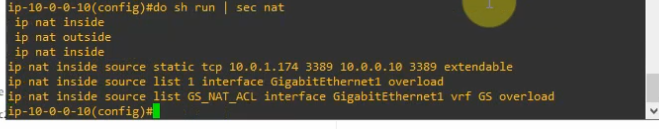
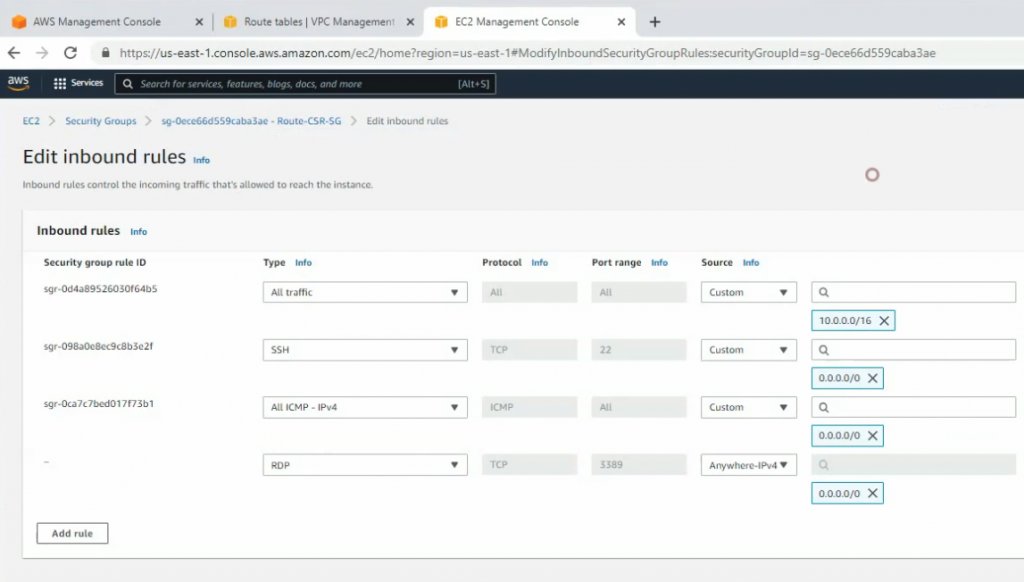
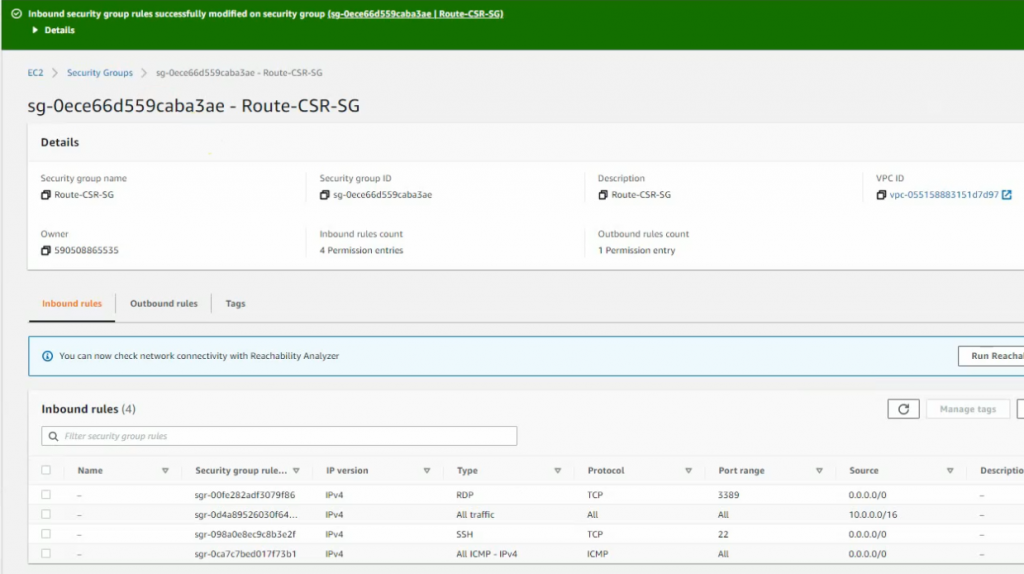
Edit Router CSR Security Group and add RDP service into this group to allow RDP traffic from the Internet.
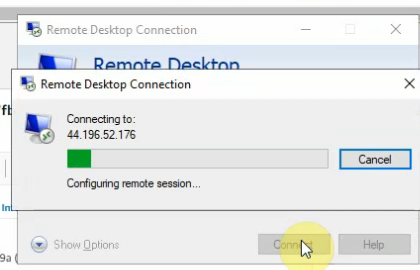
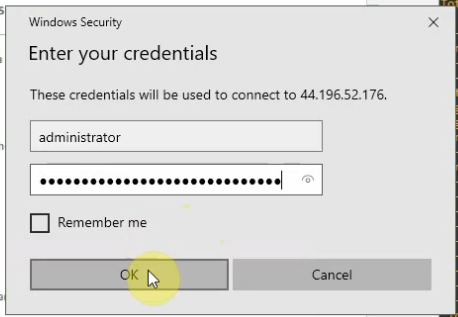
RDP to Elastic IP address of CSR Router.