A certificate authority (CA) issues digital certificates that certify the ownership of a public key by the named subject of the certificate.
Below are a couple of steps to install self-signed trusted Root CA on a Linux server.
Step #1: Install openssl
yum install openssl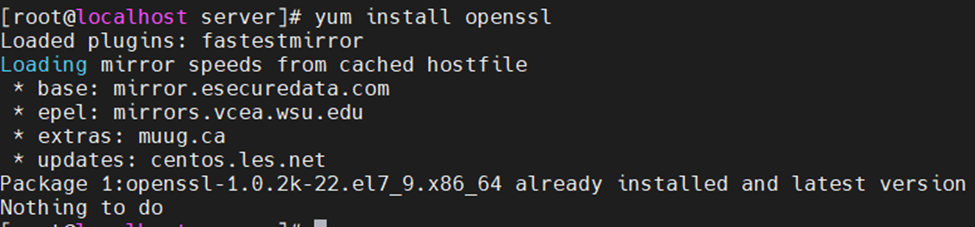
Step #2: Creating your own CA
cd /etc/pki/CA/private/
openssl genrsa -aes128 -out ourCA.key 2048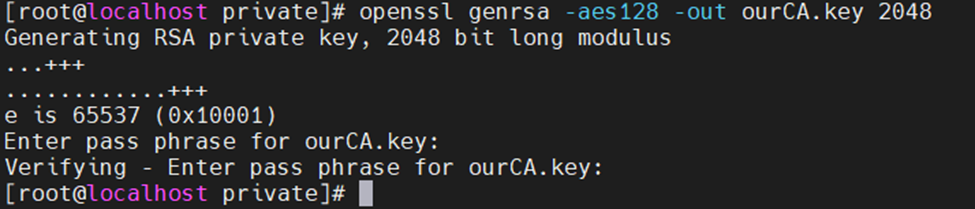
Now create a Certificate Authority (CA) certificate using the ourCA.key.
openssl req -new -x509 -days 1825 -key /etc/pki/CA/private/ourCA.key -out /etc/pki/CA/certs/ourCA.crt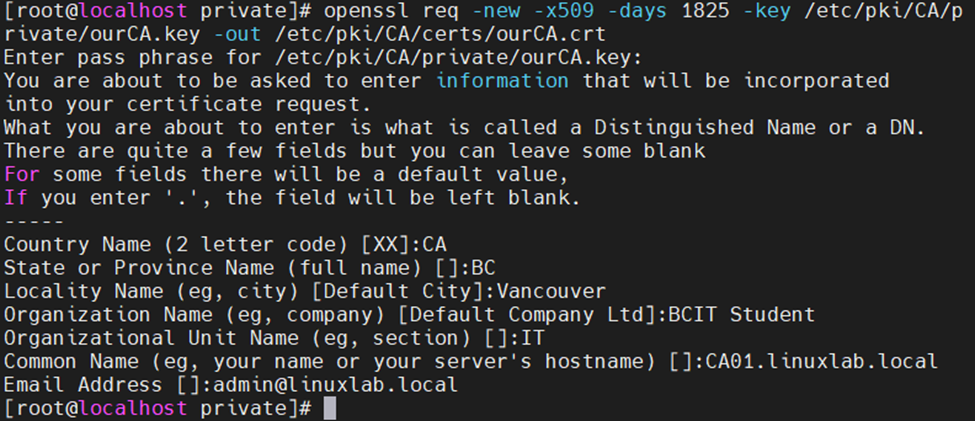
Next, create a local wildcard certificate (*.linuxlab.local) on your own CA.
openssl genrsa -out /etc/pki/tls/private/wildcard-cert.key 2048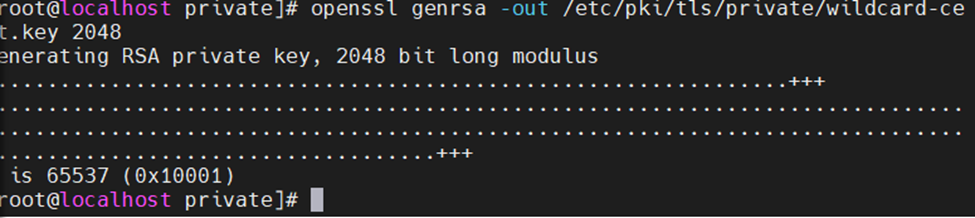
Now, generate a CSR (Certificate Signing Request) for the wildcard cert.
openssl req -new -key /etc/pki/tls/private/wildcard-cert.key -out /etc/pki/tls/wildcard.csr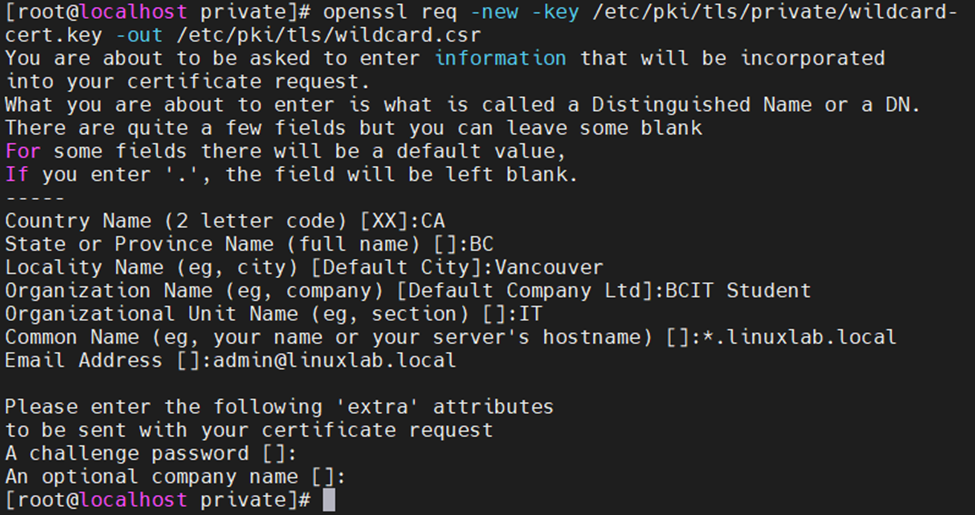
Using WinSCP to download a local Root CA self-signed public-key certificate to a Windows machine. Then, import it into the GPO of the Windows domain or any Windows/Linux/Mac web browser.
