Wazuh is a free, open-source, and enterprise-ready security monitoring solution for threat detection, integrity monitoring, incident response, and compliance.
Below is a topology to implement Wazuh solution.
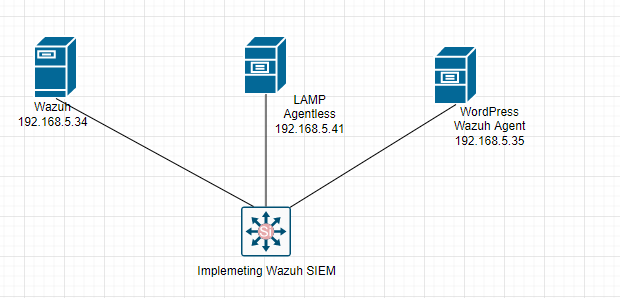
Below are a couple of steps in this lab.
- Install Wazuh on LinuxMint
- Configure Agentless on LAMP server
- Install Agent on WordPress
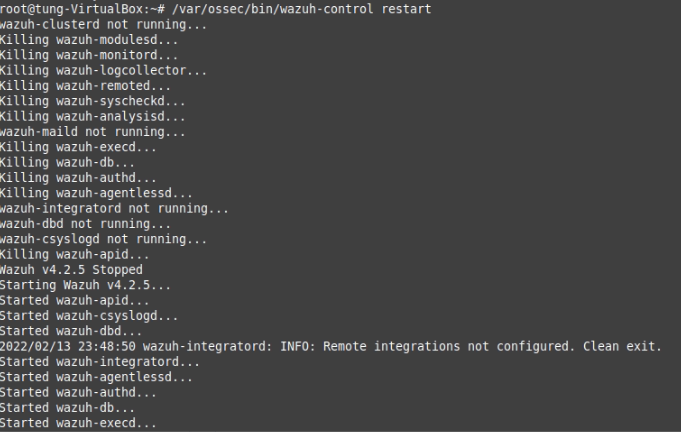
+ Install Wazuh on LinuxMint 20.
Following Wazuh link below to install it into LinuxMint 20
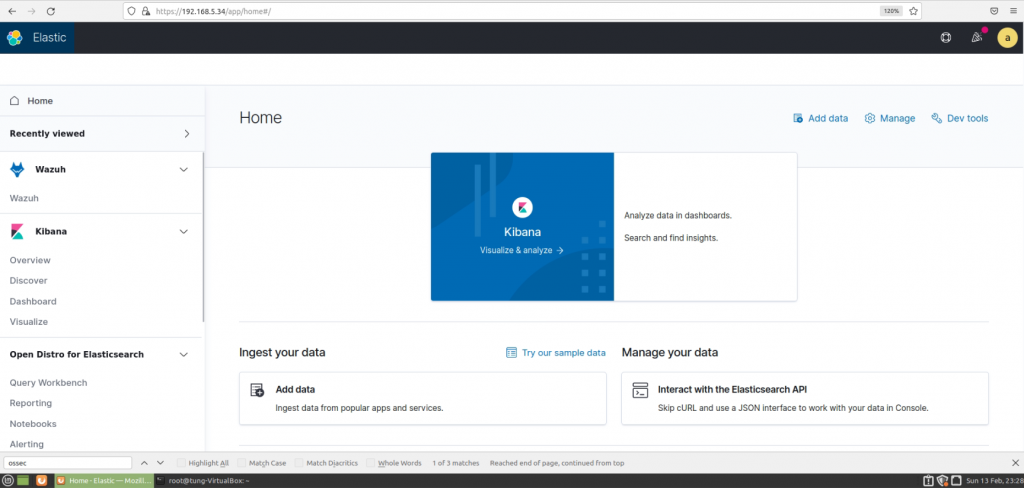
Login to Wazuh management interface.
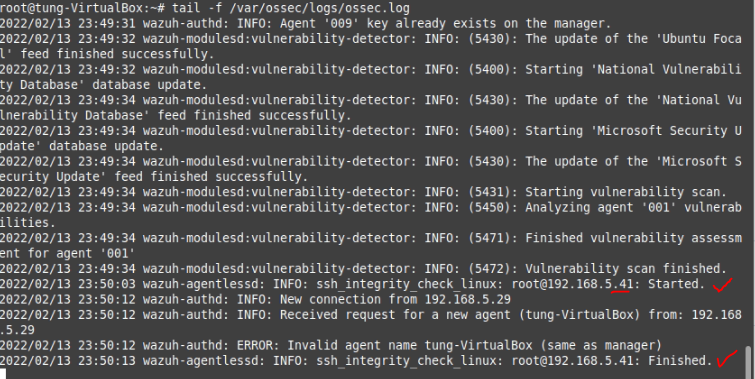
+ Using a link below to Configure Agentless monitoring on Wazuh.
To set up that method of access, firstly you need to create ssh keys for the user ossec which is the account the agentless scripts run.
sudo -u ossec ssh-keygen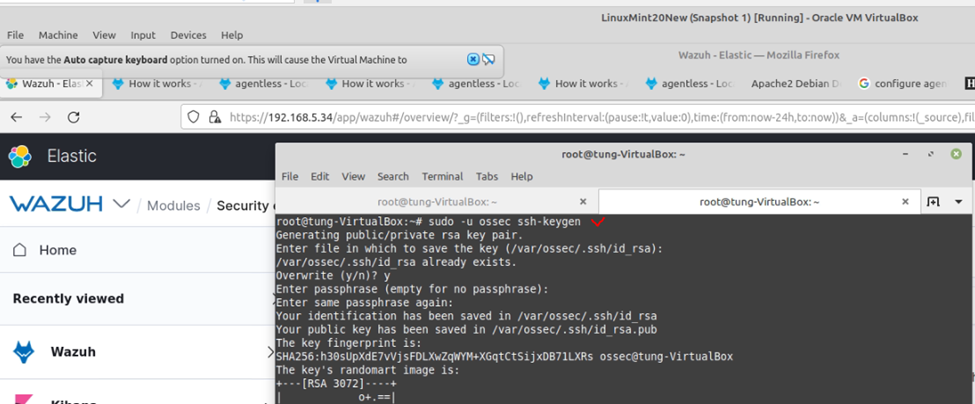
Copy SSH public key to Debian server that you want to monitor via agentless.
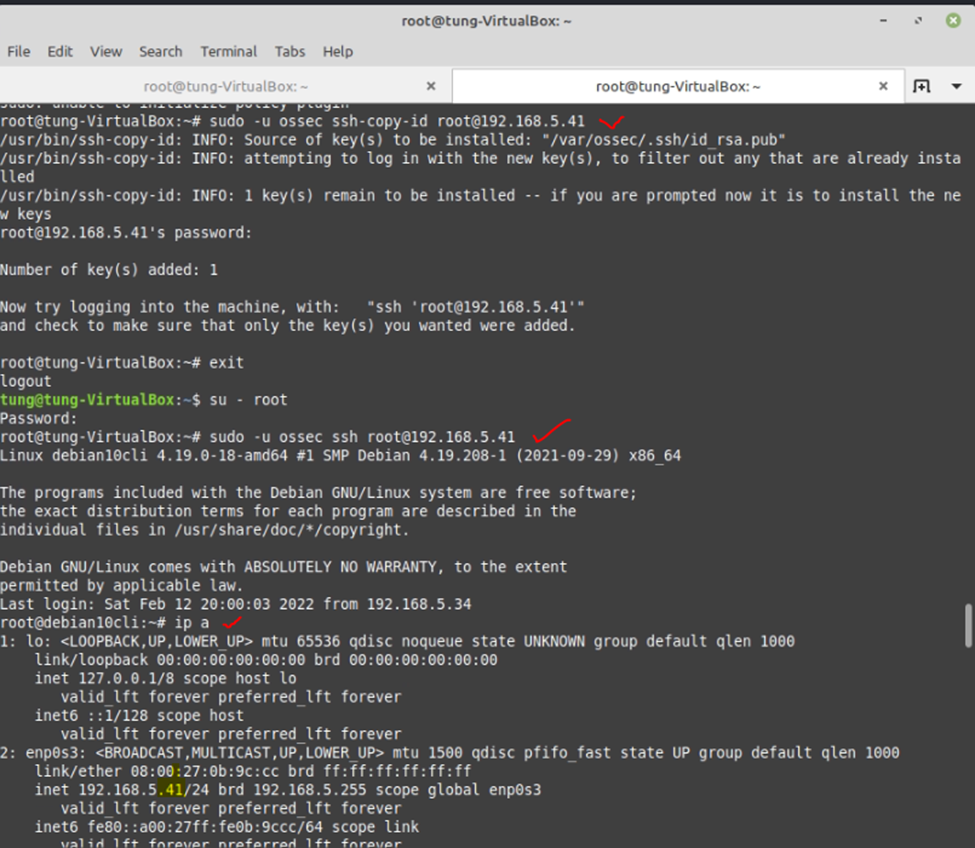
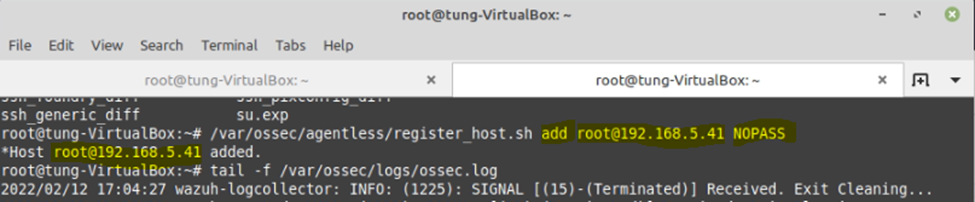
Using the add the option will specify a new device to be added to the manager. “NOPASS” may be entered as the password to use public-key authentication rather than using a password.
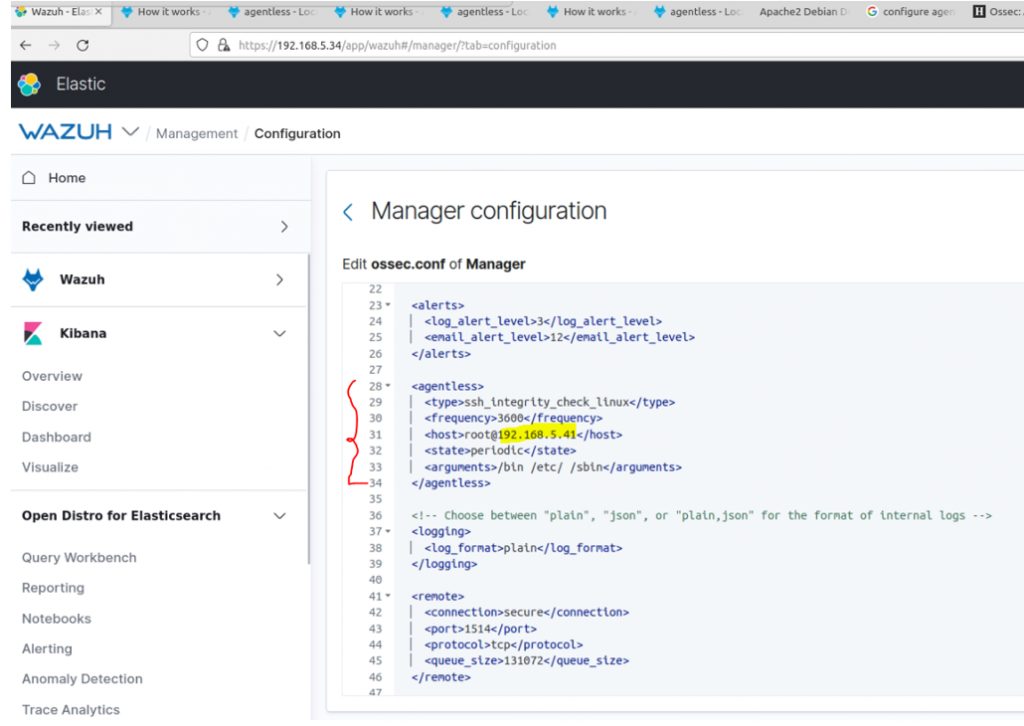
Back to Wazuh management interface and add the code below into ossec.conf file to monitor Linux servers with any changes on /bin / etc and /sbin directory.
<agentless> <type>ssh_integrity_check_linux</type> <frequency>3600</frequency> <host>root@192.168.5.41</host> <state>periodic</state> <arguments>/bin /etc/ /sbin</arguments> </agentless>
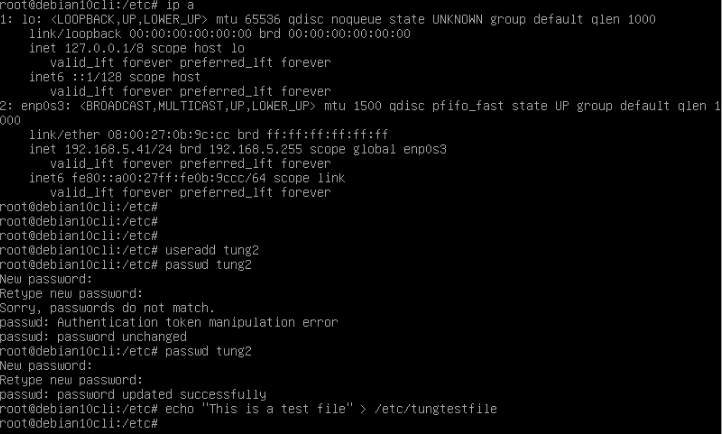
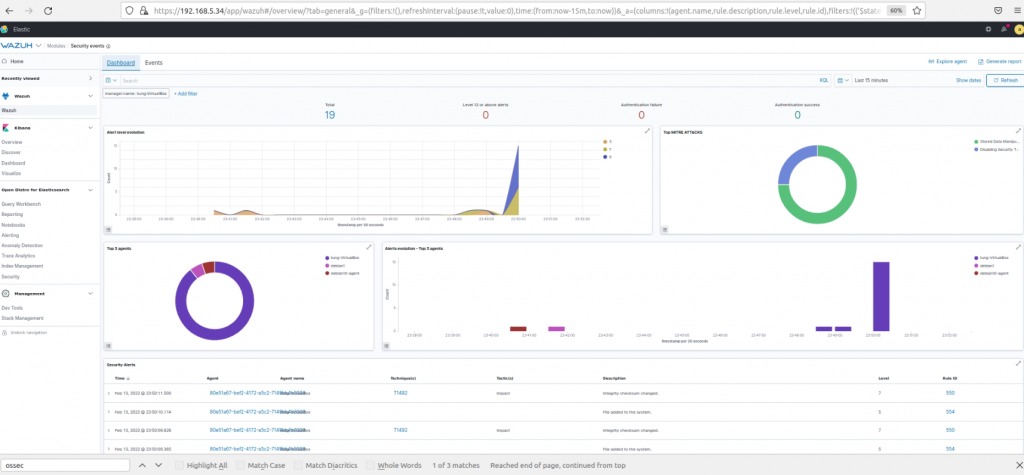
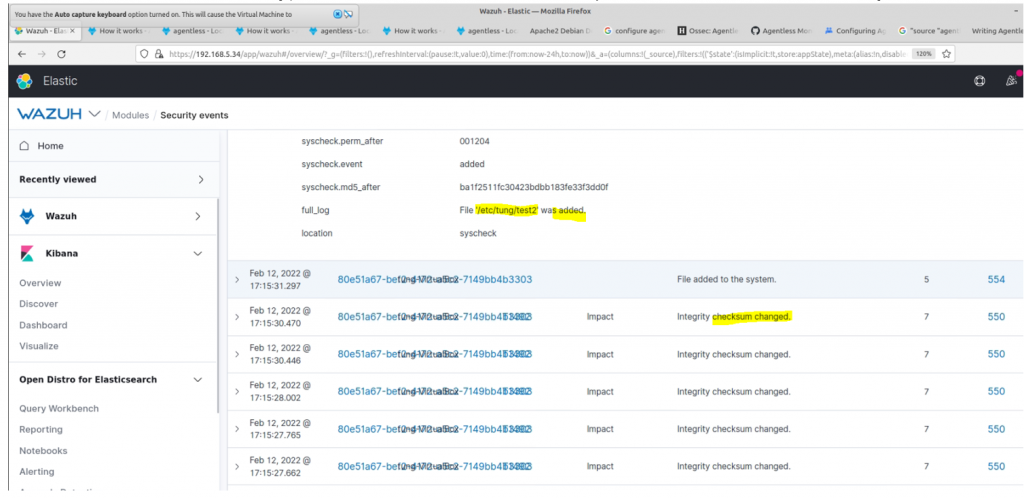
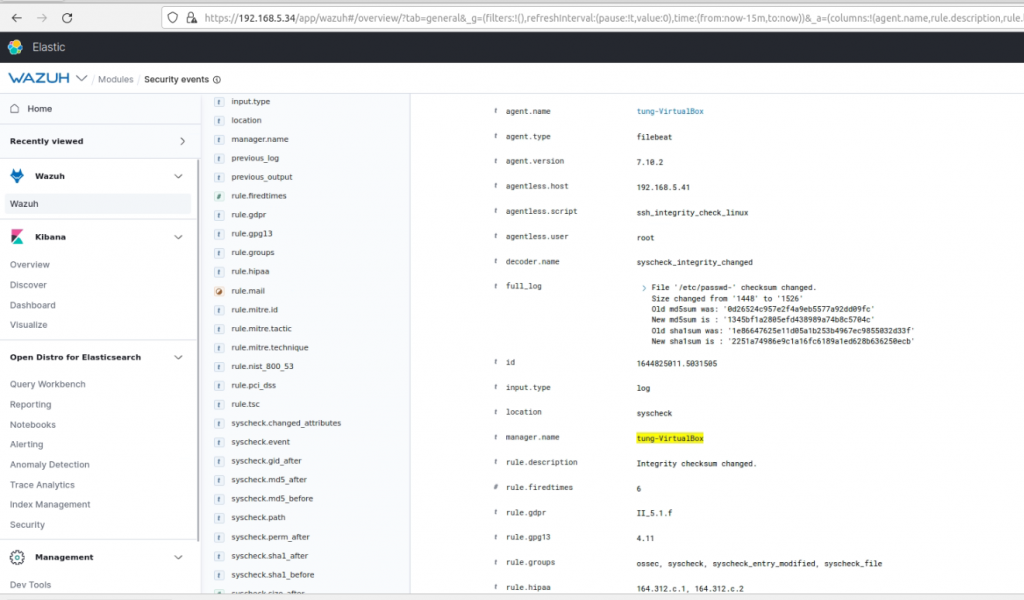
Create a new file under /etc/tung and tung1 user. Security events have been generated on Wazuh from Debian server.
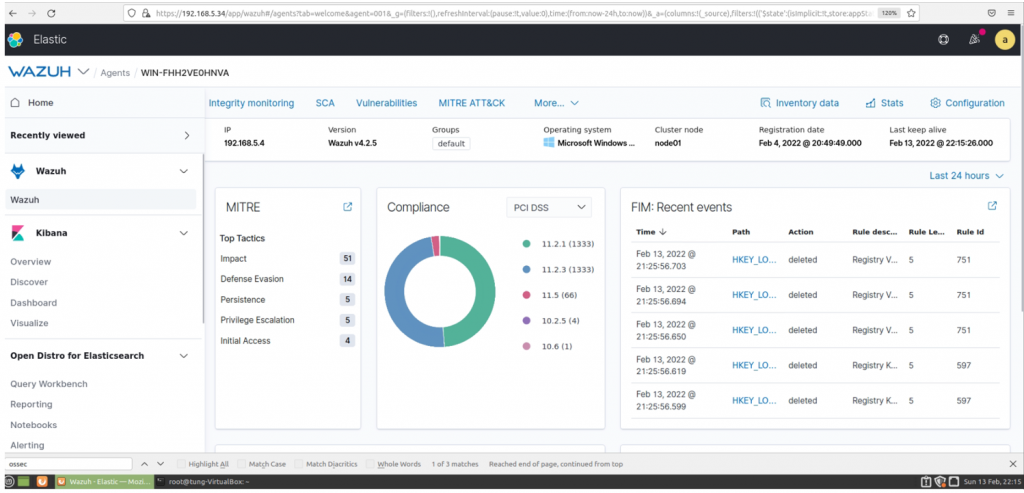
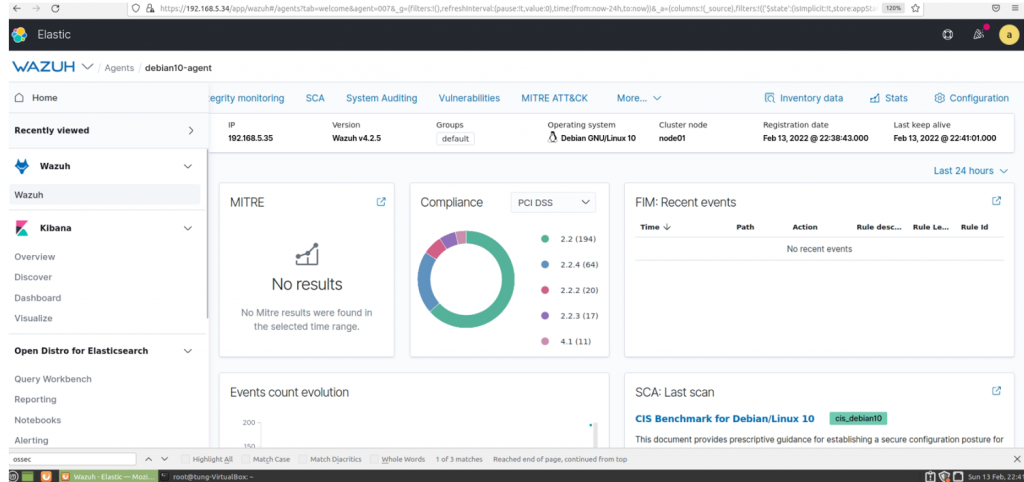
Wazuh Security Dashboard.
+ Install Wazuh agent on Debian server.
Follow the link below to install Wazuh agent.
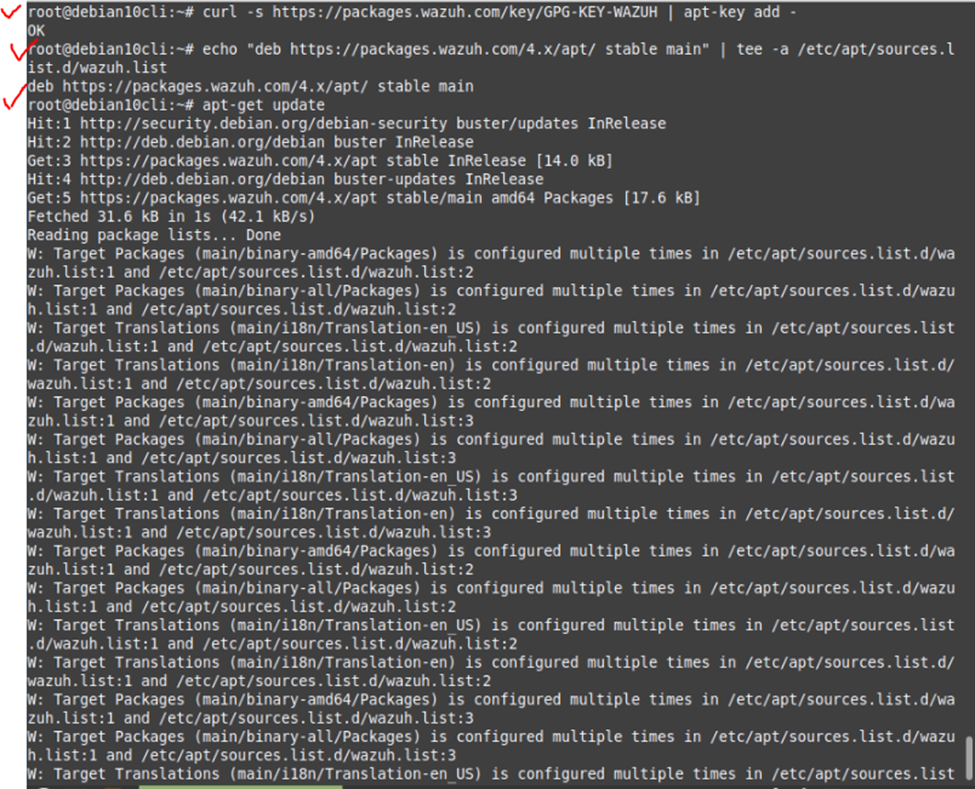
# Add the Wazuh repository
curl -s https://packages.wazuh.com/key/GPG-KEY-WAZUH | apt-key add -
# Add the repository:
echo "deb https://packages.wazuh.com/4.x/apt/ stable main" | tee -a /etc/apt/sources.list.d/wazuh.list
# Update the package information:
apt-get update
# Deploy a Wazuh agent
WAZUH_MANAGER="192.168.5.34" apt-get install wazuh-agent
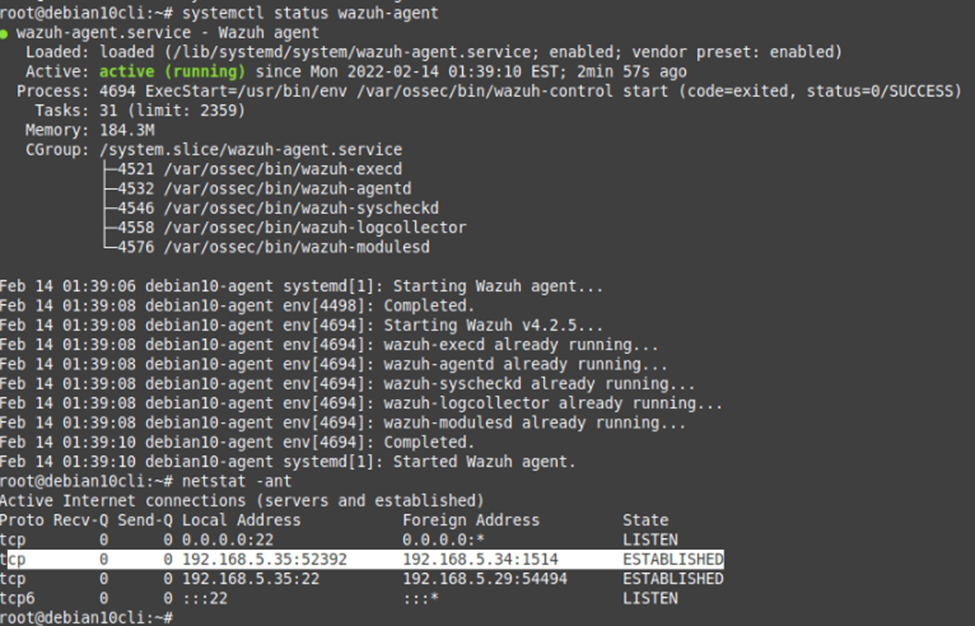
# Enable and start Wazuh
systemctl daemon-reload
systemctl enable wazuh-agent
systemctl start wazuh-agent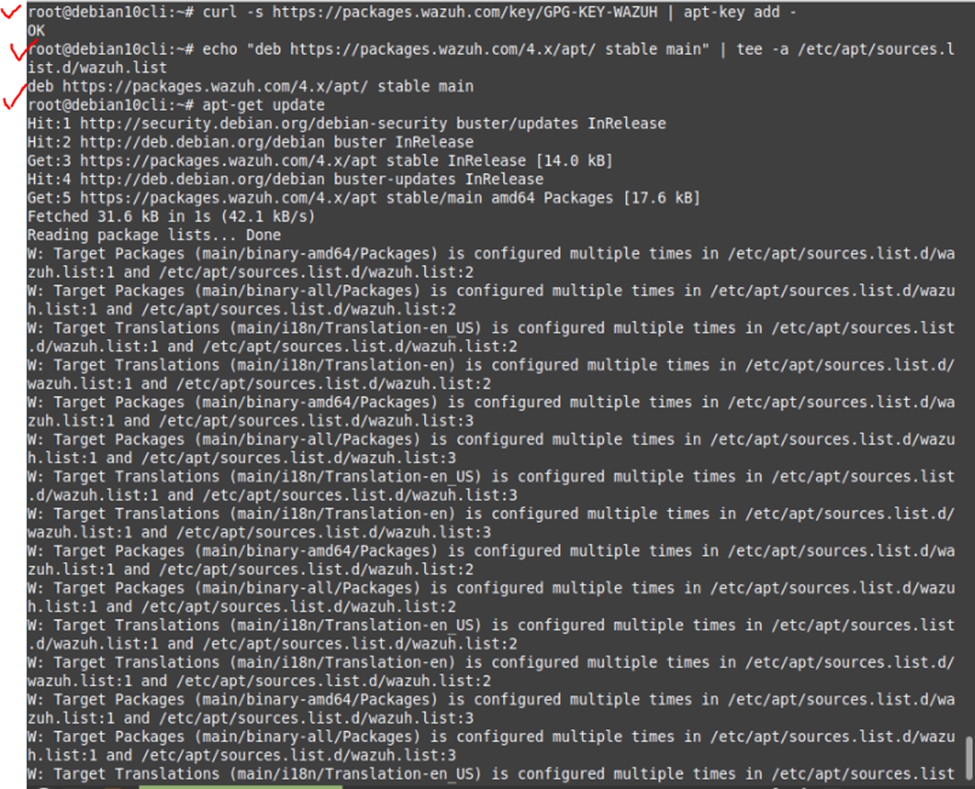
Wazuh agent on Windows machine.